Introduction
Discovering devices on a network is a critical task for network administrators and security experts. In this article, we will learn how to perform ARP (Address Resolution Protocol) discovery using the Python Scapy library and explore how we can use it to find devices on the network.
Learning Objectives
- Gain basic knowledge about the operation of the ARP protocol
- Understand outgoing and incoming ARP packets
- Learn the process of detecting devices on the network
A Brief Introduction to ARP
ARP (Address Resolution Protocol) is a network protocol used to translate IP addresses into MAC addresses. ARP discovery is commonly used to find devices on a network. For more, you can check here.
Outgoing ARP Packet (ARP Request):
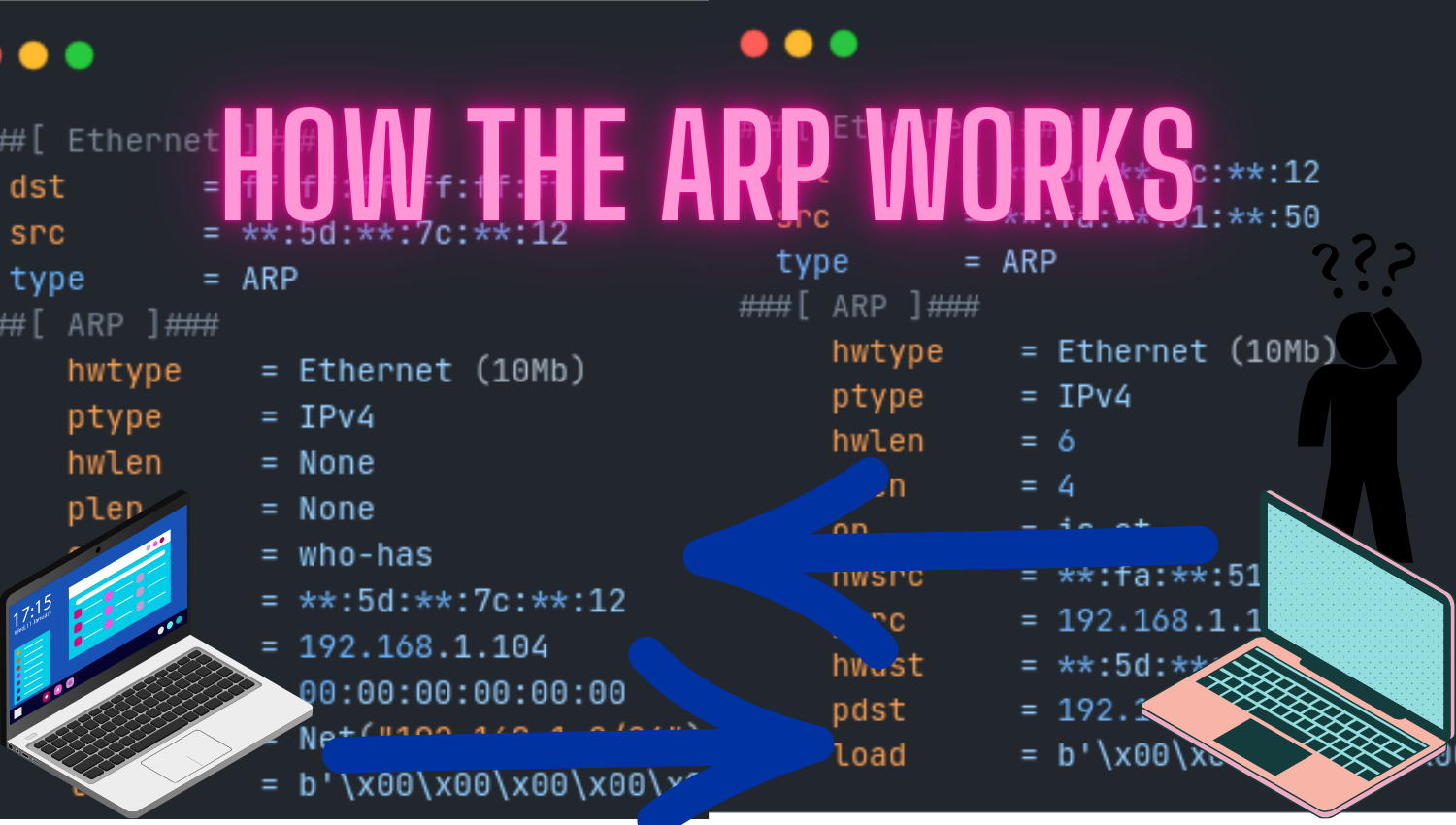
First, our program sends ARP requests to devices in a specific IP range. This request is sent to learn the MAC addresses of devices with the target IP address. Let’s now examine the outgoing ARP request(Mac Changer):
###[ Ethernet ]###
dst = ff:ff:ff:ff:ff:ff
src = **:5d:**:7c:**:12
type = ARP
###[ ARP ]###
hwtype = Ethernet (10Mb)
ptype = IPv4
hwlen = None
plen = None
op = who-has
hwsrc = **:5d:**:7c:**:12
psrc = 192.168.1.104
hwdst = 00:00:00:00:00:00
pdst = Net("192.168.1.0/24")
load = b'\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00'The above packet represents an ARP request. It contains an Ethernet frame with the destination MAC address ff:ff:ff:ff:ff:ff. The ARP packet is sent with the who-has operation code, meaning it queries the MAC address of the target. The MAC address of the sender device is set to **:5d:**:7c:**:12, and the IP address is 192.168.1.104. hwtype specifies the Ethernet (10Mb) hardware type, ptype specifies the IPv4 protocol type, hwlen and plen specify the lengths of hardware and protocol addresses. The load part represents the padding payload.
Incoming ARP Packet (ARP Reply):
In response to the ARP request sent, devices with the target IP address send ARP replies. These replies contain the information of the target MAC address. Here is the content of an ARP reply:
###[ Ethernet ]###
dst = **:5d:**:7c:**:12
src = **:fa:**:51:**:50
type = ARP
###[ ARP ]###
hwtype = Ethernet (10Mb)
ptype = IPv4
hwlen = 6
plen = 4
op = is-at
hwsrc = **:fa:**:51:**:50
psrc = 192.168.1.1
hwdst = **:5d:**:7c:**:12
pdst = 192.168.1.104
load = b'\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00'The above packet represents an ARP reply. This packet is sent with the is-at operation code, meaning it is a response to the MAC address of the target. The MAC address of the responding device is **:fa:**:51:**:50, and the IP address is 192.168.1.1. The packet is carried by an Ethernet frame with the MAC address of the sender device set to **:5d:**:7c:**:12.
Conclusion:
Performing ARP discovery with Python provides a powerful tool for network administrators and security experts to detect devices on the network and enhance network security. In this article, we discussed the basics of the ARP protocol, the importance of understanding outgoing and incoming ARP packets, and the process of detecting devices on the network using Python Scapy. With this knowledge, you can effectively manage your network.