Introduction
OWASP Amass is a robust open-source tool designed for asset discovery, subdomain enumeration, and comprehensive attack surface mapping in cybersecurity. By utilizing both passive and active reconnaissance techniques, Amass supports security professionals in detecting hidden domains, IP ranges, and infrastructure links that might otherwise remain unnoticed during a standard assessment. Its modular features include DNS scanning, recursive subdomain discovery, brute-forcing with wordlists, certificate and public archive analysis, and asset database management for historical comparison and reporting. The ability to automate these processes, along with its support for cloud, on-premises, and container environments, makes Amass extremely valuable for penetration testers, bug bounty hunters, and blue teams. With continuous asset tracking and a visual analysis interface, teams can quickly adapt to changes, identify new exposures, and integrate findings into incident response and security strategies. Thanks to its ongoing updates and vibrant community support, Amass remains a leading solution for organizations aiming to stay ahead of evolving threats and maintain effective attack surface management.
Learning Objectives
- Understand Amass’s role in attack surface mapping
- Apply basic and advanced usage examples for practical subdomain discovery
- Utilize a cheat sheet for popular Amass commands
- Develop problem-solving strategies in real-world cybersecurity scenarios
Amass’s Place in Cybersecurity
Amass plays a central role in asset discovery for red teams, penetration testers, threat intelligence analysts, and bug bounty hunters who need comprehensive visibility into an organization’s digital footprint. Leveraging a suite of specialized modules—Intel, Enum, Viz, Track, and DB—Amass empowers users to perform large-scale OSINT scoping, conduct detailed DNS-based subdomain enumeration, track asset changes over time, and generate graph-based visualizations for critical assessment. By aggregating data from public DNS records, SSL/TLS certificates, APIs, domain wordlists, and various historical sources, Amass consistently provides a rich set of actionable intelligence to identify external exposures and vulnerabilities before they can be exploited. Thanks to active maintenance by OWASP and a vibrant developer community, Amass remains one of the most trusted and widely adopted tools for attack surface mapping. Its rapid adoption rate and integration capabilities allow for seamless collaboration with other reconnaissance and scanning platforms. For organizations seeking to strengthen their security posture, Amass delivers reliability, scalability, and accuracy in identifying internet-exposed assets and shadow IT infrastructure.
Basic and Advanced Usage Examples
Essential Commands:
- Discover subdomains rapidly using passive sources:
amass enum -d example.com -passiveThis command performs non-intrusive OSINT discovery using public repositories and APIs.
- Write results to a file:
amass enum -d example.com -o subdomains.txtDirects subdomain results into a specified text file.
- Run a basic enumeration across multiple domains:
amass enum -d example.com,example.netSimultaneously scans multiple root domains for subdomains.
- Perform DNS port scanning:
amass enum -d example.com -p 443,8080 -activeFilters enumeration to specific ports, helping map web and application services more precisely.
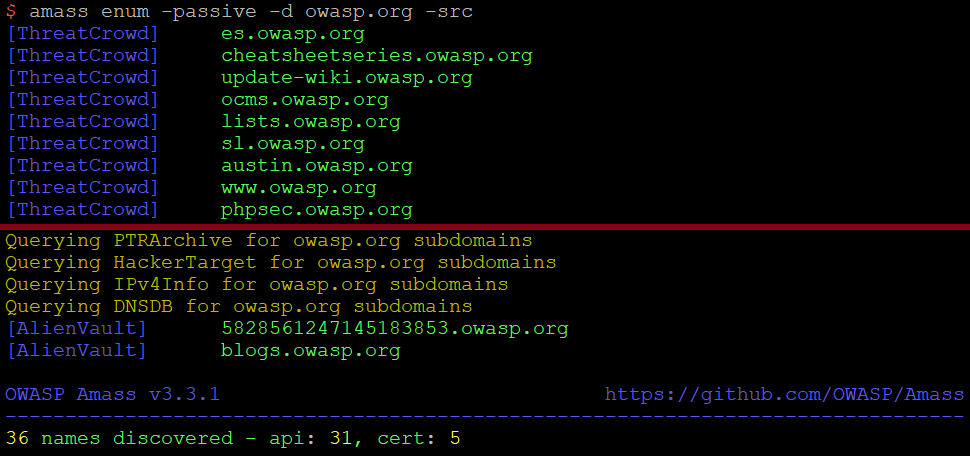
- Passive reconnaissance with source tracking:
amass enum -passive -d example.com -srcShows which OSINT sources returned each subdomain, aiding validation and reporting.
