Introduction
In the digital age, the Domain Name System (DNS) plays a pivotal role in translating human-readable domain names into IP addresses. With the rising number of cyber threats targeting DNS infrastructure, monitoring DNS traffic has become essential for network administrators and security professionals. This is where a DNS traffic analysis tool comes in handy. The DNSWatch project is designed to provide a robust solution for monitoring and analyzing DNS traffic, detecting anomalies, and helping users gain insights into their network’s DNS activity.
Learning Objectives
By the end of this article, you will:
- Understand the purpose and functionality of the DNSWatch project.
- Learn how DNSWatch works and its core features.
- Know how to download, install, and use DNSWatch effectively for DNS traffic monitoring.
- See practical examples of how to use DNSWatch for network security and troubleshooting.
What is the DNSWatch Project?
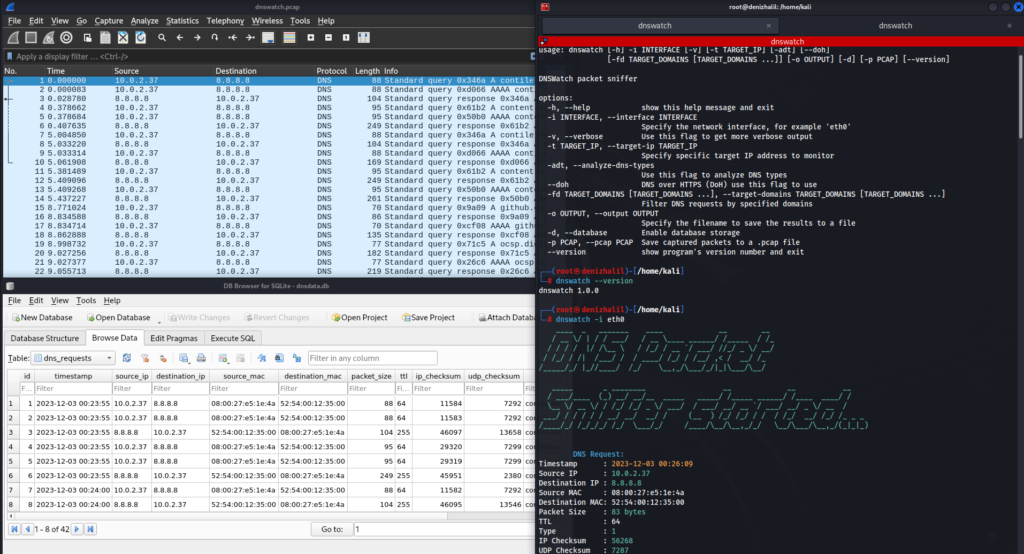
DNSWatch is a Python-based packet sniffing tool developed to help users monitor and analyze DNS traffic on a network. Whether you’re an IT professional, network administrator, or cybersecurity enthusiast, DNSWatch offers a comprehensive set of features for analyzing DNS queries, detecting suspicious activities, and improving overall network security. Its capabilities extend to filtering DNS traffic, analyzing DNS response types, using DNS over HTTPS (DoH), and even enabling a DNS firewall mode for enhanced protection.
How Does DNSWatch Work?
DNSWatch leverages the power of scapy, a Python library for network packet manipulation, to sniff and analyze DNS packets on a specified network interface. The tool listens for DNS requests and responses, providing detailed insights into the type, source, destination, and content of DNS traffic. It allows users to apply various filters, including IP address, DNS type, and port, to narrow down traffic analysis. DNSWatch also offers the ability to save traffic data into PCAP files for further analysis or use with other network analysis tools, DNS Security Tool: Monitoring and Detecting DDoS/DoS Attacks with Python.
The tool’s DNS firewall mode detects and alerts on potential DNS spoofing attempts, helping protect the integrity of DNS traffic in real-time.
Key Features of DNSWatch
- DNS Packet Sniffing: Monitors DNS packets on a user-specified network interface.
- Verbose Output: Provides detailed, in-depth information if verbose mode is enabled.
- Target IP Analysis: Allows monitoring of DNS responses associated with a specific IP address.
- DNS Type Filtering: Analyzes different DNS request types (e.g., A, MX, AAAA, etc.).
- DNS over HTTPS (DoH): Enables DNS resolution using DNS over HTTPS, providing an additional layer of privacy.
- Port and IP Filtering: Filters packets by source or destination port/IP address.
- PCAP File Saving: Saves captured packets into PCAP format for later analysis.
- DNS Firewall Mode: Detects DNS spoofing attempts and other suspicious activities.
- Threshold and Window Size Settings: Allows users to customize monitoring parameters, such as the number of DNS queries per second and the time window for analysis.
Downloading DNSWatch from GitHub
DNSWatch is freely available on GitHub and can be easily installed and set up by following the instructions below.
Step 1: Clone the repository
git clone https://github.com/HalilDeniz/DNSWatch.gitStep 2: Install the required dependencies
pip install -r requirements.txtThe dependencies include:
- Python 3.7+
- scapy 2.4.5+ (for network packet manipulation)
- colorama 0.4.4+ (for color-coded output)
Example Usage of DNSWatch
Here are some practical examples of how to use DNSWatch in real-world scenarios:
- 1. Basic DNS Traffic Monitoring: Start monitoring DNS traffic on the default network interface.
$ python dnswatch.py- 2. Monitor DNS Traffic on a Specific Interface: Specify the network interface to capture DNS traffic (e.g.,
eth0).
$ python dnswatch.py -i eth0- 3. Analyze DNS Traffic for a Target IP: Monitor DNS queries and responses related to a specific IP address.
$ python dnswatch.py -t 192.168.1.1- 4. Enable DNS over HTTPS (DoH): Secure DNS resolution by using DNS over HTTPS.
$ python dnswatch.py --doh- 5. Save Captured Packets to a PCAP File: Capture DNS traffic and save it for future analysis
$ python dnswatch.py --pcap-file dns_traffic.pcap- 6. Activate DNS Firewall Mode: Detect DNS spoofing attempts and protect your network.
$ python dnswatch.py --firewall- 7. Customizing Threshold and Window Size: Configure the DNS firewall with a specific threshold and window size.
$ python dnswatch.py --firewall --threshold 100 --window-size 120Conclusion
DNSWatch is a powerful and flexible tool for monitoring DNS traffic, offering a range of features to enhance network security. Whether you are troubleshooting DNS issues, detecting suspicious activities, or just curious about your network’s DNS traffic, DNSWatch provides the capabilities to gain valuable insights. The open-source nature of DNSWatch allows users to customize the tool to their specific needs, making it a valuable addition to any cybersecurity toolkit.
By following the steps in this article, you should now be equipped to download, install, and use DNSWatch to safeguard your network’s DNS infrastructure. As DNS continues to be a target for attackers, tools like DNSWatch are essential for proactive network defense.
