Introduction
Port knocking is a sophisticated technique in network security that serves as a stealthy access control mechanism for sensitive services and endpoints. By requiring a specific sequence of connection attempts across predefined closed ports, port knocking ensures that network services remain concealed from conventional port scans and unauthorized users, effectively making protected services invisible to attackers during initial reconnaissance. This obfuscation supports a defense-in-depth strategy, in which layered security controls make penetrating a network significantly more challenging. Organizations face ever-evolving threats from cyber adversaries who exploit vulnerabilities exposed by open and misconfigured ports. Port knocking addresses these risks by only allowing access to users who can replicate the correct “knock” sequence, which acts as an authentication method and a dynamic firewall rule trigger. When implemented securely—ideally with cryptographic protection and strict access logging—port knocking can mitigate exposure to zero-day vulnerabilities and brute-force scans, thereby improving the resilience of legacy or publicly facing systems.
This guide delivers a detailed technical and strategic examination of port knocking’s operational principles, deployment scenarios, and real-world security implications. Network security professionals and penetration testers will find actionable insights on both attack vectors and defensive mechanisms, enabling them to design and test robust security architectures. By understanding the strengths and caveats of port knocking, IT teams can leverage this tool to reduce attack surfaces, while ensuring critical systems remain protected against unauthorized access.
Learning Objectives
- Understanding the fundamental concepts of port knocking and its role in network security
- Discovering how port knocking mechanisms work and exploring different implementation types
- Identifying potential security risks and attack vectors in port knocking systems
- Understanding how attackers can discover and manipulate port knocking sequences
- Implementing effective defense mechanisms against port knocking threats
- Detection and evaluation of port knocking during penetration tests
- Securely configuring port knocking in real-world scenarios
What is Port Knocking?
Port knocking is a specialized network security mechanism rooted in the idea of security through obscurity, offering an additional layer of defense for servers and networked resources. Instead of exposing sensitive services like SSH directly to the internet, port knocking requires clients to initiate a connection sequence—usually involving TCP, UDP, or even ICMP packets—to a prearranged series of closed ports. The system’s firewall remains strictly closed to outsiders, only opening when the expected “knock” pattern is recognized, minimizing the risk of unauthorized access and automated attacks. From a technical perspective, the process involves sending packets with specific flags (commonly SYN for TCP) to the designated ports. These ports appear shut to scanners, responding with reset (RST) or no reply at all so attackers see no indication that a service exists behind the firewall. Upon correct sequencing, a dedicated daemon (like knockd on Linux) monitors and authenticates the pattern, updating firewall rules in real time to allow temporary access for the originator’s IP address. This ensures that even if the real service port is well-known (e.g., SSH on 22 or RDP on 3389), it remains completely inaccessible until the client gains clearance through this “secret handshake.”
Port knocking’s stealth advantage is particularly evident against automated scanning tools and brute-force bots that flood networks searching for vulnerabilities. Because the protected ports never reply to unsolicited probes, attackers are unable to detect or target the underlying services. For legitimate users—often sysadmins or remote workers—port knocking can be scripted and automated as part of their regular workflow, lowering exposure to threat actors without sacrificing accessibility. This technique is popular in Capture-the-Flag (CTF) contests and ethical hacking labs but is also used in production environments where remote access must be highly restricted. The effectiveness and flexibility of port knocking scale with its configuration. Simple implementations may use static sequences, which are easier to brute force or intercept, while advanced setups employ dynamic rotation, cryptographic validation, or integrate client/server scripts to further obscure the process. Setting timeouts ensures ports aren’t left open for extended periods; the sequence can be reversed or altered to close holes after a session ends. Administrators are advised to use random, unpredictable knock patterns and strong file permissions for configuration files to prevent leaks and misconfiguration abuses.
Despite its strengths, port knocking should be seen as part of a broader security posture, not a standalone solution. Its primary purpose is to reduce visibility and block casual attacks, but it does not substitute robust authentication, regular updates, and vigilant monitoring. When organized with other layers—firewalls, multi-factor authentication, and security event logging—it remains a valuable tool for minimizing risk and improving operational security in challenging network environments.
