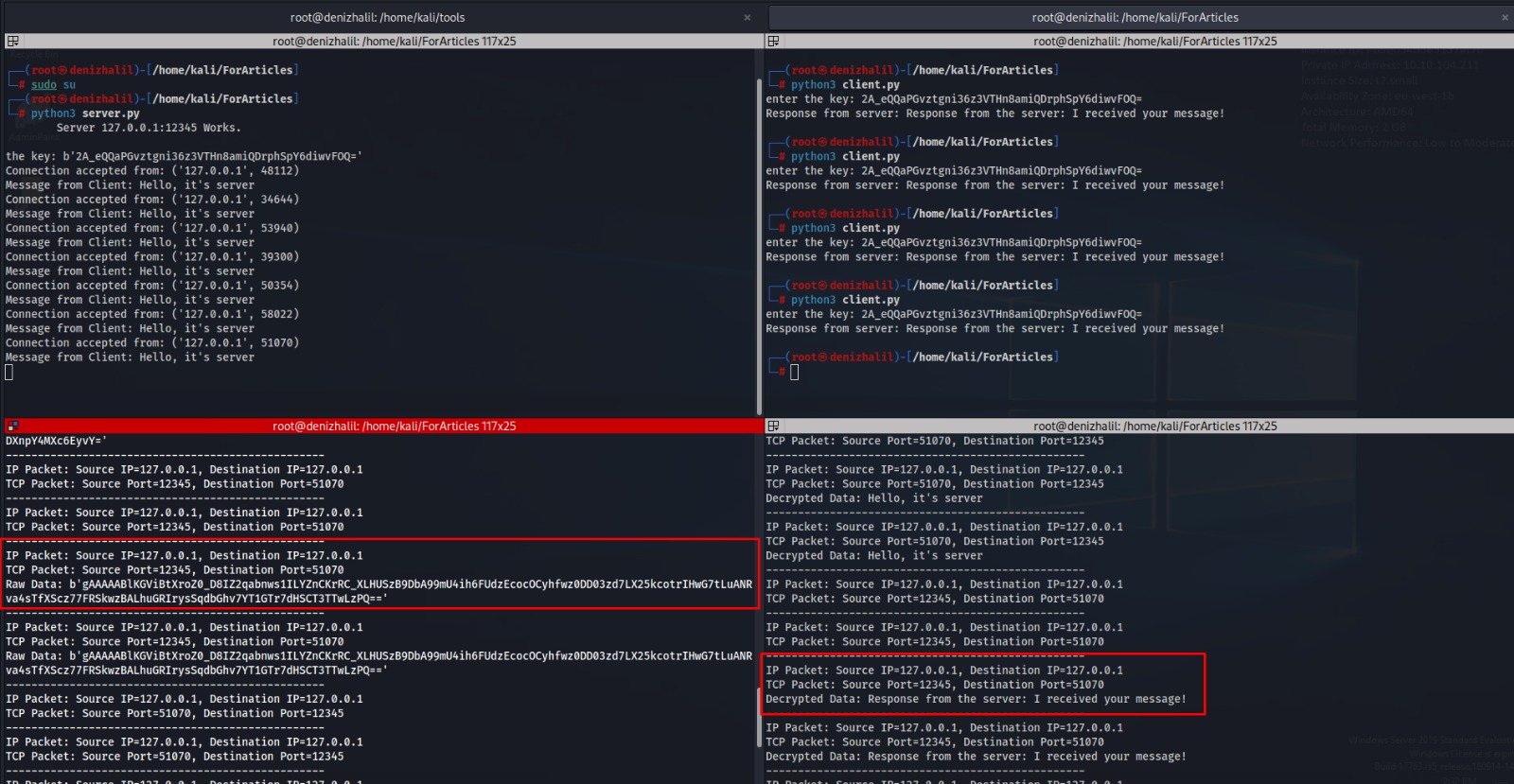
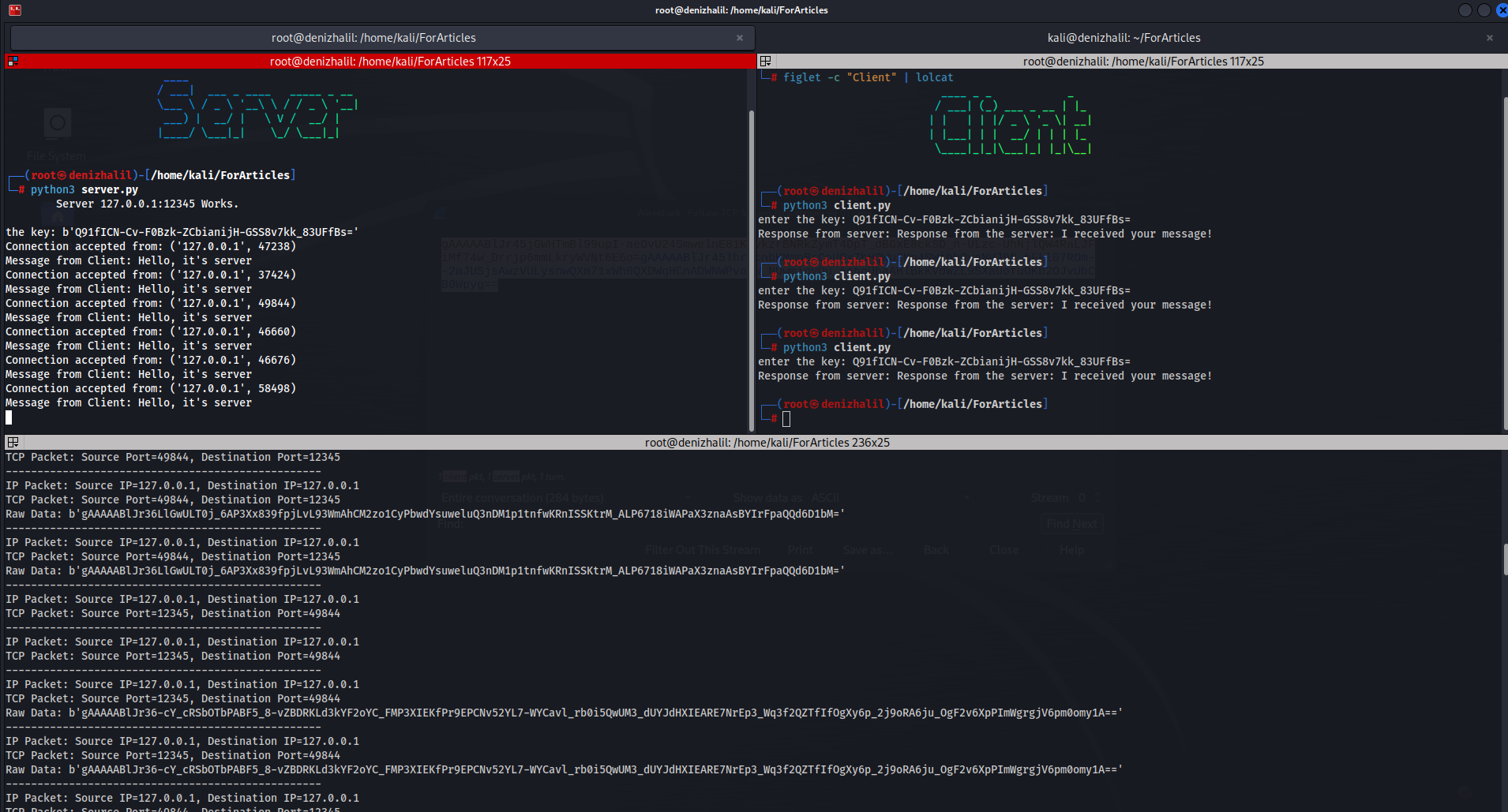
Server and Client Application in C
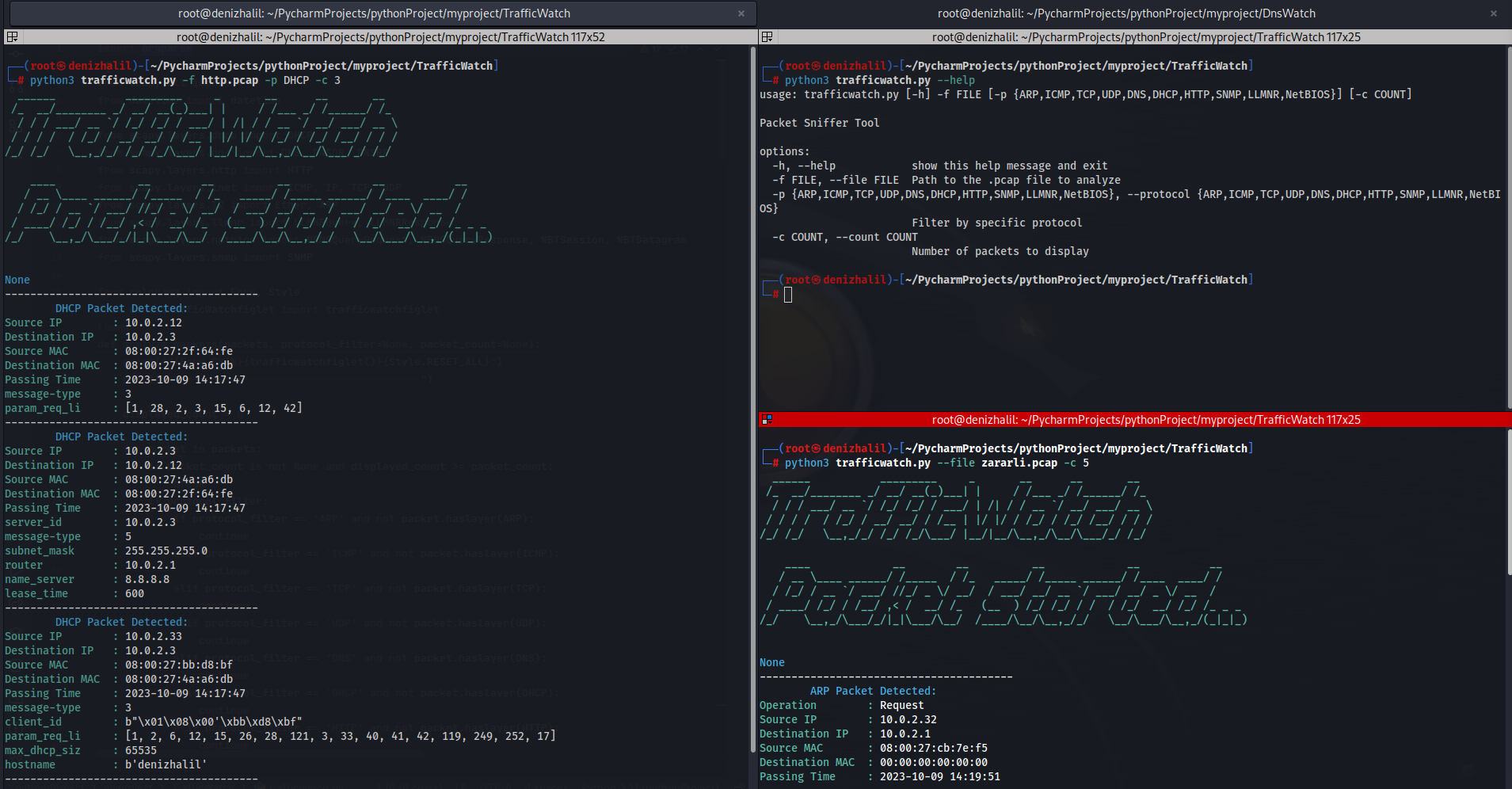
