Dark Web and Deep Web:
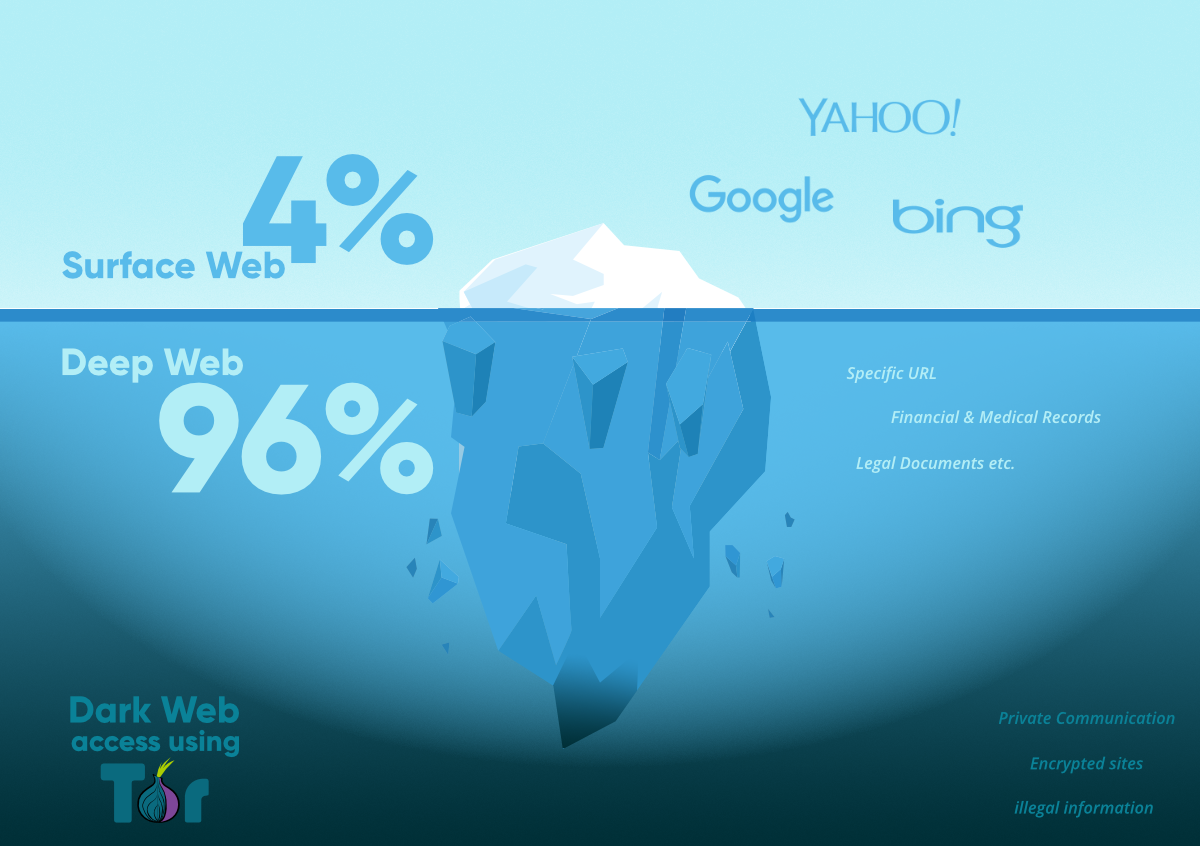
The internet has become an integral part of our daily lives, but beyond the widely accessible surface of the internet, there exists a deeper and more mysterious realm known as the Deep Web and Dark Web. In this article, we will explore what the Deep Web and Dark Web are, delve into their histories, discuss the Tor network, examine the Deep Web, shed light on the Dark Web, and provide a security warning.
History:
The history of the Deep Web and Dark Web is intertwined with the development of the internet itself. In the early days of the internet, accessing websites and information was a relatively straightforward process. However, as more private networks, databases, and services emerged, a portion of the internet that was not indexed by search engines and generally inaccessible came to be known as the Deep Web.
The origin of the Dark Web can be traced back to the early 2000s. The Tor project, developed by the U.S. Naval Research Laboratory, played a significant role in the emergence of the Dark Web. Tor is an anonymity network designed to encrypt internet traffic and enable users to remain anonymous. Launched in 2002, Tor facilitated the growth of the Dark Web, which became a haven for illegal activities. “I recommend you to check the PrivacyNet tool on privacy”
The Tor Network:
The Tor network, also known as The Onion Router, is the most widely used anonymity network for accessing the Dark Web. Tor is specifically designed to help users protect their identities online. It achieves this by encrypting internet traffic and routing it through a series of volunteer-operated servers, making it difficult to trace the origin of the traffic.
