Introduction
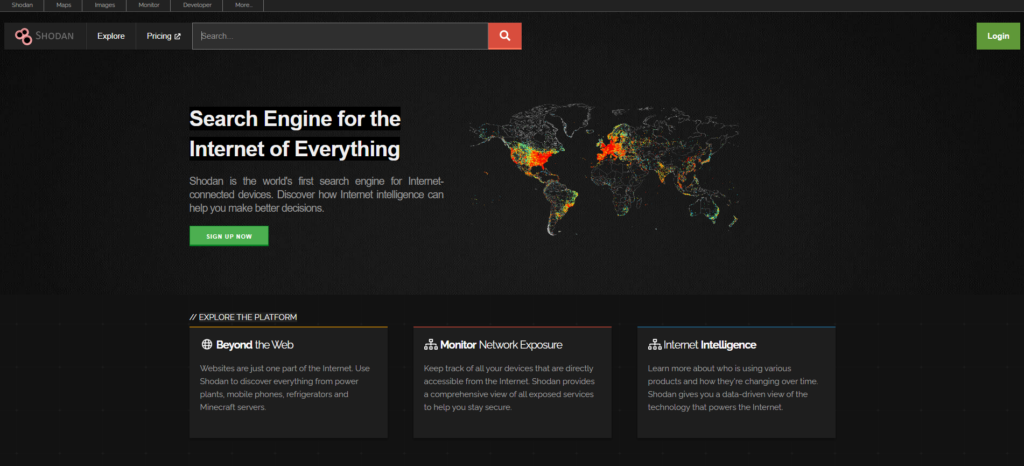
In today’s rapidly evolving digital world, the ability to detect, assess, and mitigate vulnerabilities in internet-connected devices is crucial. Shodan, often referred to as the “Google of IoT,” offers cybersecurity professionals, researchers, and enthusiasts an invaluable tool to explore the Internet of Things (IoT) and beyond. Unlike traditional search engines, which index websites, Shodan uncovers the infrastructure that powers the web—servers, webcams, routers, and more. This Shodan Dork Cheat Sheet will equip you with essential and advanced Shodan queries to bolster your cybersecurity expertise and protect your network from potential threats.
Learning Objectives
By the end of this article, you will:
- Understand Shodan’s role in cybersecurity.
- Learn to use both basic and advanced Shodan search queries.
- Identify security vulnerabilities in internet-connected devices.
- Use Shodan effectively to monitor and secure networks.
What is Shodan?
Shodan is a search engine that scans the internet for devices connected to it. This includes a wide variety of systems such as industrial control systems (ICS), webcams, routers, security cameras, servers, home automation systems, and much more. While traditional search engines index content from websites, Shodan indexes information on the services running on devices—such as open ports, protocols, and software versions—providing a deeper look into how devices are configured. This Shodan Dork Cheat Sheet is a critical tool for understanding the current security posture of internet-connected devices, identifying potential vulnerabilities, and ensuring no device is unintentionally exposed.
Key applications of Shodan include:
- Vulnerability assessment: Identify exposed systems with potential security weaknesses.
- Network monitoring: Track devices connected to your network and assess their security.
- Research: Understand the global deployment of certain technologies and protocols.
- Security defense: Detect insecure configurations in your infrastructure before attackers exploit them.
Who Actively Uses Shodan?
Shodan is utilized by a diverse group of users, each with specific goals:
- Cybersecurity professionals: Network security experts rely on Shodan to uncover vulnerabilities in devices and ensure systems are securely configured.
- Ethical hackers (white hats): Penetration testers use Shodan to identify security weaknesses in systems, enabling organizations to bolster their defenses.
- Network administrators: Admins monitor the exposure of devices within their infrastructure to ensure nothing is publicly accessible that shouldn’t be.
- Researchers: Academics and security researchers use Shodan to study trends in IoT, analyze device security, and track protocol usage globally.
- Malicious actors (black hats): Unfortunately, cybercriminals also use Shodan Dork Cheat Sheet to identify vulnerable systems. This reinforces the need for organizations to regularly check Shodan for any exposed systems.