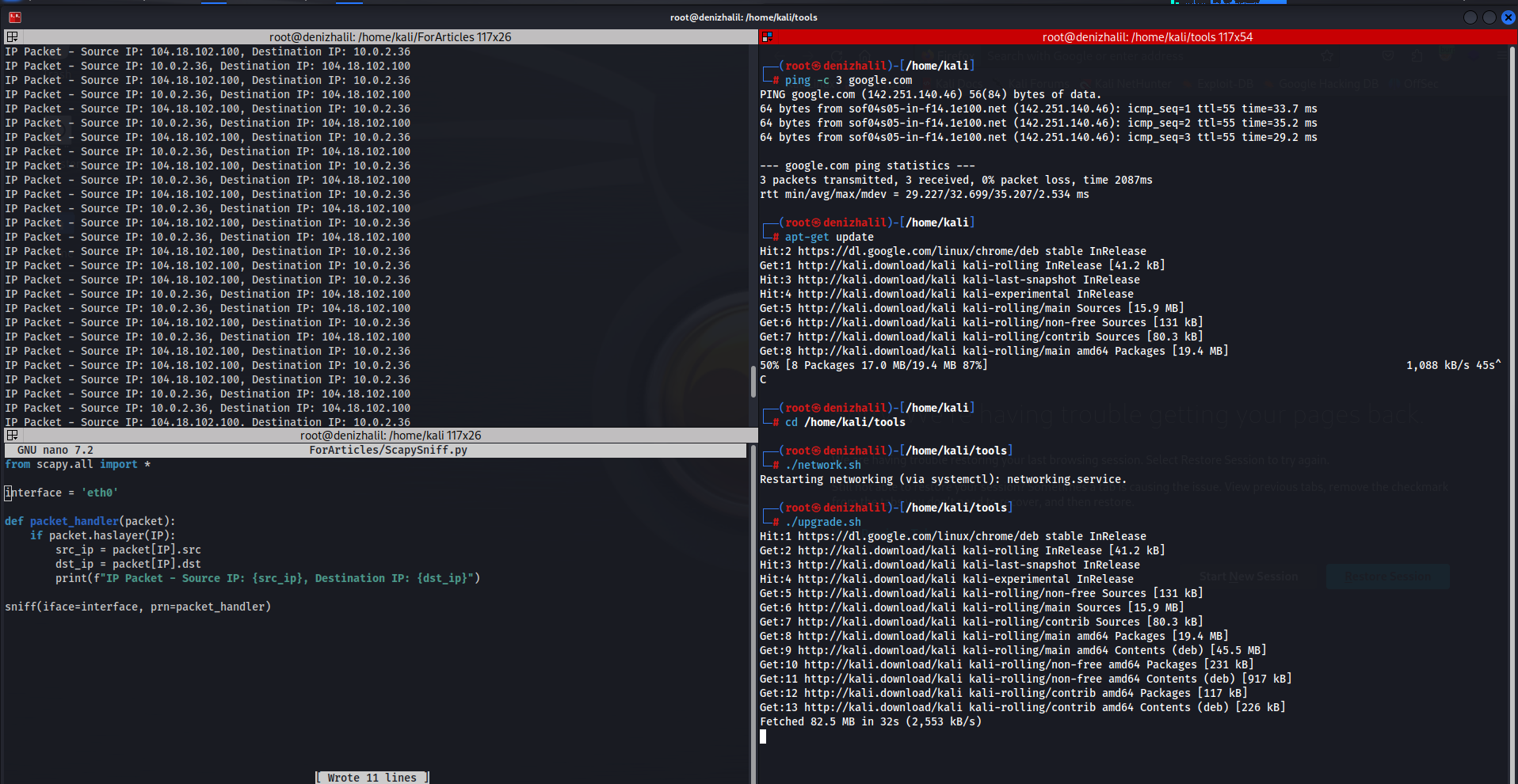
Introduction The C programming language is a powerful language commonly used for developing computer programs. In this article, we will explore how to create a basic server and client application using the C programming language. Such an application can help you gain a fundamental understanding of data communication and network programming. Server Application First, let’s … Read more