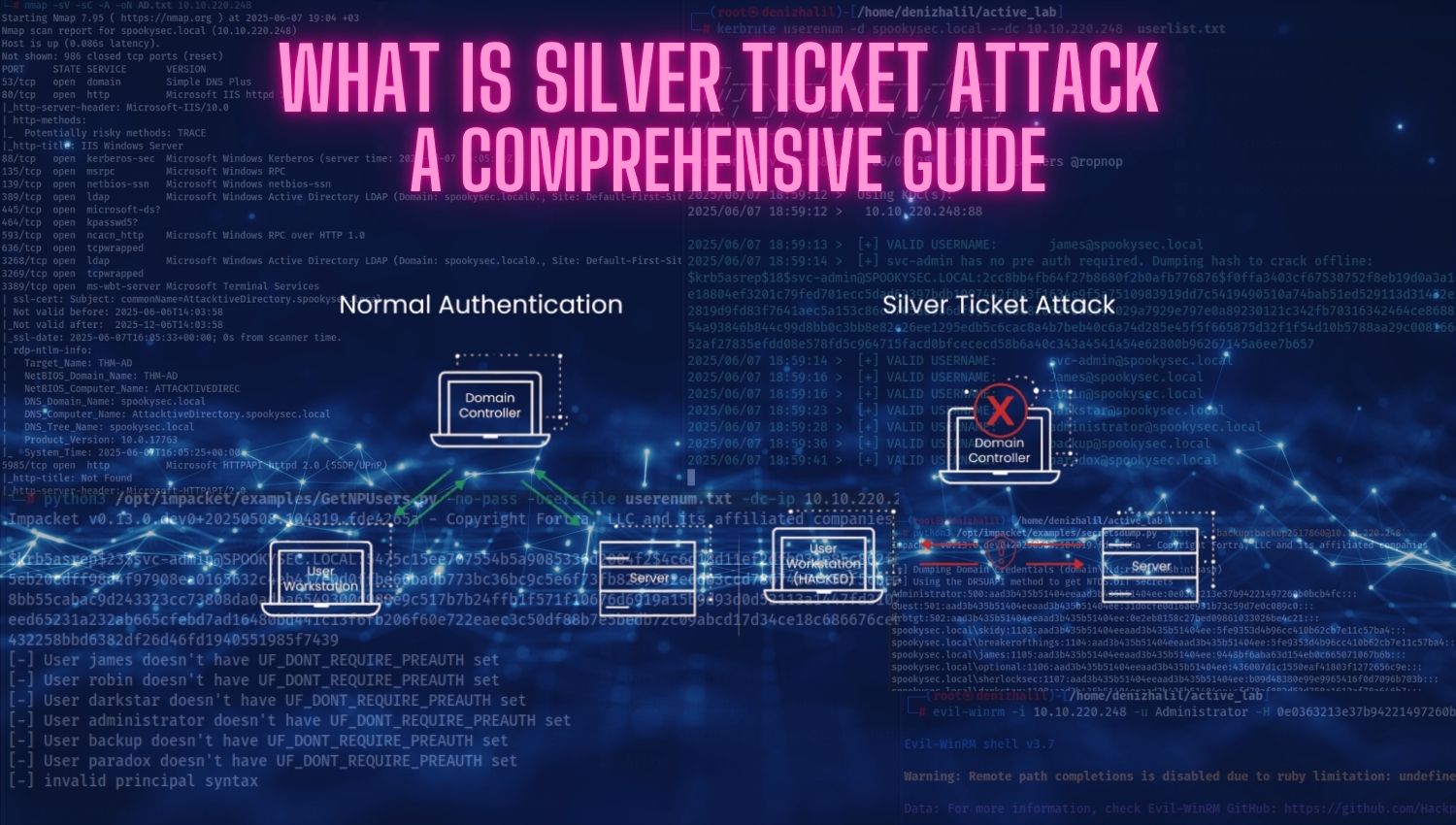
What is Silver Ticket Attack: A Comprehensive Guide
Introduction A Silver Ticket attack is a stealthy Kerberos exploitation technique that allows attackers to access specific network services in an Active Directory environment by forging service tickets. Unlike Golden Tickets, which provide domain-wide access by compromising the KRBTGT account, Silver Tickets exploit individual service account credentials to impersonate authorized users for targeted resources. These attacks bypass the domain