General Search Queries
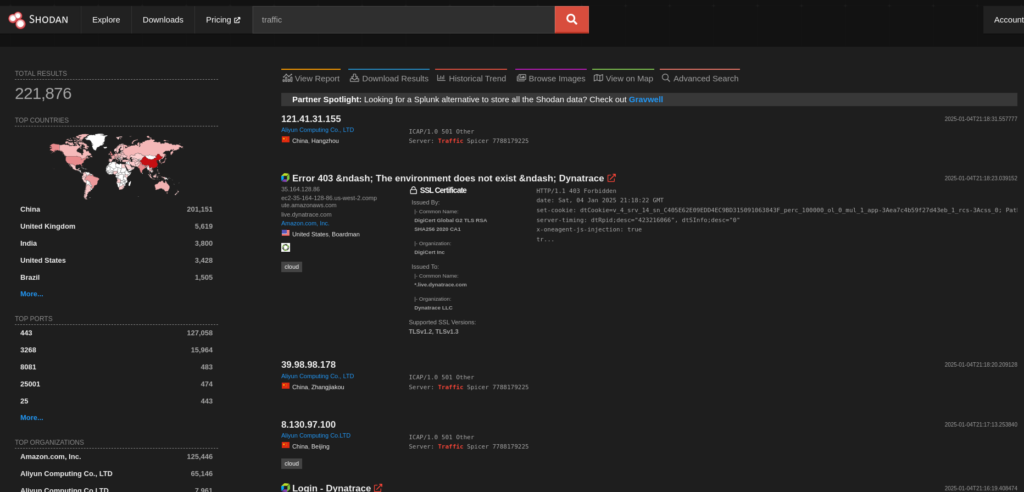
Shodan allows users to create queries to locate specific devices, services, or configurations. Here are some of the most widely used queries:
- city:”[city name]”: Find devices located in a specific city.
Example:city:"New York"searches for devices in New York City. - country:”[country code]”: Search for devices in a specific country.
Example:country:"US"finds devices in the United States. - geo:”[latitude],[longitude]”: Search for devices at a specific geographical location.
Example:geo:"40.7128,-74.0060"searches around New York City’s coordinates. - hostname:”[hostname]”: Look for devices with a specific hostname.
Example:hostname:"example.com"returns devices hosted under example.com. - net:”[IP range]”: Find devices within a certain IP range.
Example:net:"192.168.1.0/24"finds devices in the IP range 192.168.1.0-192.168.1.255. - os:”[operating system]”: Search for devices running a specific operating system.
Example:os:"Windows"returns devices running Windows. - port:”[port number]”: Find devices with a specific open port.
Example:port:22returns devices with SSH running on port 22. - org:”[organization name]”: Search for devices associated with a particular organization.
Example:org:"Google"finds devices associated with Google. - isp:”[ISP name]”: Search for devices using a specific ISP.
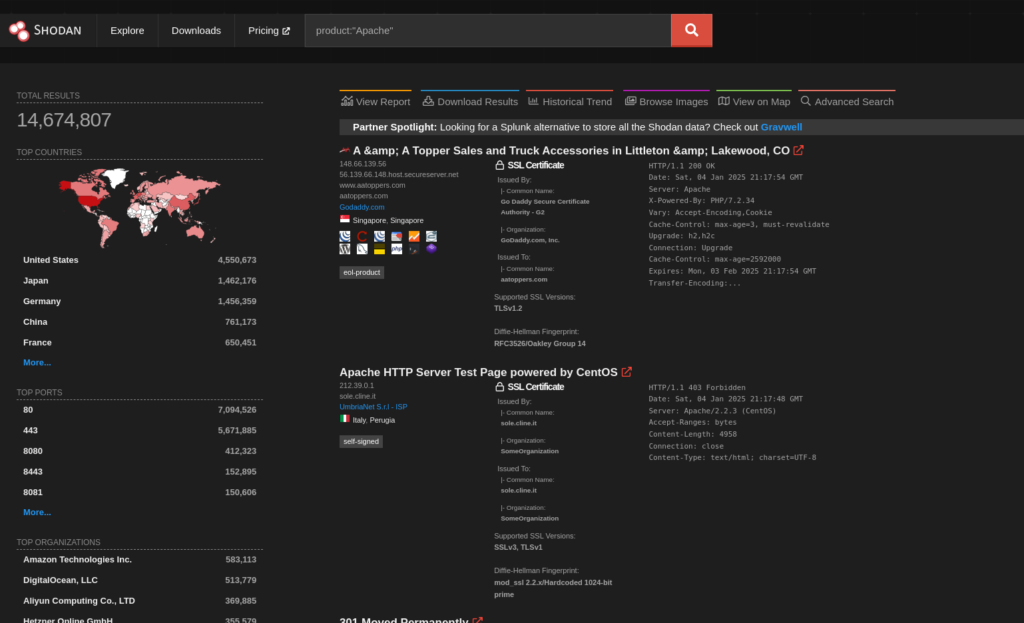
Example:isp:"Comcast"finds devices using Comcast as their ISP. - product:”[product name]”: Find devices running a specific software product.
