Introduction
In the dynamic world of network security and analysis, tools that offer versatility and powerful features are highly sought after. One such tool, hping3, stands out for its robustness and multifaceted capabilities.
What is Hping3
Hping3 is an advanced network packet crafting and analysis tool. It’s an evolution of its predecessor, hping2, and is used for testing firewalls, network performance, port scanning, and network auditing. Hping3 works at a lower level compared to other packet crafting tools, providing users with the flexibility to manipulate different aspects of TCP/IP protocols.
Why Hping3?
The significance of hping3 lies in its ability to craft custom TCP/IP packets and send them to a specific target, allowing users to test network rules, conduct security audits, and simulate network behavior. This level of control and customization is invaluable in diagnosing network issues and testing security systems.
Features and Usage of Hping3
Hping3 offers a multitude of functionalities, making it a versatile tool for network testing and security. Here’s a brief cheat sheet on how to use hping3 for various purposes: (Scapy: A Powerful Tool for Network Analysis and Security)
1. Help Menu
- Command:
hping3 --help
$ hping3 --help
usage: hping3 host [options]
-h --help show this help
-v --version show version
-c --count packet count
-i --interval wait (uX for X microseconds, for example -i u1000)
--fast alias for -i u10000 (10 packets for second)
--faster alias for -i u1000 (100 packets for second)
--flood sent packets as fast as possible. Don't show replies.
-n --numeric numeric output
-q --quiet quiet
-I --interface interface name (otherwise default routing interface)
-V --verbose verbose mode
-D --debug debugging info
-z --bind bind ctrl+z to ttl (default to dst port)
-Z --unbind unbind ctrl+z
--beep beep for every matching packet received
Mode
default mode TCP
-0 --rawip RAW IP mode
-1 --icmp ICMP mode
-2 --udp UDP mode
-8 --scan SCAN mode.
Example: hping --scan 1-30,70-90 -S www.target.host
-9 --listen listen mode
IP
-a --spoof spoof source address
--rand-dest random destionation address mode. see the man.
--rand-source random source address mode. see the man.
-t --ttl ttl (default 64)
-N --id id (default random)
-W --winid use win* id byte ordering
-r --rel relativize id field (to estimate host traffic)
-f --frag split packets in more frag. (may pass weak acl)
-x --morefrag set more fragments flag
-y --dontfrag set don't fragment flag
-g --fragoff set the fragment offset
-m --mtu set virtual mtu, implies --frag if packet size > mtu
-o --tos type of service (default 0x00), try --tos help
-G --rroute includes RECORD_ROUTE option and display the route buffer
--lsrr loose source routing and record route
--ssrr strict source routing and record route
-H --ipproto set the IP protocol field, only in RAW IP mode
ICMP
-C --icmptype icmp type (default echo request)
-K --icmpcode icmp code (default 0)
--force-icmp send all icmp types (default send only supported types)
--icmp-gw set gateway address for ICMP redirect (default 0.0.0.0)
--icmp-ts Alias for --icmp --icmptype 13 (ICMP timestamp)
--icmp-addr Alias for --icmp --icmptype 17 (ICMP address subnet mask)
--icmp-help display help for others icmp options
UDP/TCP
-s --baseport base source port (default random)
-p --destport [+][+]<port> destination port(default 0) ctrl+z inc/dec
-k --keep keep still source port
-w --win winsize (default 64)
-O --tcpoff set fake tcp data offset (instead of tcphdrlen / 4)
-Q --seqnum shows only tcp sequence number
-b --badcksum (try to) send packets with a bad IP checksum
many systems will fix the IP checksum sending the packet
so you'll get bad UDP/TCP checksum instead.