Key Characteristics of Port Knocking:
- Dynamic Firewall Rules: Port-knocking actively manages firewall rules, ensuring that sensitive service ports are kept closed except for authorized users who trigger the correct sequence. This reduces surface-area exposure for critical systems.
- Obscured Visibility: Enforced port knocking makes protected services invisible to standard scanning and enumeration techniques. Attackers probing the network encounter only closed ports, making target identification extremely challenging.
- IP Address-Based Access: Access privileges are granted only for the requester’s IP address upon passing the knock sequence, preventing relay attacks and broad exploitation of opened ports.
- Timeout Mechanism: Configurable timeouts ensure that ports opened after a valid knock automatically close after a set period, mitigating the risk of lingering access and limiting opportunities for unauthorized intrusion.
- Concealment of Known Ports: Port knocking prevents attackers from learning which ports host important services because those ports remain closed and undiscoverable until the authentication sequence is performed, thereby raising the bar for targeted attacks.
How does Port Knocking Work?
Port knocking operates through a coordinated interplay of network protocols, server-side monitoring, and dynamic firewall management. At a high level, the approach involves making several connection attempts to a specific, secret sequence of closed ports on a server. These attempts are invisible to standard network probes or scans, but they are actively watched by a dedicated port knocking daemon running on the server. By tracking the correct sequence, timing, and source IP address, the system can distinguish legitimate authentication attempts from random background noise or scanning activity. When a client initiates a knocking attempt, it sends packets—typically TCP SYNs, but sometimes UDP or ICMP packets—to each port in the defined order, with each port appearing “closed” to any observer. From the viewpoint of anyone but the intended recipient, the server responds with standard “port closed” behaviors, such as TCP RSTs or dropped packets. However, the monitoring service logs these attempts and determines when the sequence matches the pre-configured key. This logic often includes requirements about how quickly the packets must be sent, enforcing a strict sequence timing window to thwart guesswork or brute force replay.
Upon verification of the knock sequence, the port knocking daemon temporarily adjusts the firewall to open access to a sensitive port, like SSH, from the source IP address that correctly completed the sequence. This dynamic rule remains in place only for a short, predefined period, after which access is revoked, returning the server to its default stealth state. The entire process is stateless for non-participating clients, so attackers performing port scans will see nothing out of the ordinary. The system thereby operates as a form of single-use “secret handshake” layered onto firewall logic, making targeted services functionally invisible until needed. Variations exist within this architecture. Traditional approaches use static sequences; modern strategies might require a dynamically changing knock pattern, cryptographic signatures, or a single encrypted authentication packet as in Single Packet Authorization (SPA). Some implementations offer more granular control, like IP, support for multiple knock patterns, or integration with security information and event management (SIEM) systems for logging and alerting. Timeout settings, state tracking, and automatic removal of stale firewall rules further improve resilience and minimize the attack surface.
Firewall technology is central to port knocking’s effectiveness. Whether using iptables with its “recent” matching module, nftables’ flexible sets and timeouts, or higher-level systems like firewalld, the dynamic injection and removal of rules allows granular, temporary access. Complemented by careful sequence management and robust logging, port knocking becomes a vital component in defense-in-depth for minimizing unwanted exposure and deterring automated reconnaissance tools.
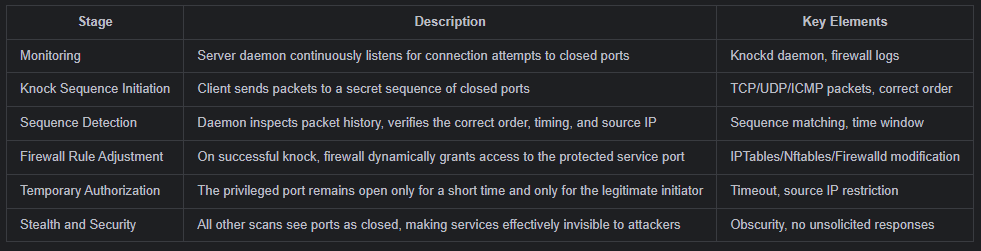
This table provides a structured overview of port knocking’s operation, emphasizing its layered and conditional logic designed to hide, authenticate, and tightly control access to services.