Example:product:"Apache"returns devices running the Apache web server. - version:”[version number]”: Search for devices running a particular version of software.
Example:version:"5.7"returns devices running MySQL version 5.7. - has_screenshot:”true”: Find devices with available screenshots.
Example:has_screenshot:truereturns devices that include a screenshot. - ssl.cert.subject.cn:”[common name]”: Search for SSL certificates with a specific common name.
Example:ssl.cert.subject.cn:"example.com"finds certificates for example.com. - http.title:”[title text]”: Find web pages with a specific title.
Example:http.title:"Welcome"returns web pages with the title “Welcome.” - http.status_code:[code]: Search for devices returning a specific HTTP status code.
Example:http.status_code:404returns devices showing a 404 Not Found page. - ssl:”[SSL keyword]”: Find devices with specific SSL configurations or details.
Example:ssl:"SHA256"returns devices using SHA256 encryption in their SSL configuration. - before:”[date]” / after:”[date]”: Search for devices that were indexed before or after a certain date.
Example:before:"2023-01-01"finds devices indexed before January 1, 2023.
Specific Applications and Services
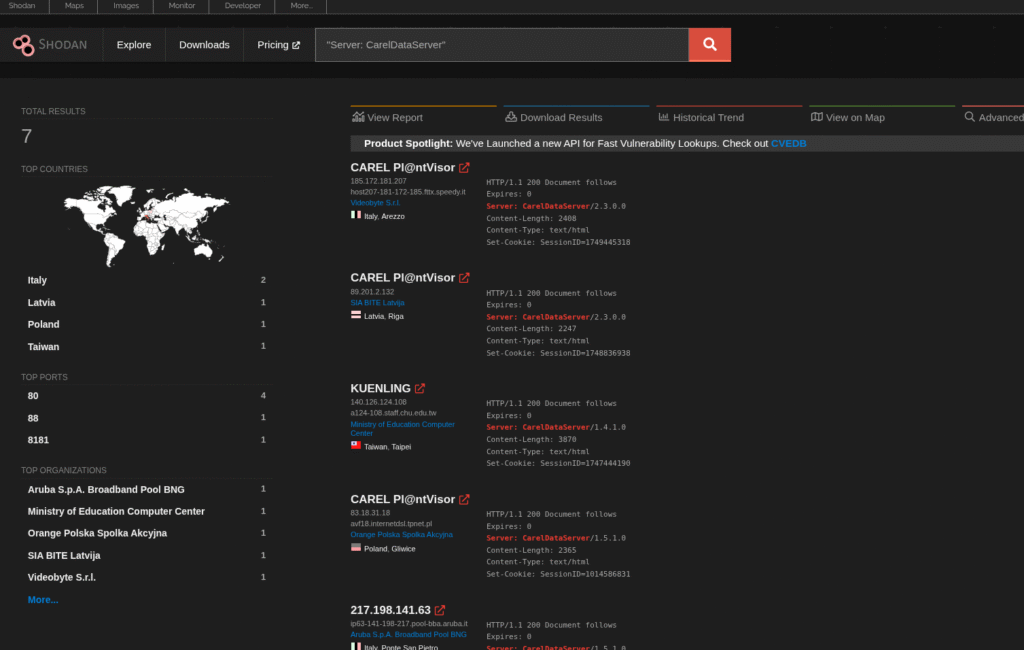
Shodan can also pinpoint devices running particular services or applications, making it useful for targeted searches:
- product:”[product name]”: Locate devices running a specific product.
Example:product:"Apache"finds servers running the Apache web server. - version:”[version]”: Find devices running a specific software version.
Example:version:"2.4.41"returns devices running Apache version 2.4.41. - “default password”: Find devices still using their default credentials (a major security risk).
Example:"default password"reveals devices that haven’t changed their default login credentials. - webcam: Search for internet-connected webcams.
Example:webcamreturns exposed webcams connected to the internet. - ftp: Find devices with FTP services.
Example:ftpreturns devices running FTP servers, which may be misconfigured or vulnerable. - “X-Powered-By: PHP/[version]”: Locate servers running specific PHP versions.
Example:"X-Powered-By: PHP/5.6"finds servers running PHP version 5.6. - iis:[version number]: Search for servers running a specific version of Microsoft IIS.
Example:iis:8.5finds servers running IIS version 8.5. - “MongoDB Server Information” port:27017: Identify exposed MongoDB databases on the default port.