-M --setseq set TCP sequence number
-L --setack set TCP ack
-F --fin set FIN flag
-S --syn set SYN flag
-R --rst set RST flag
-P --push set PUSH flag
-A --ack set ACK flag
-U --urg set URG flag
-X --xmas set X unused flag (0x40)
-Y --ymas set Y unused flag (0x80)
--tcpexitcode use last tcp->th_flags as exit code
--tcp-mss enable the TCP MSS option with the given value
--tcp-timestamp enable the TCP timestamp option to guess the HZ/uptime
Common
-d --data data size (default is 0)
-E --file data from file
-e --sign add 'signature'
-j --dump dump packets in hex
-J --print dump printable characters
-B --safe enable 'safe' protocol
-u --end tell you when --file reached EOF and prevent rewind
-T --traceroute traceroute mode (implies --bind and --ttl 1)
--tr-stop Exit when receive the first not ICMP in traceroute mode
--tr-keep-ttl Keep the source TTL fixed, useful to monitor just one hop
--tr-no-rtt Don't calculate/show RTT information in traceroute mode
ARS packet description (new, unstable)
--apd-send Send the packet described with APD (see docs/APD.txt)2. Basic Command Structure
Linux Basics for Hackers
Linux Basics for Hackers: Getting Started with Networking, Scripting, and Security in Kali
-49% $20.49 on AmazonThe basic syntax for using hping3 is hping3 [options] target, where target can be an IP address or a hostname.
- Basic Command:
hping3 [options] targettarget: Can be an IP address or hostname.
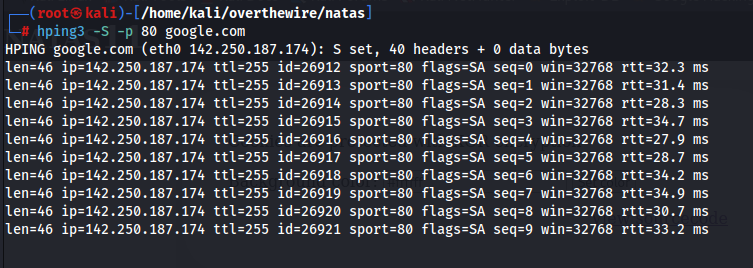
3. Sending TCP SYN Packets
- Command:
hping3 -S -p 80 target-S: SYN packet.-p: Target port number.
4. Sending ICMP Echo Requests
- Command:
hping3 -1 target-1: Indicates ICMP mode.
5. Sending UDP Packets
- Command:
hping3 --udp -p 53 target--udp: UDP packet.-p: Target port number.
6. Sending ARP Requests
- Command:
hping3 --arping target--arping: Pings using the ARP protocol.
7. Conducting Flood Attacks
Mastering Scapy: A Comprehensive Guide to Network Analysis
you will find yourself equipped with the skills to analyze, diagnose, and even manipulate network traffic. This book aims to transform you from a passive observer to an active participant in the digital conversation that occurs ceaselessly in the network wires and airwaves around us
-10% $10 on buymeacoffee- WARNING: These commands should only be used for testing purposes on networks where you have permission.
- Command:
hping3 --flood -S -p 80 target--flood: Speeds up packet sending.-S: SYN packet.-p: Target port number.
8. Setting Packet Size
- Command:
hping3 -S -p 80 -d 120 target-d: Packet size (in bytes).
9. Setting Time Between Packets
- Command:
hping3 -S -p 80 --fast target--fast: Reduces packet sending interval (10 packets/second).
10. Discovering Network Gateway
- Command:
hping3 --traceroute -V -1 target--traceroute: Shows the path the packet takes.-V: Verbose output mode.-1: ICMP mode.
11. Saving to File
- Command:
hping3 -S -p 80 target --safe -I eth0 > record.txt--safe: Safe mode (random IP addresses).-I eth0: Network interface to use.> record.txt: Saves output to a file.
12. Creating a Custom Packet
- Command:
hping3 -S -p 80 -E file.txt -d 100 target-E file.txt: File from which to read packet content.-d 100: Packet size.
Bonus
DoS (Denial of Service) Examples:
- TCP SYN Flood Attack:
- Command:
hping3 -S -p 80 --flood target-S: Sends SYN packets.-p 80: Specifies port 80 as the destination port (replace with the desired port).--flood: Conducts a SYN flood attack by sending a large number of SYN packets to the target.target: Replace this with the IP address or hostname of the target machine.
- Description: This command launches a DoS attack by overwhelming the target server with a flood of TCP SYN packets, exhausting its resources and making it unresponsive.
- Command:
Conclusion
Hping3 serves as a powerful and flexible tool for network analysis and security testing. Its ability to craft and manipulate network packets offers invaluable insights into network performance and security vulnerabilities. However, it is crucial to use hping3 ethically and legally, ensuring that all activities comply with relevant laws and policies. By understanding and utilizing the capabilities of hping3 as outlined in this cheat sheet, professionals can enhance their network management and security strategies significantly