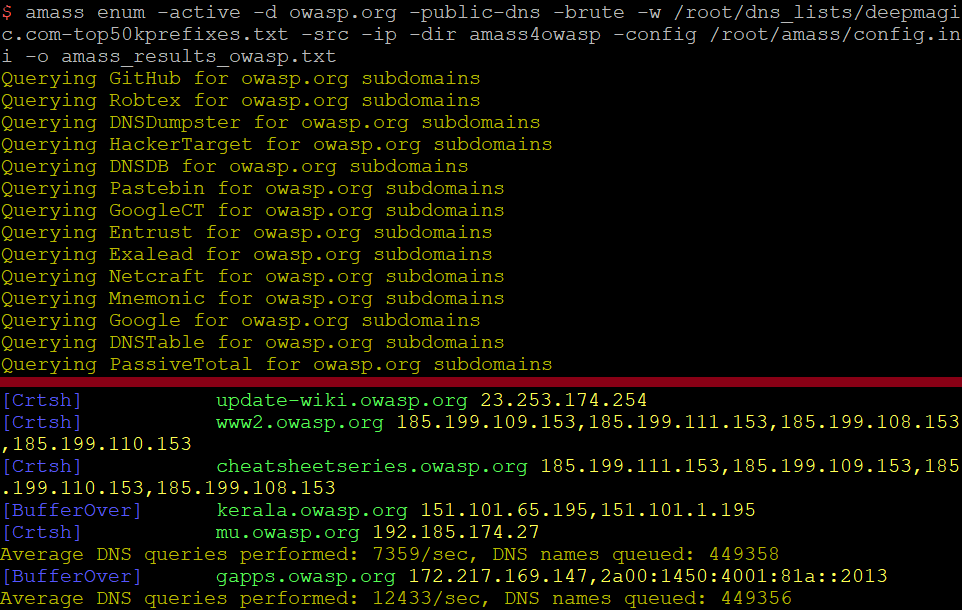
Advanced Techniques:
- Comprehensive brute-force enumeration with custom wordlists:
amass enum -active -d example.com -brute -w wordlist.txt -ipExecutes active enumeration using provided wordlist, also displaying IP addresses for each discovered subdomain.
- Enhanced OSINT with API config:
amass enum -d example.com -config apis.iniUtilizes API keys and custom configuration to maximize data sources and discovery depth.
- Output data in machine-readable format for automation:
amass enum -d example.com -json results.jsonStores reconnaissance results in JSON format for integrations and analysis.
- Visualize attack surface for deeper analysis:
amass viz -dir ./amassdb -d3Renders a graph of discovered assets for review using visualization tools.
These examples illustrate Amass’s versatility, helping professionals tailor discovery processes to organizational needs and research goals.
