Introduction
Bettercap stands as a highly regarded open-source tool among cybersecurity professionals, ethical hackers, and network administrators. It plays a pivotal role in advanced network reconnaissance and security assessments. Functioning across Linux, macOS, and Windows platforms, Bettercap is integral for scrutinizing network traffic, executing penetration tests, and identifying network vulnerabilities. Its operation demands not only expertise but also a strong commitment to ethical practices to prevent unauthorized network interference.
Key Features and Applications
- Network Discovery and Monitoring: Bettercap shines in detecting devices, services, and open ports within a network. It extends its reach to uncover Wi-Fi networks, BLE (Bluetooth Low Energy) devices, and various IoT (Internet of Things) devices, showcasing its versatility.
- Man-in-the-Middle (MITM) Attacks: Utilizing methods like ARP Spoofing and DNS Spoofing, Bettercap enables effective MITM attacks. These attacks facilitate the interception and manipulation of data transfers between a target and a server, a critical aspect in network security testing.
- Traffic Capture and Analysis: The tool is adept at capturing and analyzing both HTTP and HTTPS traffic. It employs sophisticated techniques like HSTS bypass for scrutinizing encrypted HTTPS traffic, a vital feature for comprehensive network analysis.
- Social Engineering and Phishing: Bettercap can be employed for more nefarious means, such as directing network traffic to malicious pages or content for extracting user information, emphasizing the need for ethical usage.
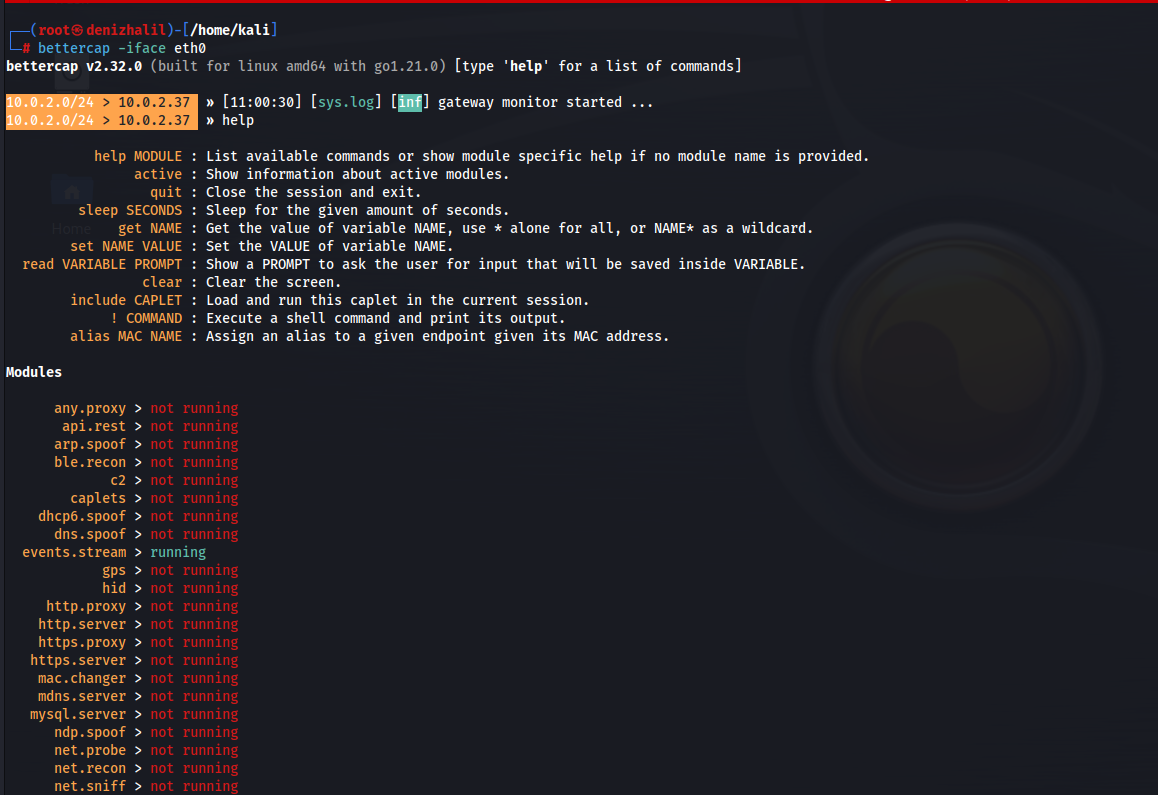
Installation and Basic Commands
- Installation:
- Linux:
sudo apt-get install bettercap - macOS (using Homebrew):
brew install bettercap - Windows: Operational via WSL (Windows Subsystem for Linux).
- Linux:
- Starting Bettercap:
- Command:
sudo bettercap - Initiates the Bettercap interface, serving as the gateway to its array of functions.
- Command:
- Listing Network Interfaces:
- Command:
net.interfaces - Enumerates all network interfaces, aiding in selecting the appropriate one for analysis.
- Command:
- Network Reconnaissance:
- Command:
net.recon on - Engages the tool in discovering devices across the network.
- Command:
- Setting Target IP:
- ARP Spoofing:
set arp.spoof.targets [Target IP] - DNS Spoofing:
set dns.spoof.domains [Target Domain]
- ARP Spoofing:
- Initiating ARP Spoofing:
- Command:
arp.spoof on - Commences an ARP spoofing attack, a fundamental technique in network intrusion.
- Command:
- Initiating DNS Spoofing:
- Command:
dns.spoof on - Engages in DNS spoofing for designated domains, a critical step in MITM attacks.
- Command:
- Capturing HTTP and HTTPS Traffic:
- HTTP:
http.sniffer on - HTTPS (HSTS bypass):
hstshijack/hstshijack
- HTTP:
- Scanning Wi-Fi Networks:
- Command:
wifi.recon on - Scans for local Wi-Fi networks, expanding the scope of network analysis.
- Command:
- Social Engineering Tools:
- Command:
set http.proxy.script [Script Path] - Employs specified scripts for manipulating traffic through the HTTP proxy, demonstrating its capacity for advanced network manipulation.
- Command:
- Exiting Bettercap:
- Command:
quit - Terminates the Bettercap session, a necessary step to conclude operations.
- Command:
Security and Ethical Considerations
The potency of Bettercap necessitates its cautious and conscientious use. Network security testing and penetration exercises should be strictly confined to networks where explicit permission has been secured. Engaging in unauthorized network interference not only poses legal risks but is also fundamentally unethical.
Conclusion
Bettercap emerges as a formidable and adaptable instrument in the realm of network security and penetration testing. Its diverse modules and customizable scripts offer extensive applicability, catering to a broad spectrum of network analysis needs. Nonetheless, its employment demands a high degree of responsibility and adherence to legal and ethical standards.