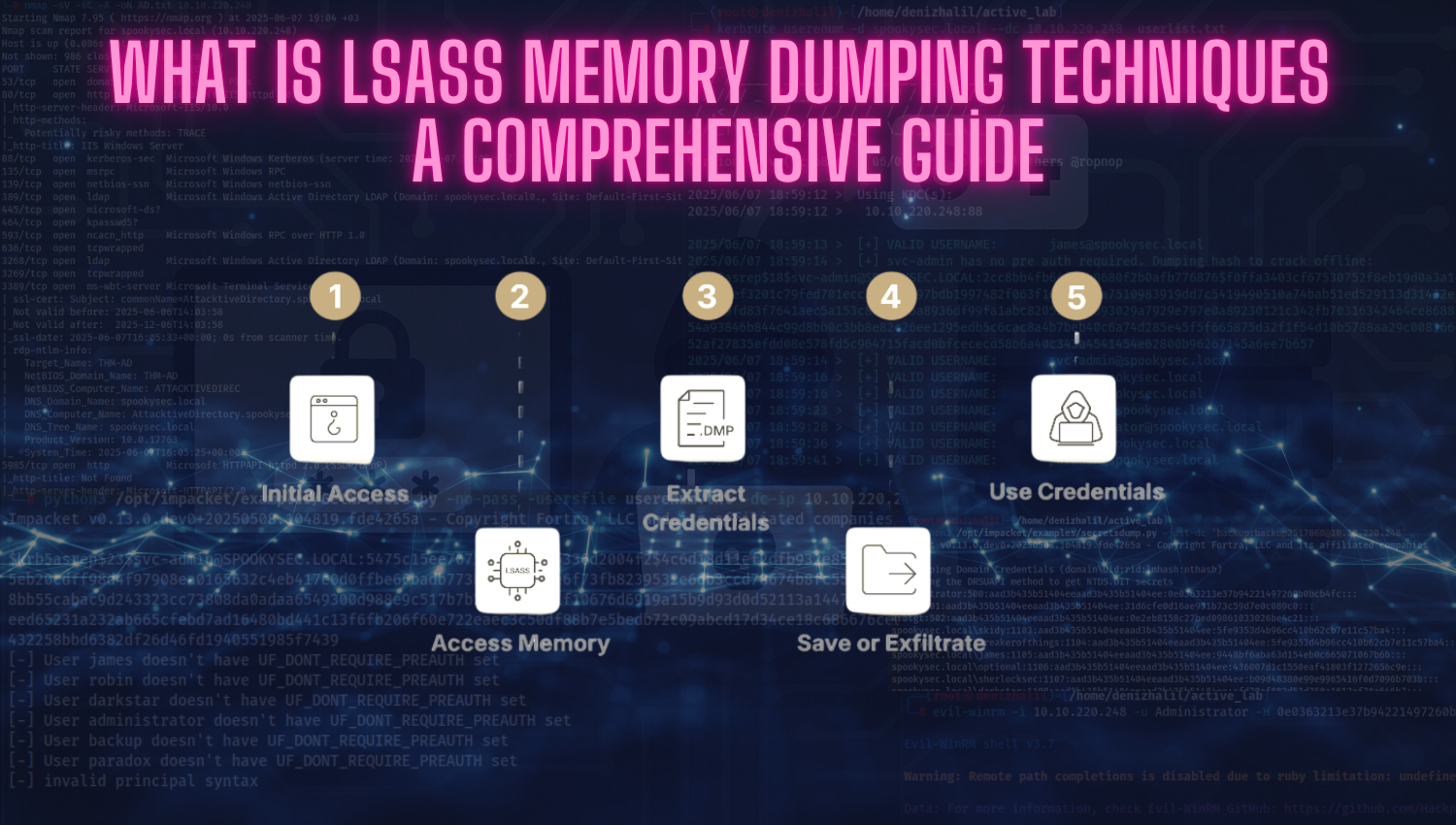
What is LSASS Memory Dumping Techniques: A Comprehensive Guide
Introduction As cyber threats continuously evolve and become increasingly sophisticated, attackers persistently target critical system processes to extract valuable credentials and maintain persistent access within compromised environments. One of the most targeted components on Windows systems is the Local Security Authority Subsystem Service, better known as LSASS. This core Windows process is responsible for managing user authentication, enforcing security policies, and