Cheat Sheet Table
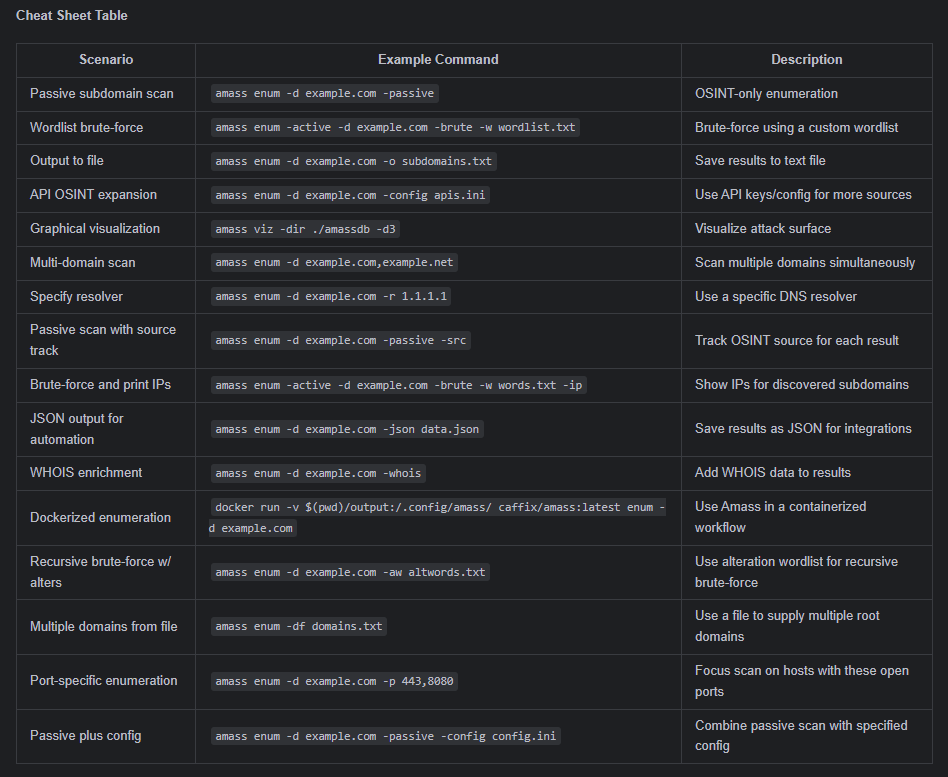
This expanded table equips you for a variety of real-life Amass deployments, from basic recon to advanced, automated, and large-scale discovery scenarios.
Behavioral Questions and Problem Solving Approach
Effective use of Amass in security assessments means not only automated discovery, but also critical thinking about risk, validation, and process integration. The questions below reflect real-world scenarios that practitioners encounter during reconnaissance and asset mapping. Each is paired with solution approaches that represent best practices in the field.
Prioritize domains uncovered by Amass that reference administration panels, development, test, or backup environments, external integrations, or legacy infrastructure. Correlate these with SSL certificate transparency logs, WHOIS records, and port scans to identify potentially exposed sensitive assets. Use vulnerability scanners to determine actual risk level.
Compare output from Amass’s passive and brute-force modules to expose subdomains missed by OSINT alone. Highlight those found exclusively by brute-force, and investigate with DNS resolutions and HTTP probes to confirm legitimacy. This dual approach closes gaps in asset awareness, especially for assets not indexed publicly.
Integrate Amass results with tools like Subfinder, Assetfinder, or custom scripts, and cross-reference with DNS checks and live endpoint investigation (using HTTPX, Nmap, etc.). Only proceed to exploitation after confirmation, thus reducing false positives and ensuring actionable intelligence
Use alteration wordlists, WHOIS lookups, and internal keyword filters (dev, vpn, api, intranet, staging) to focus enumeration. Leverage Amass’s database and history modules to find newly exposed infrastructure and verify relevant endpoints with active scanning.
Set up regular Amass scans with cron jobs or CI pipelines, activating the “track” module for historical change analysis and automated notifications. Store output in databases for future comparison and reporting. This makes attack surface management continuous, not point-in-time.
Pipe Amass enumeration output into dedicated takeover scanners such as Nuclei or custom scripts. Flag subdomains with CNAMEs that point to cloud platforms, third-party SaaS, or expired endpoints, then verify takeovers using built-in templates and risk scoring.
Thoroughly working through these questions with Amass not only improves asset discovery, but also strengthens the technical rigor of the security assessment process and ensures real-world defense against modern attack vectors.
Conclusion
Amass sets the standard in subdomain enumeration and attack surface reconnaissance, combining OSINT aggregation, active search, and smart visualization into a single toolkit. With its suite of subcommands—including intel, enum, viz, track, and db—Amass empowers cybersecurity teams to discover even deeply buried assets by aggregating public DNS records, scraping certificate logs, interfacing with dozens of APIs, and recursively mapping infrastructure connections. Its capability to automate scanning, monitor changes over time, and visually map complex relationships makes it a cornerstone tool for modern penetration testers, red teams, vulnerability managers, and bug bounty hunters seeking actionable intelligence. By mastering Amass’s extensive options, practitioners can adapt their workflows to ever-changing environments, reduce exposures proactively, and elevate the defense posture of any organization against the latest reconnaissance-driven threats.