Introduction
In the rapidly evolving digital landscape of today, where the internet has become an integral part of our daily lives, the importance of online privacy and security has never been more pronounced. Individuals and organizations alike are increasingly aware of the potential risks associated with sharing personal information online, and as a result, they are seeking effective solutions to safeguard their data and maintain their anonymity. In this context, proxy servers emerge as vital tools that not only facilitate secure internet access but also provide various advantages that enhance the overall online experience. This article aims to explore the concept of a proxy, elucidate its operational mechanisms, outline its numerous benefits, and explain why utilizing a proxy connection can be a prudent choice for anyone navigating the complexities of the internet.
Learning Objectives
By engaging with this article, readers will be equipped with a comprehensive understanding of several key concepts, including:
- The fundamental definition and function of proxy servers.
- The intricate workings of how a proxy operates in relation to user requests.
- The diverse benefits that arise from employing a proxy connection.
- Compelling reasons to consider integrating a proxy into one’s online activities.
What is a Proxy?
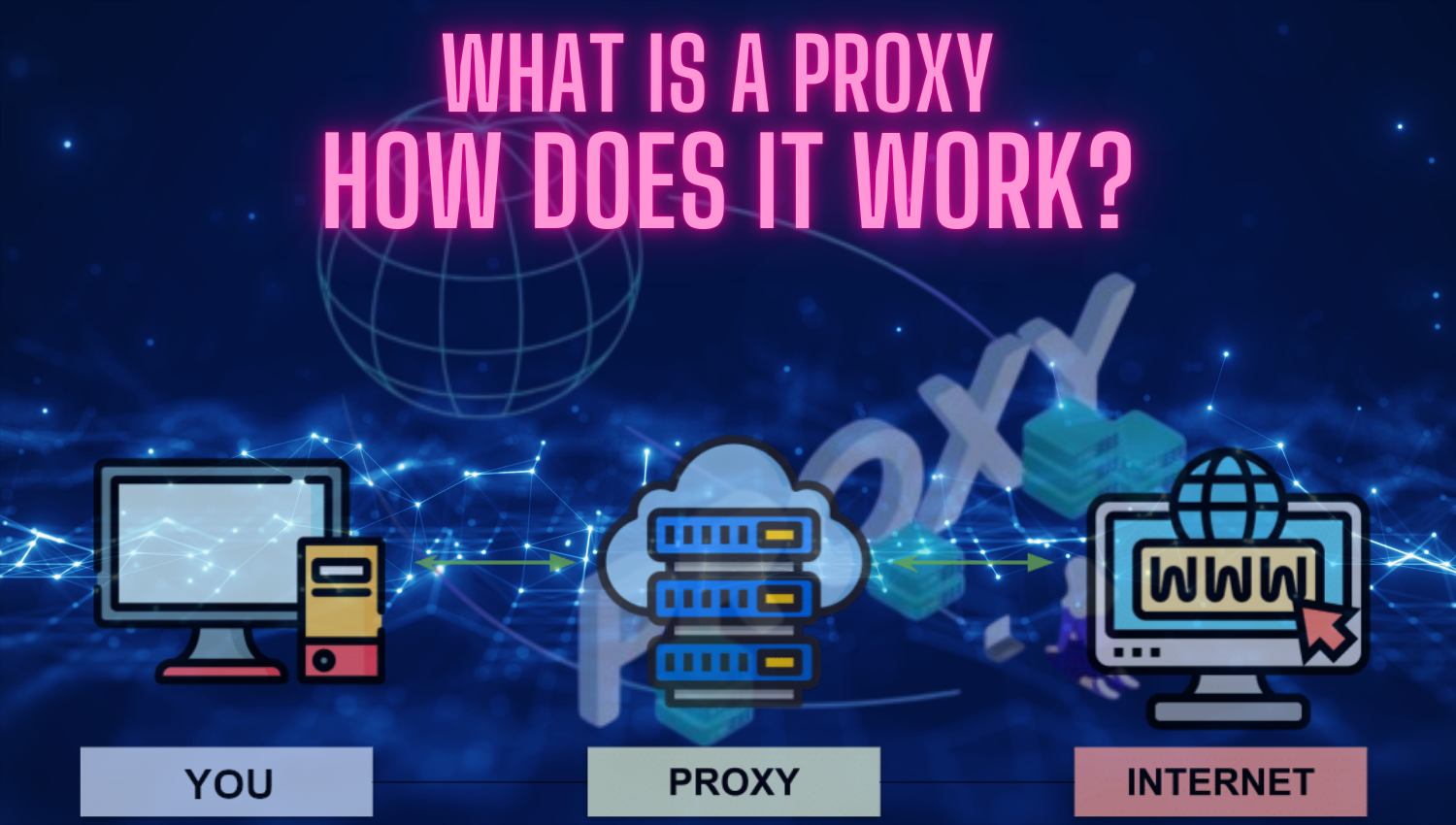
At its core, a proxy is an intermediary server that acts as a gateway between users and the vast expanse of the internet. When an individual wishes to access a particular website or online resource, their request is first directed to the proxy server rather than going straight to the target web server. The proxy server then processes this request and forwards it to the appropriate destination while concealing the user’s real IP address in the process. This mechanism serves multiple purposes, primarily focused on enhancing security and preserving user privacy.