The Tor network serves as a gateway to accessing the Deep Web and Dark Web. Users can access Dark Web websites and services using the Tor browser. While navigating the Tor network, users must take precautions, maintain their anonymity, and abide by legal guidelines.
Deep Web
The Deep Web refers to the portion of the internet that is not indexed by search engines and is not readily accessible to the general public. It consists of private networks, databases, services, and resources that require authorization to access.
Examples of content found in the Deep Web include private company intranets, banking systems, academic library databases, healthcare records, and membership-based forums. Accessing such content typically requires proper authentication and authorization.
The Deep Web is primarily used for legitimate purposes, such as safeguarding privacy, protecting sensitive data, and preserving personal information. It should not be confused with the Dark Web, as the Deep Web does not inherently imply illegal activities.
Dark Web
The Dark Web is a subset of the Deep Web and can be accessed through specific structures and software designed to provide anonymity and privacy. The Dark Web operates on networks like Tor. It is commonly associated with illegal activities due to the anonymity and privacy it offers.
On the Dark Web, one can find illicit marketplaces, anonymous communication channels, and various services associated with illegal activities. These may include drug trafficking, weapons sales, stolen data, malicious software, and more. However, it is essential to note that the Dark Web is not solely defined by illegal activities. Legal and ethical content can also be found within its realm.

Who Uses the Dark Web?
The Dark Web is used by various groups of people for different reasons. Some examples include:
- Journalists and activists: The Dark Web provides a platform for journalists and activists to bypass censorship, protect their privacy, and communicate securely. In repressive regimes, they may rely on the Dark Web to disseminate information, organize movements, and protect freedom of expression.
- Privacy advocates: Individuals who value their privacy may turn to the Dark Web to conduct online activities without being tracked. Particularly concerned about the protection of personal data, they may utilize privacy-focused services available on the Dark Web.
- Individuals involved in illegal activities: Unfortunately, the Dark Web also attracts individuals and criminal organizations involved in illegal activities. Drug dealers, weapon smugglers, counterfeiters, and other criminals utilize the anonymity of the Dark Web to facilitate their illicit trade.

Popular Search Engines:
Some popular search engines used on the Dark Web include:
- TorSearch: TorSearch is a search engine specifically designed for the Tor network. It indexes content on the Dark Web and allows users to search within the Dark Web. TorSearch operates over the Tor network to ensure user anonymity.
- Ahmia: Ahmia is a popular Dark Web search engine. It operates on the Tor network and enables users to search Dark Web content anonymously. Ahmia indexes various sites on the Tor network, providing users with access to the indexed content.
- Candle: Candle is a search engine that indexes Dark Web content. Users can search for Dark Web content by using Onion addresses through Candle and access the search results. Candle assists users in discovering content within the Dark Web.
- Kilos: Kilos is a popular option for searching Dark Web content. Users can utilize Kilos to find illegal products and services such as drugs, weapons, and stolen data. Kilos indexes Dark Web marketplaces and forums, providing users with search capabilities.
- Recon: Recon is a search engine that indexes content from different categories within the Dark Web. Users can search for content on forums, marketplaces, blogs, and other sources using Recon and view the search results. Recon offers users the opportunity to explore Dark Web content.
These search engines enable users to search for and access content within the Dark Web, but it is essential to approach the Dark Web with caution and adhere to legal and ethical guidelines.
Security Warning
Due to the anonymous nature of the Dark Web and the presence of illegal activities, it is associated with security threats. Users must be vigilant, take necessary security precautions, and be mindful of protecting their personal information while navigating the Dark Web. Engaging in illegal activities and exposing oneself to security risks should be avoided.
Conclusion
The Deep Web and Dark Web represent the hidden layers of the internet beyond its visible surface. The Deep Web encompasses content that is not indexed by search engines and requires authorization for access. On the other hand, the Dark Web refers to a subset of the Deep Web that can be accessed through specialized structures, offering anonymity and privacy.
Users should approach the Dark Web with caution, fully understanding its potential risks, and prioritize their security. Emphasizing legal and ethical use, taking necessary security measures, and staying informed are vital steps towards responsible and secure internet usage.
Please note that the content provided is for informational purposes only, and engaging in illegal activities or visiting the Dark Web can have severe legal and security consequences
Honestly the deepweb knowledge really surprised me
I learned more about the dark web and the deep web
I’ve learned many things of this article. thanks for everything. I am so glad that you’ve informed us.