What are the Risks of Port Knocking?
While port knocking can significantly enhance network stealth and help control access to critical services, it is not without substantial security risks. The most prominent vulnerabilities stem from how knock sequences are handled, the cryptographic strength of the implementation, and environmental threats such as misconfiguration or denial-of-service tactics. Unencrypted knock sequences can be trivially captured by attackers monitoring network traffic, and once the sequence is known or published, any host could be leveraged to exploit the system. Unlike robust cryptographic authentication, port knocking relies largely on the secrecy of its sequence—an inherently fragile security principle. Attackers actively target inherent weaknesses such as brute forcing, replay attacks, or IP spoofing, aiming to bypass legitimate access controls. Short sequences or those made up of well-known ports are highly susceptible to automated guessing, and absence of timing constraints further exacerbates this threat. Sophisticated adversaries may flood the target with fake knock attempts or manipulate packets to lock out legitimate users, resulting in denial-of-service. Moreover, the port knocking daemon itself is a critical infrastructure component: if it fails due to load or bug, legitimate users might be locked out, or much worse all services accidentally exposed.
Complexity and administrative burden add to the risks. Port knocking configurations, especially at organizational scale, can be cumbersome to deploy correctly. Unmanaged logs may leak sensitive knock patterns; too many users with knowledge of the sequence dilute its secrecy; poorly scripted firewall updates can inadvertently create backdoors or service downtime. Finally, the technique’s obfuscation properties do not prevent malware actors from abusing it to create hidden communication channels like rootkits or covert C2 further raising the stakes for secure management.
Technical and Attack Vectors:
- Packet sniffing enables attackers to capture knock sequences over unencrypted networks, making future compromise straightforward.
- Brute force attacks are possible on short, predictable, or poorly randomized knock sequences, especially those using common service ports.
- Replay attacks allow reuse of previously captured valid knock attempts unless steps are taken to change sequences dynamically.
- IP spoofing lets unauthorized users impersonate legitimate source IPs, obstructing true users and potentially gaining access.
- Malware, such as rootkits or advanced trojans, may utilize port knocking to open secret communication channels for command and control (C2).
- Excessive failed knock attempts can result in resource exhaustion, crash the port knocking daemon, or trigger unwanted service exposure.
- Non-existent anti-replay or timing verification mechanisms make sequence guessing substantially easier for attackers.
- Insecure protocols (e.g., plain UDP without cryptographic integrity) further facilitate network interception and manipulation.
- Lack of rate-limiting mechanisms allows attackers to flood the server with repeated knock attempts, disrupting legitimate access.
- Attackers monitoring logs or firewall changes can deduce successful knock patterns and automate future intrusions.
Operational and Configuration Weaknesses:
- Disclosure or accidental publication of knock sequences in mismanaged logs, documentation, or public repositories compromises security.
- Firewall misconfiguration—including unintended open rules or timeouts—creates silent exposure of services to unauthorized users.
- Ineffective or missing timeout mechanisms lead to ports remaining open longer than necessary, increasing vulnerability window.
- Insufficient intrusion detection and alerting mechanisms obscure when knock abuse or attack attempts occur.
- Too many users or administrators know the secret sequence, lowering the chances that secrecy can be preserved.
- Port knocking daemon failures represent a single point of access and reliability risk for both security and availability.
- Uncoordinated or incompatible software upgrades may break port knocking integrations, leaving services unprotected.
- Lack of SIEM (Security Information and Event Management) integration, making it difficult to correlate and analyze suspicious activity.