Example:"MongoDB Server Information" port:27017reveals unsecured MongoDB servers.
Security Vulnerabilities and Weaknesses
Shodan is an essential tool for identifying devices with known security vulnerabilities. Use these queries to find systems that may be at risk:
- vuln:”[CVE-ID]”: Search for devices affected by a specific CVE (Common Vulnerabilities and Exposures) ID.
Example:vuln:"CVE-2021-26855"finds devices vulnerable to a Microsoft Exchange Server exploit. - ssl.cert.expired:”true”: Find devices using expired SSL certificates.
Example:ssl.cert.expired:truereturns systems with expired SSL certificates, which can cause security warnings or issues. - “heartbleed” vuln: Search for devices vulnerable to the Heartbleed bug, a critical SSL/TLS vulnerability.
Example:"heartbleed" vulnidentifies devices affected by the Heartbleed vulnerability. - “Authentication: disabled”: Find devices where authentication mechanisms are disabled, leaving them exposed.
Example:"Authentication: disabled"returns databases or services with no authentication in place. - ssl:”TLSv1″: Locate devices using the outdated and insecure TLSv1 protocol.
Example:ssl:"TLSv1"identifies devices still relying on TLSv1, which is susceptible to attacks. - http.component:”Drupal” vuln:”CVE-2018-7600″: Search for Drupal websites vulnerable to the Drupalgeddon2 vulnerability.
Example:http.component:"Drupal" vuln:"CVE-2018-7600"identifies Drupal sites that are vulnerable to a critical CVE.
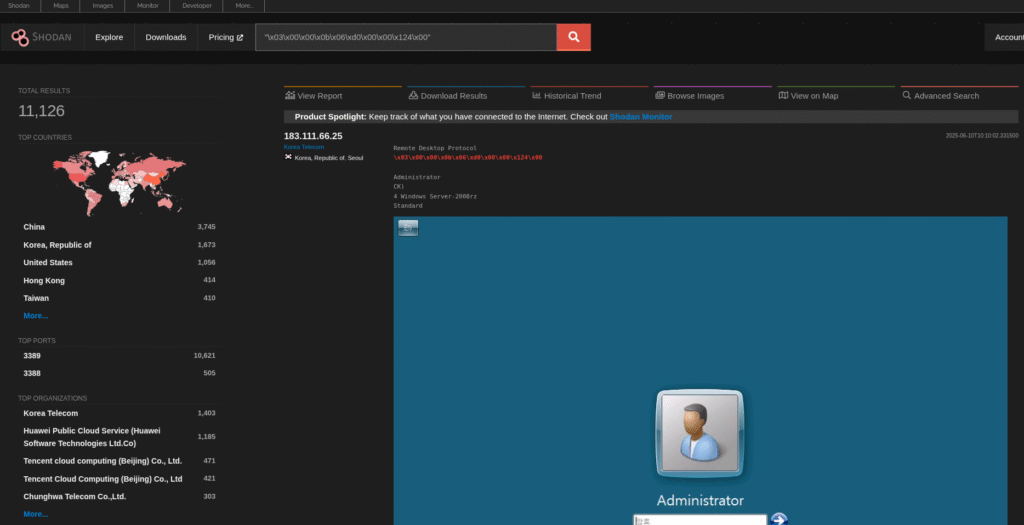
Example Complex Queries for Shodan
For more advanced search needs, Shodan supports combining multiple filters to create powerful queries. Here are some examples:
- os:”Linux” port:”22″ “SSH” country:”JP” : Find Linux devices in Japan running SSH on port 22.
- product:”Apache” version:”2.4.7″ -“200 OK” : Identify Apache servers running version 2.4.7 that do not return a 200 OK status.
- city:”New York” os:”Windows” port:”3389″ : Find Windows devices with RDP enabled in New York City.
- net:”192.168.1.0/24″ webcam : Locate webcams within the specified IP range.
- org:”Google” ssl.cert.expired :”true”: Search for devices owned by Google with expired SSL certificates.
- country:”DE” product:”MySQL” version:”5.5″ “default password” : Find MySQL databases in Germany using default credentials.
Conclusion
This Shodan Dork Cheat Sheet is a powerful, versatile tool that offers cybersecurity professionals deep insight into the internet’s infrastructure. Its ability to discover vulnerabilities, misconfigurations, and exposed devices makes it invaluable for both defensive and offensive security work. However, it is crucial to use Shodan responsibly and within legal limits. By mastering Shodan search queries, you can enhance your cybersecurity defenses and respond swiftly to potential risks in your networks.

