Responder Tool for Network Credential Capture in Active Directory
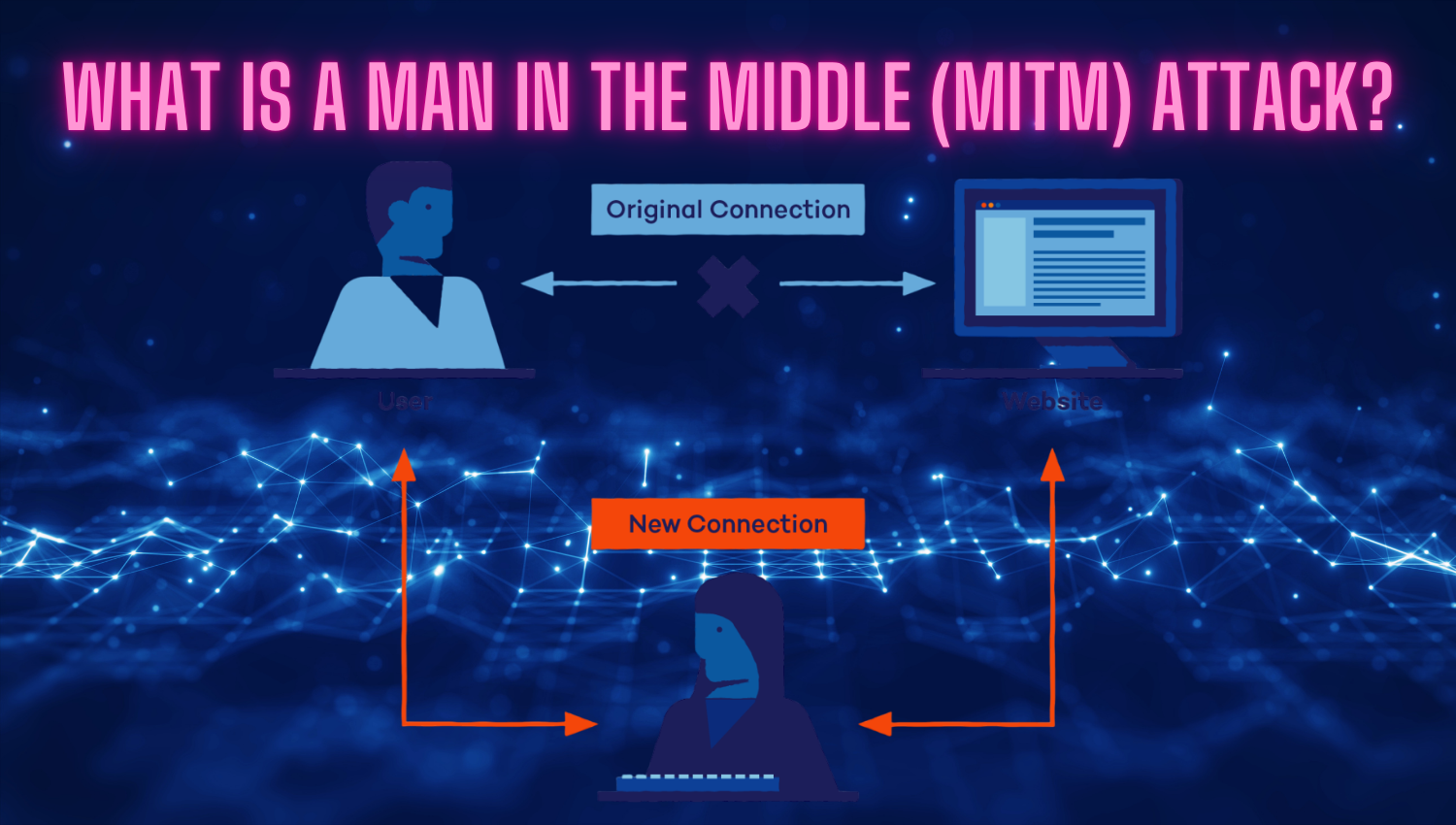
Introduction Responder is a powerful, open-source Python-based penetration testing tool that directly targets the fundamental weaknesses present in Windows network environments. By manipulating how machines resolve hostnames when DNS lookups fail, Responder intercepts broadcast name resolution requests—specifically those using LLMNR (Link-Local Multicast Name Resolution), NBT-NS (NetBIOS Name Service), and MDNS (Multicast DNS) protocols—and impersonates legitimate network resources. This approach lets attackers seamlessly perform man-in-the-middle (MITM) attacks: when victims