- Port knocking may block legitimate emergency access for incident response teams or administrators during outages.
- Weak encryption or poor sequence protection in configuration files, scripts, or automation logic creates latent vulnerabilities exploitable by attackers.

Port Knocking Attack and Defense
Port knocking mechanisms are both a target for attackers and a valuable line of defense in security architecture. Attackers—especially penetration testers—focus on capturing, replaying, or brute-forcing the knock sequence, while defenders build countermeasures like dynamic sequences, cryptographic protections, and rate limiting. The offensive-defensive interplay often determines whether port knocking serves as an effective stealth gate or becomes an exploitable weak link.
Attack Techniques and Practical Examples:
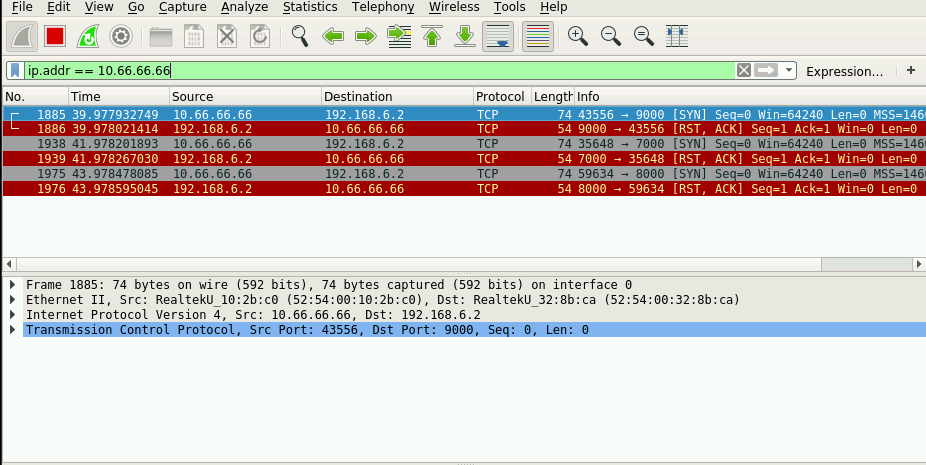
A primary attack is passive sniffing. Using tools like tcpdump or Wireshark, an attacker on the same segment can capture the legitimate user’s knock sequence:
sudo tcpdump -i eth0 -n dst 192.168.1.105 and 'tcp[tcpflags] & tcp-syn != 0' -w knock_capture.pcap
# Analyze with Wireshark: display destination ports in orderAfter collecting the sequence (e.g., 7000, 8000, 9000), it can be replayed on demand:
knock -v 192.168.1.105 7000 8000 9000
# SSH is now open for the attacker's IPAnother approach is brute force. If the system uses a weak, short, or well-known sequence, an attacker can cycle combinations via a script:
for p1 in {1000..1100}; do for p2 in {1000..1100}; do for p3 in {1000..1100}; do knock 192.168.1.105 $p1 $p2 $p3; done; done; doneWithout rate-limiting, a correct sequence discovery opens the protected port.
Replay attacks are also viable when an attacker records legitimate traffic and retransmits the sequence—even weeks after the original capture. Using a Python Scapy script, attackers reconstruct TCP SYN packets to replay any sequence at will.
Notification systems can alert administrators to brute force or reconnaissance behavior as soon as it starts.
Port knocking can be very effective when layered with strong operational practices—dynamic sequences, cryptographic authentication, logging, and rate limiting—ensuring that even if attackers monitor or probe the system, service exposure cannot be automated or trivially exploited. Conversely, poor implementation (static sequences, unencrypted knocks, or missing timeouts) makes the system easy prey for even basic penetration testers or malware.

How can you Protect Against Port Knocking?
