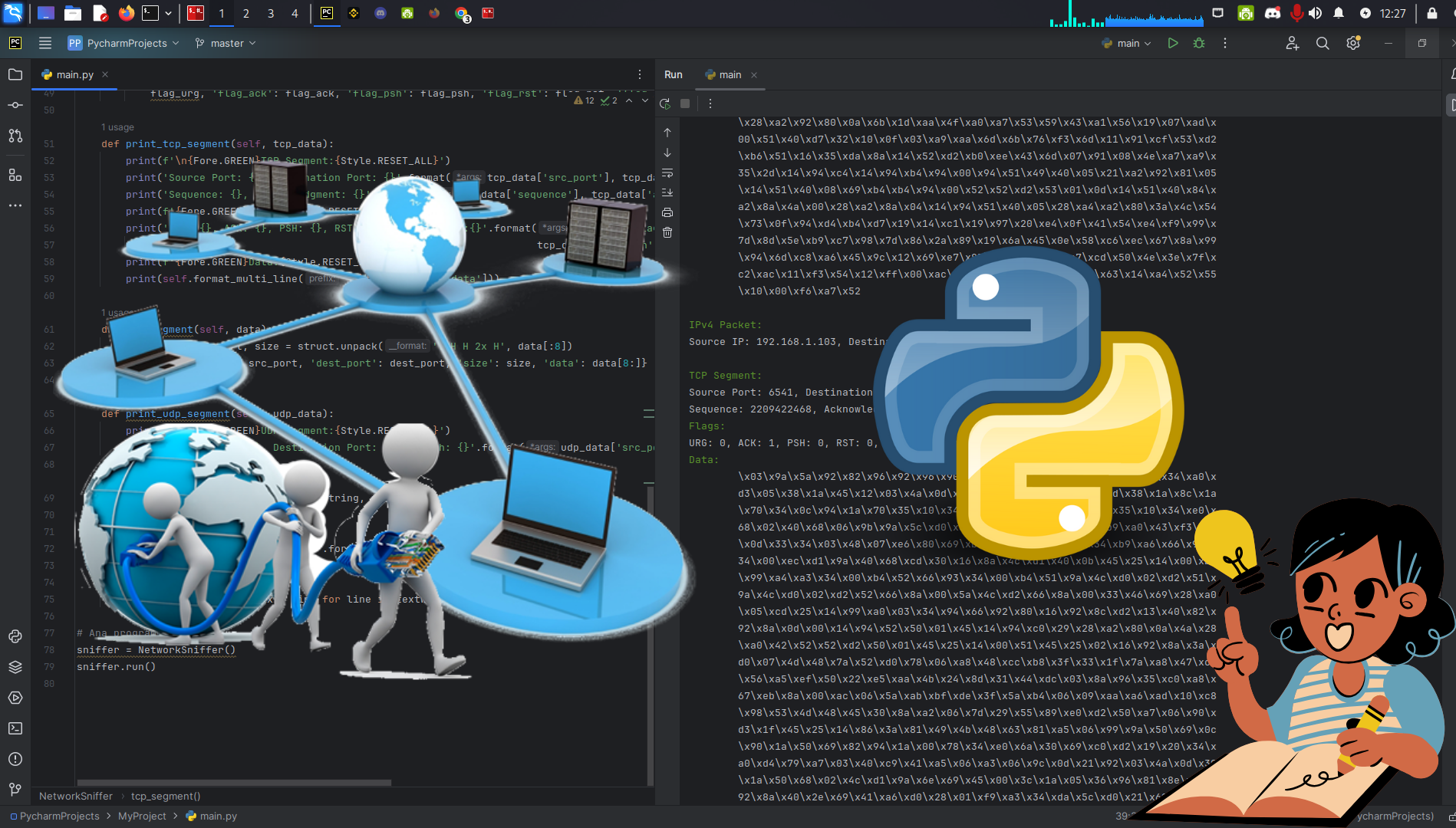
Python TCP/UDP Network Traffic Listener (Part 1)
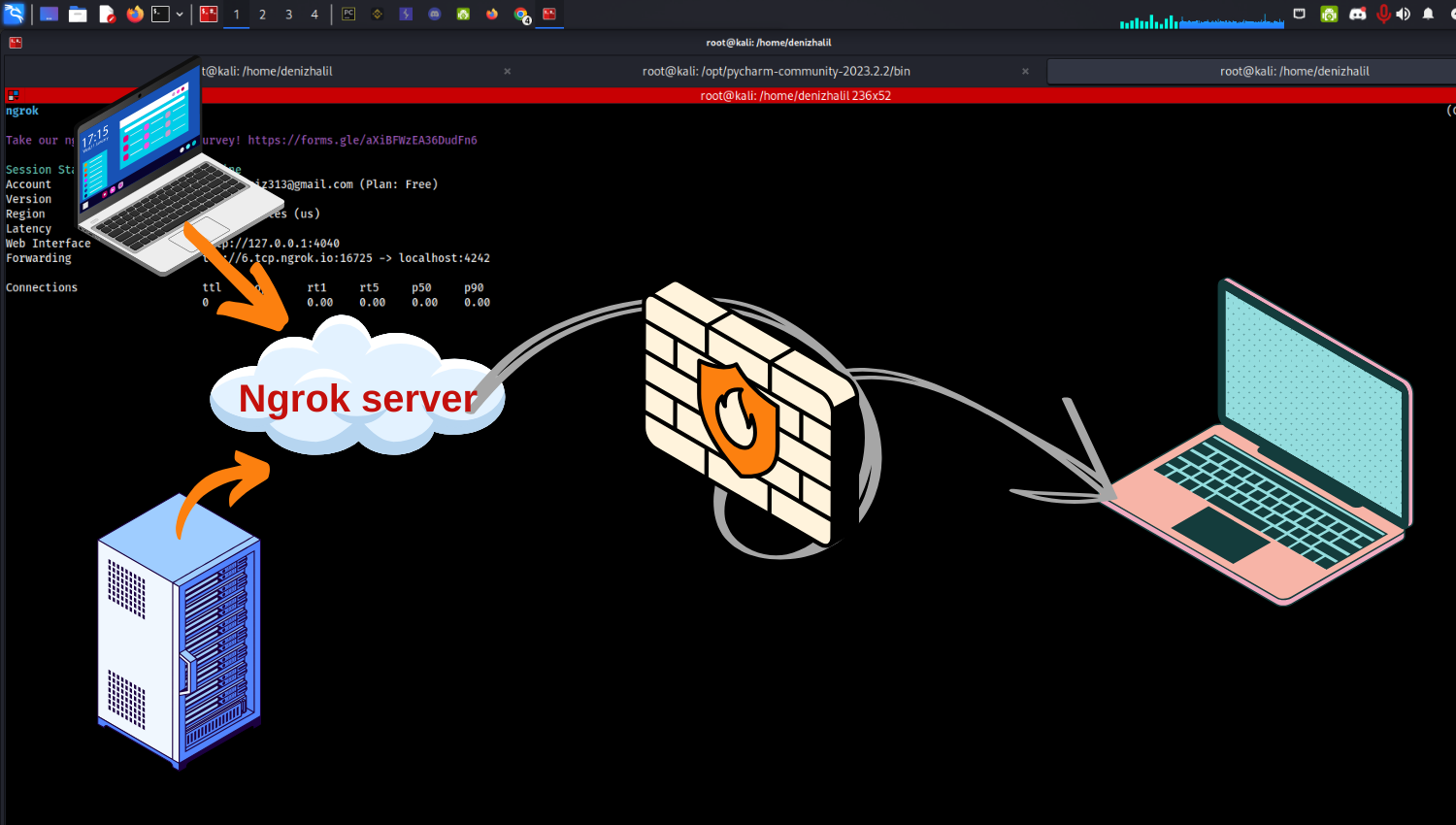
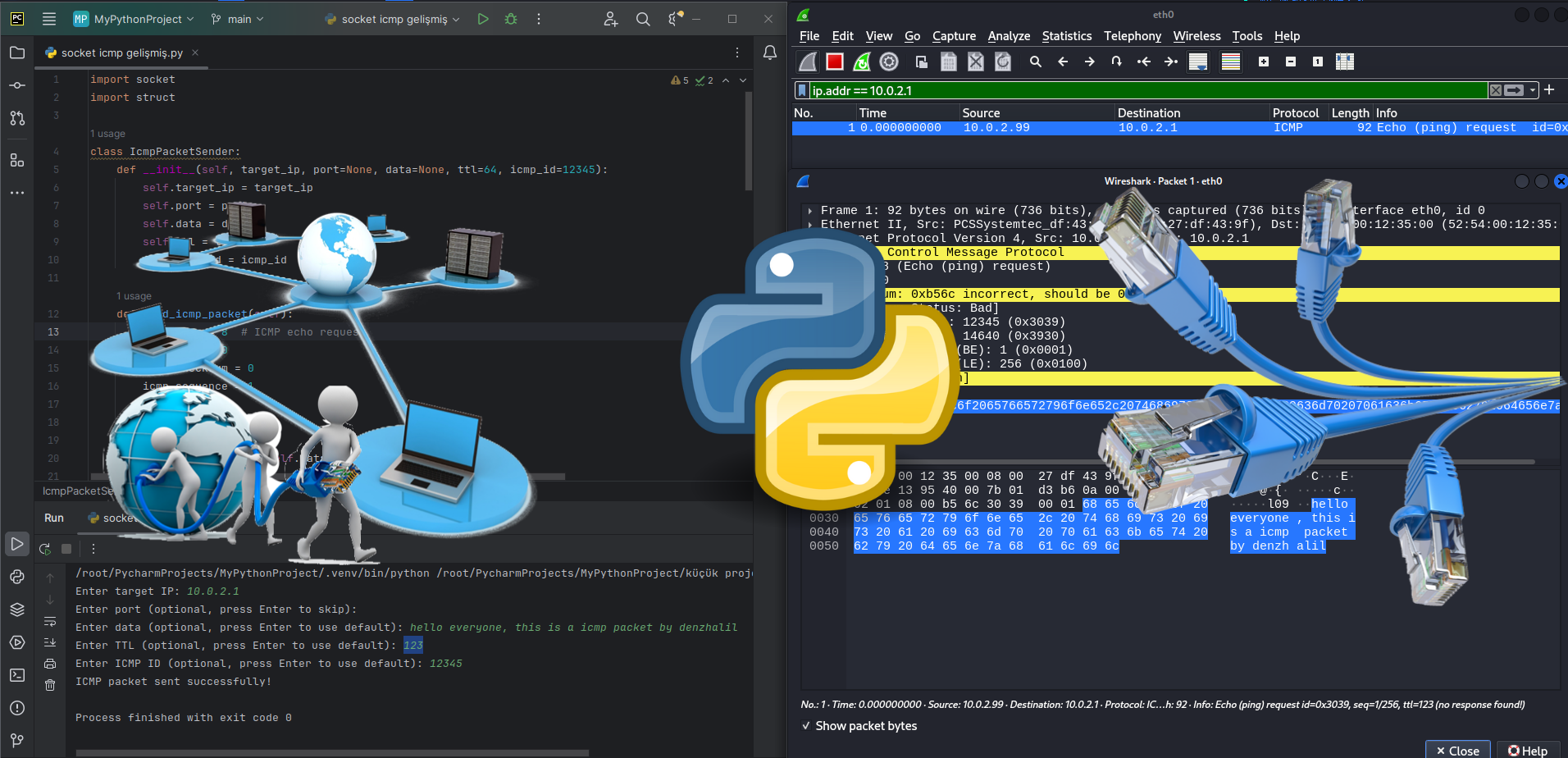
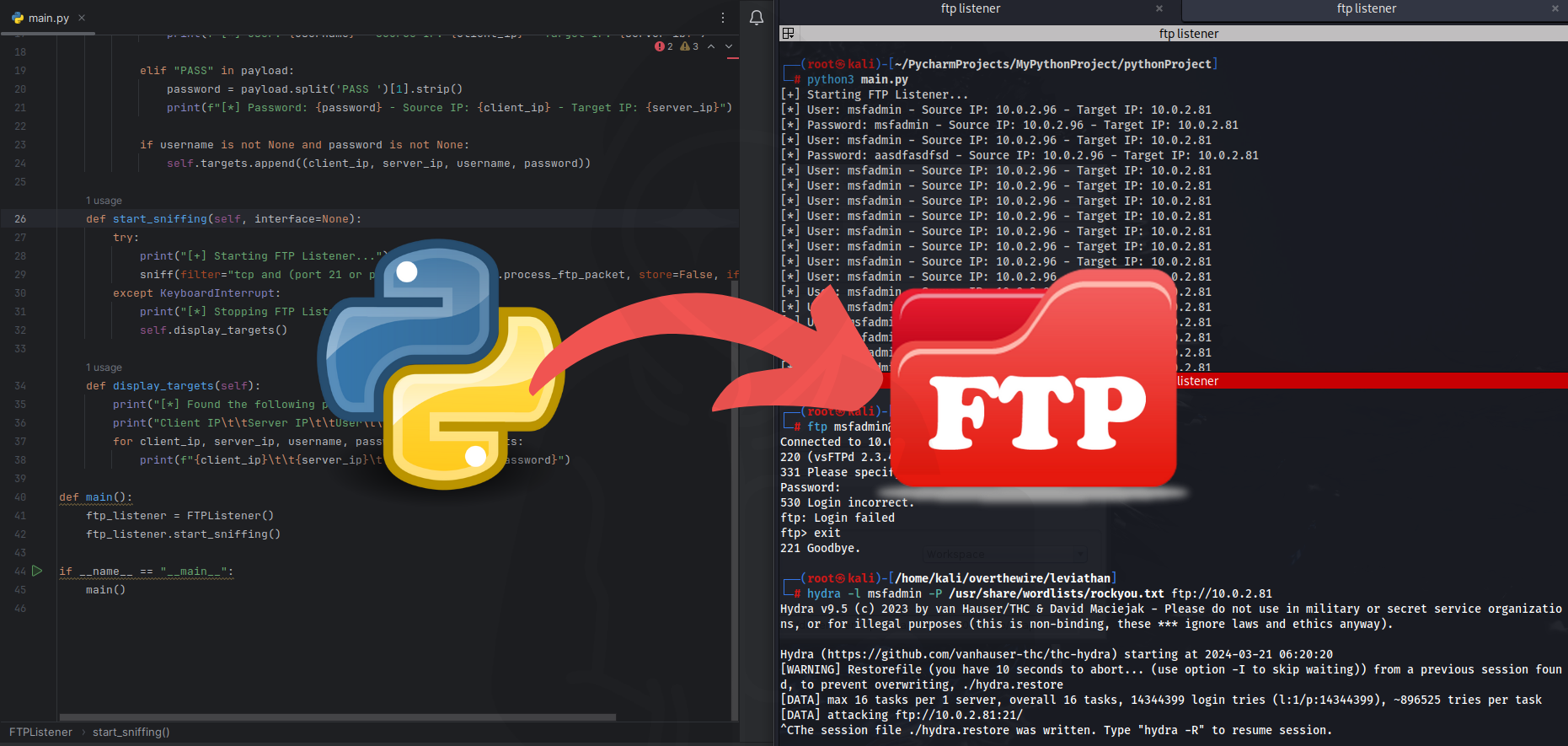
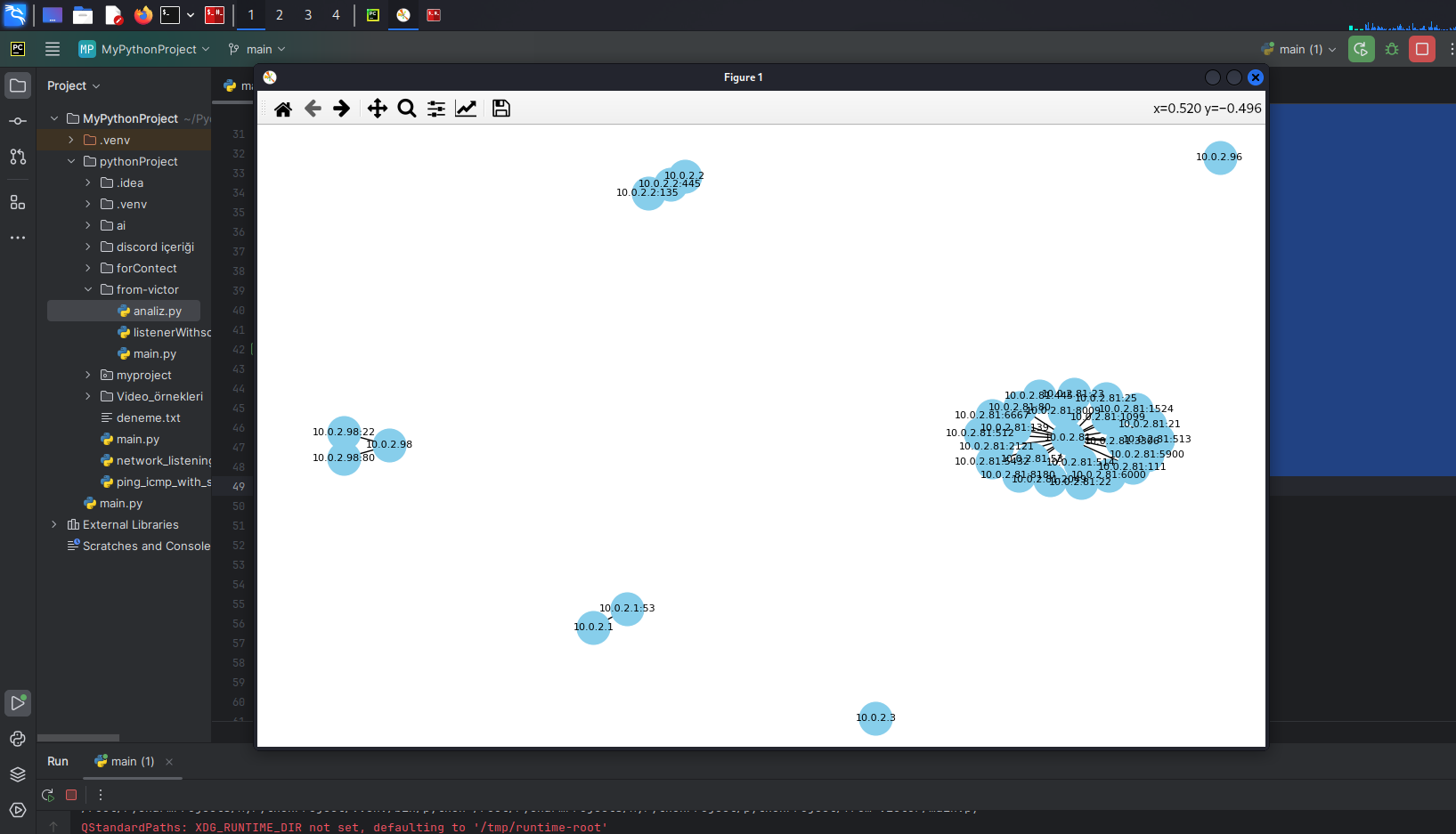
Introduction: Network traffic analysis is an essential part of gaining insights into cybersecurity, monitoring network performance, and understanding network communication. Using a powerful language like Python, we can listen to network traffic, analyze it, and make sense of it. In this article, we’ll learn how to listen to and analyze network traffic using Python. We’ll … Read more