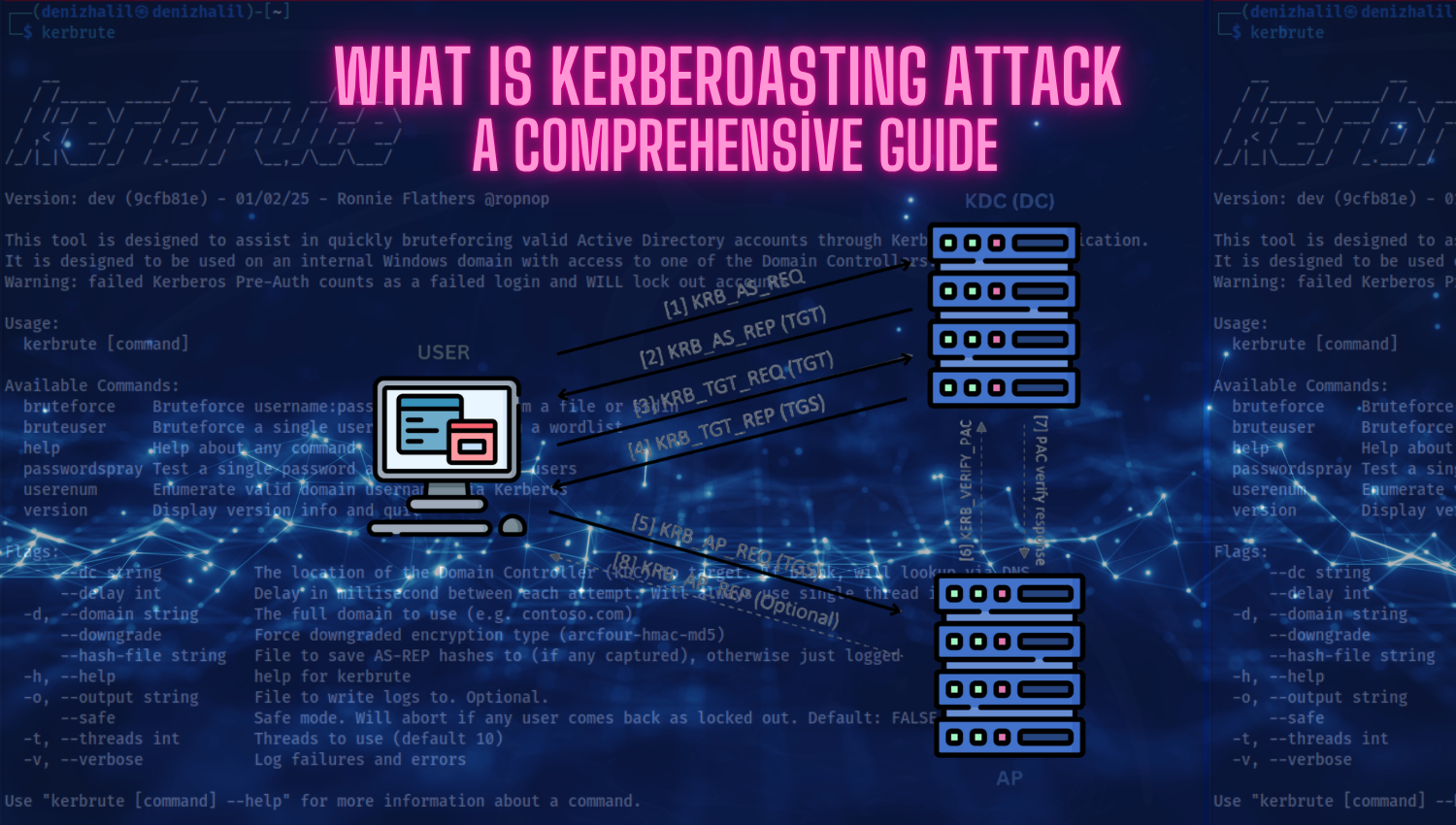
What is Kerberoasting Attack – Kerberoasting: A Comprehensive Guide
Introduction Kerberoasting has emerged as one of the most prevalent attack techniques targeting service accounts in modern Windows networks. Its effectiveness stems from the way the Kerberos authentication protocol operates: service tickets are encrypted using the hash of the target account’s password. Attackers with even low-level domain access can exploit this feature to request service tickets for accounts