Securing port knocking systems requires a multi-layered approach combining cryptographic validation, dynamic sequence generation, and rigorous operational controls. The most effective implementations use Single Packet Authorization (SPA) with HMAC signatures rather than traditional multi-port sequences. In an SPA setup using fwknop, the client generates an encrypted, authenticated packet containing the current timestamp, destination port, and HMAC-SHA256 signature derived from a shared secret. The server daemon validates both the signature and timestamp freshness before modifying firewall rules. This approach eliminates replay attacks since each packet includes a unique timestamp that expires within seconds:
# Client sends SPA packet
$ fwknop -A tcp/22 -a 192.168.56.50 -D 192.168.1.105 --key-gen
# Server validates and opens port only if HMAC matches and timestamp is fresh
$ tail -f /var/log/fwknop/fwknopd.log
[+] SPA Packet from IP: 192.168.56.50 received with valid HMAC
[+] Command executed: iptables -I INPUT 1 -s 192.168.56.50 -p tcp --dport 22 -j ACCEPT
[+] Timeout set: 30 secondsThe encrypted payload ensures that even if an attacker captures the UDP packet, they cannot forge a valid one without the shared secret. Compare this to traditional port knocking where captured sequences remain exploitable indefinitely.
Dynamic sequence rotation adds another critical layer by preventing pattern recognition and brute force attempts. Organizations can implement TOTP-based sequences synchronized between client and server, where the knock sequence changes every 30 seconds based on a time-based algorithm:
#!/usr/bin/env python3
import pyotp
import subprocess
import time
SHARED_SECRET = "JBSWY3DPEHPK3PXP" # Pre-shared between client and server
SERVER_IP = "192.168.1.105"
def get_dynamic_sequence():
totp = pyotp.TOTP(SHARED_SECRET, interval=30)
otp = totp.now()
# Convert 6-digit OTP to three ports
port1 = 8000 + int(otp[0:2])
port2 = 9000 + int(otp[2:4])
port3 = 10000 + int(otp[4:6])
return [port1, port2, port3]
# Client executes knock with current time-based sequence
sequence = get_dynamic_sequence()
print(f"[*] Current knock sequence: {sequence}")
subprocess.run(["knock", SERVER_IP] + [str(p) for p in sequence])On the server side, knockd validates incoming sequences against the same TOTP algorithm. When an attacker captures a sequence at 12:00:00, it becomes invalid at 12:00:31—eliminating replay attack viability:
# Server-side validation log
$ cat /var/log/knockd.log
[2025-11-04 12:00:15] Valid sequence from 192.168.56.50: 8032->9056->10078
[2025-11-04 12:00:45] Invalid sequence from 192.168.56.101: 8032->9056->10078 (expired)Automated defense mechanisms through rate limiting and IP-based blocking prevent brute force and reconnaissance attempts. Integrating Fail2ban with knockd logs provides real-time protection by automatically blocking IPs that exceed failed knock thresholds:
# /etc/fail2ban/filter.d/knockd.conf
[Definition]
failregex = ^<HOST>: invalid sequence
ignoreregex =
# /etc/fail2ban/jail.d/knockd.conf
[knockd]
enabled = true
filter = knockd
logpath = /var/log/knockd.log
maxretry = 5
findtime = 600
bantime = 3600
action = iptables-allports[name=knockd]After configuration, Fail2ban monitors knock attempts and enforces bans automatically:
$ sudo fail2ban-client status knockd
Status for the jail: knockd
|- Filter
| |- Currently failed: 8
| |- Total failed: 23
| `- File list: /var/log/knockd.log
`- Actions
|- Currently banned: 3
|- Total banned: 3
`- Banned IP list: 192.168.56.101 10.0.0.45 172.16.0.88
$ sudo iptables -L f2b-knockd -n
Chain f2b-knockd (1 references)
DROP all -- 192.168.56.101 0.0.0.0/0
DROP all -- 10.0.0.45 0.0.0.0/0
DROP all -- 172.16.0.88 0.0.0.0/0Additionally, implement strict timeout mechanisms using nftables’ native set expiration to automatically close ports after brief access windows:
# /etc/nftables.conf
table inet portknock {
set allowed_ips {
type ipv4_addr
flags timeout
timeout 30s
}
chain input {
type filter hook input priority 0;
tcp dport 22 ip saddr @allowed_ips accept
tcp dport 22 drop
}
}When a valid knock occurs, the IP is added to the allowed_ips set and automatically removed after 30 seconds—no manual cleanup required. Comprehensive logging to SIEM systems completes the defense posture
# rsyslog forwarding configuration
*.* @siem-server.example.com:514
# Sample SIEM alert rule
if knockd.invalid_attempts > 10 within 5min:
alert("Possible port knock brute force from {source_ip}")
block_ip({source_ip}, duration=3600)This multi-faceted approach—cryptographic validation, dynamic sequences, automated blocking, and granular timeouts—transforms port knocking from a weak obscurity mechanism into a hardened access control layer.
