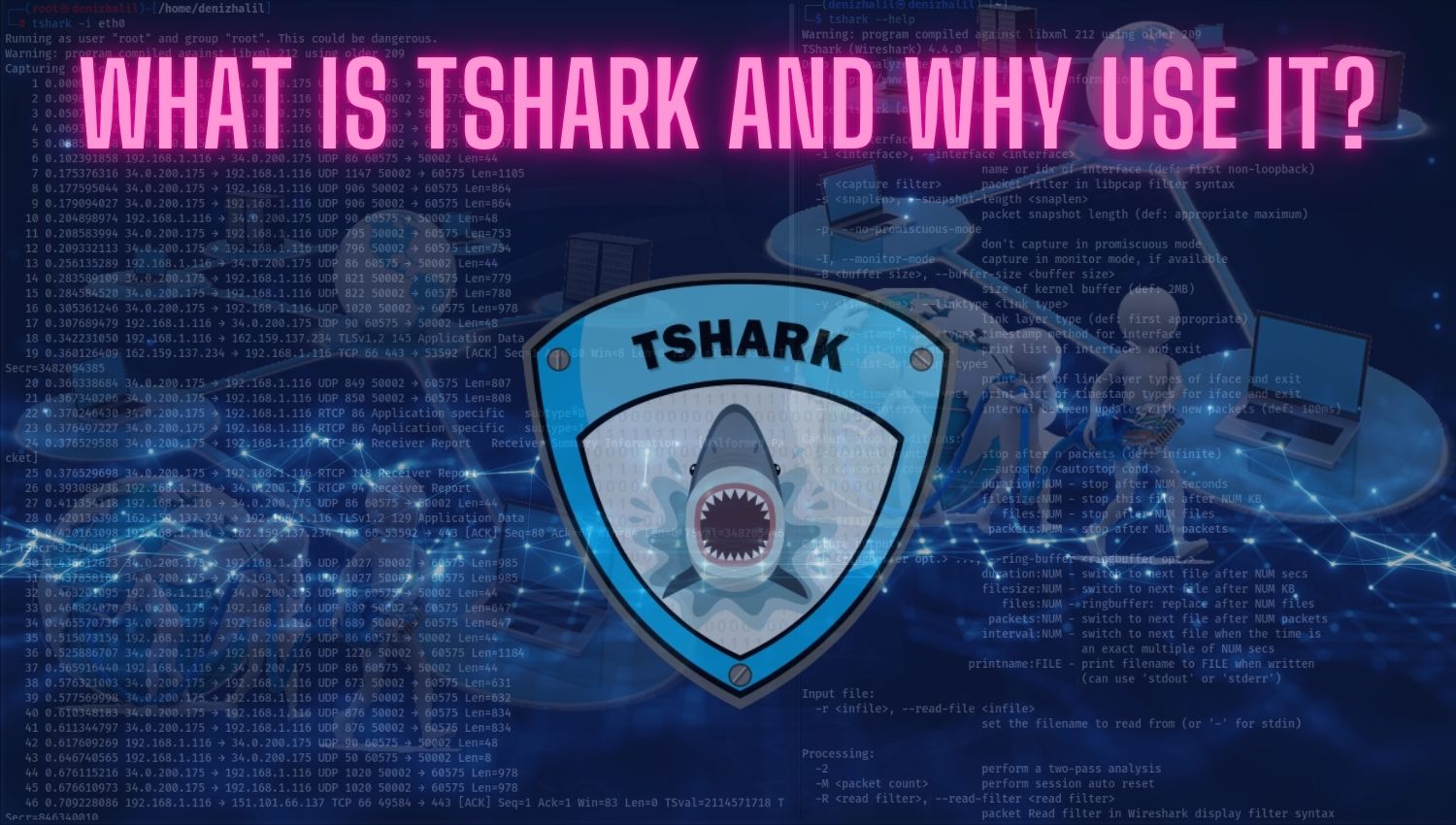
TShark serves as the command-line counterpart to the widely acclaimed Wireshark network analysis tool. While Wireshark offers a user-friendly graphical interface, TShark operates solely through the command line, making it particularly suited for remote or headless server environments where graphical interfaces are impractical or unavailable. With its extensive range of features and robust capabilities, TShark empowers network administrators, security professionals, and system operators to delve deep into network traffic, diagnose issues, detect anomalies, and ensure optimal network performance.
Learning Objectives
- Understand the basic functions and features of TShark.
- Learn how to use TShark for monitoring and analyzing network traffic.
- Gain insight into different usage scenarios.
- Discover how to identify network issues with TShark.
What is TShark and Why is It Popular?
TShark serves as the command-line interface counterpart to Wireshark, one of the most renowned network analysis tools available today. While Wireshark boasts a graphical user interface that simplifies the process of capturing and analyzing network traffic, TShark is designed for environments where such interfaces are impractical or unavailable, such as on remote servers or in headless setups. This command-line tool allows users to capture live network data or analyze previously saved packet captures, providing a detailed view of network traffic.
Its popularity stems from its versatility and powerful features that cater to a wide range of users, including system administrators, security professionals, and network engineers. TShark supports a comprehensive list of network protocols, enabling users to delve deeply into the intricacies of their network traffic. Furthermore, its ability to integrate seamlessly into automation and scripting workflows enhances its utility, allowing for efficient monitoring and analysis without manual intervention. This makes TShark an indispensable asset for those who require robust network analysis capabilities in various operational contexts.
TShark’s Features and Advantages
TShark offers several key features and advantages that contribute to its effectiveness as a network analysis tool:
- Cross-Platform Support: TShark is compatible with multiple operating systems, including Windows, Linux, and macOS. This broad compatibility ensures that users can leverage its capabilities regardless of their preferred platform, making it accessible to a diverse audience of network professionals.
- Wide Protocol Support: The tool supports an extensive range of network protocols, including but not limited to HTTP, FTP, TCP, UDP, and many more. This rich protocol support allows users to capture and analyze traffic across different types of networks and applications, enhancing TShark’s versatility in various networking scenarios.
- Flexible Filtering Options: One of TShark’s standout features is its robust filtering capabilities. Users can apply filters based on specific criteria such as IP addresses, ports, protocols, or even complex expressions. This flexibility enables precise targeting of relevant traffic, making it easier to identify issues or analyze specific data flows within the network.
- Automation Capabilities: Thanks to its command-line nature, TShark can be easily scripted and integrated into automated workflows. This feature is particularly beneficial for system administrators who need to perform regular monitoring or analysis tasks without manual intervention. Automation not only saves time but also reduces the likelihood of human error during routine operations.
- Detailed Analysis Capability: TShark excels in providing comprehensive details about captured packets, including timestamps, protocol information, and other critical data at various layers of the network stack. This depth of information empowers users to perform thorough analyses of their network traffic and diagnose potential issues effectively.
Mastering Scapy: A Comprehensive Guide to Network Analysis
Mastering Network Analysis with Scapy” is not just about learning a tool; it’s about unlocking a deeper understanding of the digital world that surrounds us
-5% $20 on buymeacoffeeThese features collectively make TShark a powerful tool for anyone involved in network management or cybersecurity efforts. Its ability to operate efficiently in diverse environments while offering rich analytical capabilities positions it as a vital resource for professionals seeking to maintain optimal network performance and security.
Usage Examples

- Basic Packet Capture: Capturing all traffic packets on a network interface.
$ tshark -i eth0- Filtered Capture: Capturing traffic packets filtering by a specific IP address.
$ tshark -i eth0 -f "src host 192.168.1.1"- Filtering by Protocol: Capturing only HTTP traffic packets.
$ tshark -Y http- Saving Packets: Saving captured packets to a file.
$ tshark -w captured_traffic.pcap- Reading Packets from File: Reading a previously saved packet file.
$ tshark -r captured_traffic.pcap- Statistics: Displaying network traffic statistics (e.g., total packet count).
$ tshark -z io,stat,0- TCP Stream Analysis: Analyzing the details of a TCP stream.
$ tshark -q -z follow,tcp,ascii,0- Monitoring DNS Queries: Monitoring DNS queries and responses.
$ tshark -Y dns- SSL/TLS Traffic Analysis: Examining encrypted SSL/TLS traffic packets.
$ tshark -Y ssl- Email Traffic Analysis: Analyzing email traffic using SMTP, POP3, or IMAP protocols.
$ tshark -Y smtp || pop || imap- Analyzing VoIP Calls: Analyzing VoIP calls using SIP and RTP protocols.
$ tshark -Y sip || rtp- Filtering by MAC Address: Capturing traffic packets related to a specific MAC address.
$ tshark -Y eth.addr==00:11:22:33:44:55- Filtering by Packet Sizes: Capturing packets within a certain size range.
$ tshark -Y "frame.len >= 100 && frame.len <= 200"- Detecting Network Errors: Detecting faulty packets (e.g., checksum errors).
$ tshark -Y tcp.analysis.flags- Temporal Traffic Analysis: Examining traffic packets in a specific time range.
tshark -Y "frame.time >= Jan 1, 2023 00:00:00 && frame.time <= Jan 1, 2023 23:59:59"These examples demonstrate how powerful and flexible TShark is in network analysis and troubleshooting. When used correctly, it can provide in-depth insights to network administrators and security professionals, making their jobs easier.
Mastering Python for Ethical Hacking: A Comprehensive Guide to Building 50 Hacking Tools
Let’s embark on this journey together, where you will learn to use Python not just as a programming language, but as a powerful weapon in the fight against cyber threats
-5% $25 on buymeacoffeeConclusion
TShark is a powerful tool for network analysis and monitoring. Its command-line interface makes it particularly useful in environments without graphical interfaces or for automated tasks. With its wide range of protocol support and filtering options, TShark allows in-depth analysis of network traffic. As a vital tool for network administrators and security experts, TShark helps improve network performance, detect issues, and prevent potential security breaches.