Proxy servers can be categorized into two primary types: forward proxies and reverse proxies.
- Forward Proxy: This type of proxy is designed to forward requests from users to the internet at large. It is particularly useful for individuals seeking to bypass geographical restrictions or access content that may be blocked in their region. By routing requests through a forward proxy, users can effectively mask their location and appear as if they are accessing the internet from a different geographical area.
- Reverse Proxy: In contrast to forward proxies, reverse proxies manage incoming requests directed at web servers. They serve various functions such as load balancing, which distributes incoming traffic across multiple servers to optimize performance; caching, which stores copies of frequently accessed content to improve retrieval speeds; and enhancing security by acting as an additional barrier between users and web servers.
Both types of proxies serve distinct purposes and provide unique advantages tailored to different use cases.
How Does a Proxy Work?
The operational mechanics of a proxy server can be broken down into several detailed steps that illustrate how user requests are processed:
- User Request: When an individual enters a URL into their web browser, this action initiates a request for information from that specific website.
- Proxy Interception: Instead of sending this request directly to the target web server, the browser routes it through the configured proxy server. This step is crucial as it allows the proxy to take control of the request before it reaches its final destination.
- Request Forwarding: Upon receiving the request from the user’s device, the proxy server processes it and forwards it to the target web server using its own IP address rather than that of the user. This step effectively anonymizes the user’s identity by masking their original IP address.
- Response Handling: After processing the request, the target web server sends back the requested data or content to the proxy server instead of directly returning it to the user.
- Data Return: Finally, once the proxy server receives this data from the web server, it forwards it back to the user’s device. At this point, the user can view or interact with the requested content without ever having directly exposed their IP address or location.
This entire process not only facilitates secure browsing but also enables users to access content that may otherwise be restricted due to geographical limitations or organizational policies.

Benefits of Using a Proxy Connection
Utilizing a proxy connection offers several significant advantages that enhance both security and usability:
- Anonymity: One of the most compelling reasons for using a proxy is its ability to provide anonymity while browsing online. By masking users’ IP addresses, proxies make it considerably more challenging for third parties—such as advertisers or malicious entities—to track users’ online activities or gather personal information about them.
- Enhanced Security: Proxy servers can act as an additional layer of security by scanning incoming data for potential threats such as malware or phishing attempts before they reach users’ devices. Furthermore, many proxies offer encryption features that protect sensitive information during transmission over public networks.
- Access Control: Organizations often implement proxies as part of their network infrastructure to enforce access controls on employee internet usage. By doing so, they can restrict access to specific websites deemed inappropriate or non-work-related, thereby improving productivity and reducing distractions in professional environments.
- Performance Improvement: Proxies can significantly enhance performance by caching frequently accessed websites and resources. When users request content that has been cached by the proxy server, retrieval times are dramatically reduced since data can be served quickly without needing to fetch it again from the original web server.
- Bypassing Geographical Restrictions: Many websites impose geographical restrictions on their content based on users’ locations. By using a proxy located in a different region or country, users can effectively bypass these restrictions and gain access to otherwise unavailable content—be it streaming services, news articles, or other resources.
Why Should You Use a Proxy Connection?
There are numerous compelling reasons why individuals and organizations should consider integrating a proxy connection into their online activities:
- Privacy Protection: In an age where digital privacy is increasingly under threat from various sources—including hackers, advertisers, and even governments—using a proxy provides greater anonymity while browsing. Users can navigate online spaces without fear of being tracked or monitored.
- Bypassing Geographical Restrictions: For those who travel frequently or reside in regions with restricted internet access, proxies offer an effective means of circumventing these limitations. Whether it’s accessing streaming services like Netflix or social media platforms blocked in certain countries, proxies enable users to connect freely.
- Speed and Performance Boost: With caching capabilities built into many proxies, users experience faster loading times for frequently visited sites. This performance boost is especially beneficial during peak usage hours when network congestion may slow down direct connections.
- Network Security: For businesses concerned about data breaches and cyber threats, implementing proxy servers enhances overall network security by providing an additional layer of protection against potential attacks. Proxies can monitor traffic patterns for suspicious activity and help mitigate risks before they escalate into serious issues.
Conclusion
In summary, proxy servers are indispensable tools that significantly enhance users’ online experiences by providing essential features such as anonymity, security, and access control. They offer valuable benefits for both individual users seeking privacy during their browsing sessions and organizations aiming to protect sensitive information while managing employee internet usage effectively. If you are looking for ways to achieve a more secure and private browsing experience on the internet, considering connection could prove advantageous in navigating today’s complex digital landscape.
Ultimately, leveraging appropriate tools like proxy servers is crucial for maximizing opportunities while minimizing risks associated with online activities. By adopting these technologies, you can safeguard your online privacy while simultaneously improving your overall internet experience. If you desire greater control over your browsing habits coupled with enhanced security measures, utilizing a proxy connection may very well be an ideal solution tailored to your needs in this interconnected world.