Conclusion
Port knocking remains a practical and stealthy method for strengthening access control to critical network services. By keeping ports closed to traditional scans and requiring a secret knock sequence, administrators reduce both the visibility of services to attackers and the attackable surface area of a network. This “security by obscurity” deters opportunistic targeting and drives up the complexity and effort required for adversaries to find and exploit vulnerabilities. Properly implemented, port knocking can quickly adapt firewall rules to allow connection only for those who know and execute the right sequence at the right time. However, the security value of port knocking depends entirely on effective integration with other protective measures and avoidance of common pitfalls. Simple static knock sequences and lack of encryption expose systems to sniffing, replay, and brute force attacks—especially on flat networks or when sequences leak in logs or documentation. Maintaining randomness, using cryptographic authentication (such as HMAC or SPA), and employing dynamic or periodic sequence changes are necessary steps to make port knocking resilient. Organizations must also invest in logging, monitoring, automatic banning of repeat failures, and regular updates to knock configurations to minimize the risks stemming from misconfiguration, daemon failure, or user error.
Ultimately, port knocking is best seen as a supportive security layer—never a replacement for strong authentication, multi-factor access control, intrusion detection, and reliable network hygiene. Its strengths lie in providing low-friction service obfuscation and temporary dynamic access. But for truly secure infrastructure, port knocking should be deployed alongside robust measures like SSH keys, network segmentation, rate limiting, SIEM integrations, and vigilant operational monitoring. When used judiciously within a defense-in-depth strategy, it remains a relevant and practical tool for administrators, penetration testers, and any organization seeking to conceal key services without sacrificing usability or manageability.
Question and answer
Port knocking is a security technique that keeps network service ports (like SSH) closed and hidden from unauthorized scans. It requires a user to attempt connections to a secret sequence of closed ports before the firewall temporarily opens access. This method reduces a system’s exposure to automated attacks and opportunistic scanning, making it harder for attackers to find and target critical services.
Traditional port knocking sequences can be sniffed over the network if unencrypted, replayed by attackers, or brute-forced if they are too short or predictable. Static sequences and lack of timing controls make these implementations vulnerable to observation, logging leaks, and automated guessing. Without cryptographic protections, anyone who learns the knock sequence can bypass security.
An attacker monitors network traffic with tools like tcpdump or Wireshark, capturing packets directed at a server. By filtering on destination ports and observing repeated sequences, the attacker identifies the knock pattern. The sequence can then be replayed from another host using port knocking clients or custom scripts, granting unauthorized temporary access to the protected service.
SPA uses a single, encrypted packet with an HMAC signature and timestamp instead of multiple connection attempts. This packet is validated by the server daemon to ensure authenticity and freshness. Unlike traditional port knocking, SPA is immune to sniffing and replay attacks without access to the shared secret, significantly improving security. Tools like fwknop implement SPA in practice.
Best practices include using dynamic or time-based knock sequences (TOTP), encrypting all knock traffic with HMAC signatures, limiting knock attempts per IP using tools like Fail2ban, enforcing strict firewall timeouts, and rotating knock patterns periodically. Comprehensive logging and integration with SIEM systems allow rapid detection and response to attack attempts.
References:

