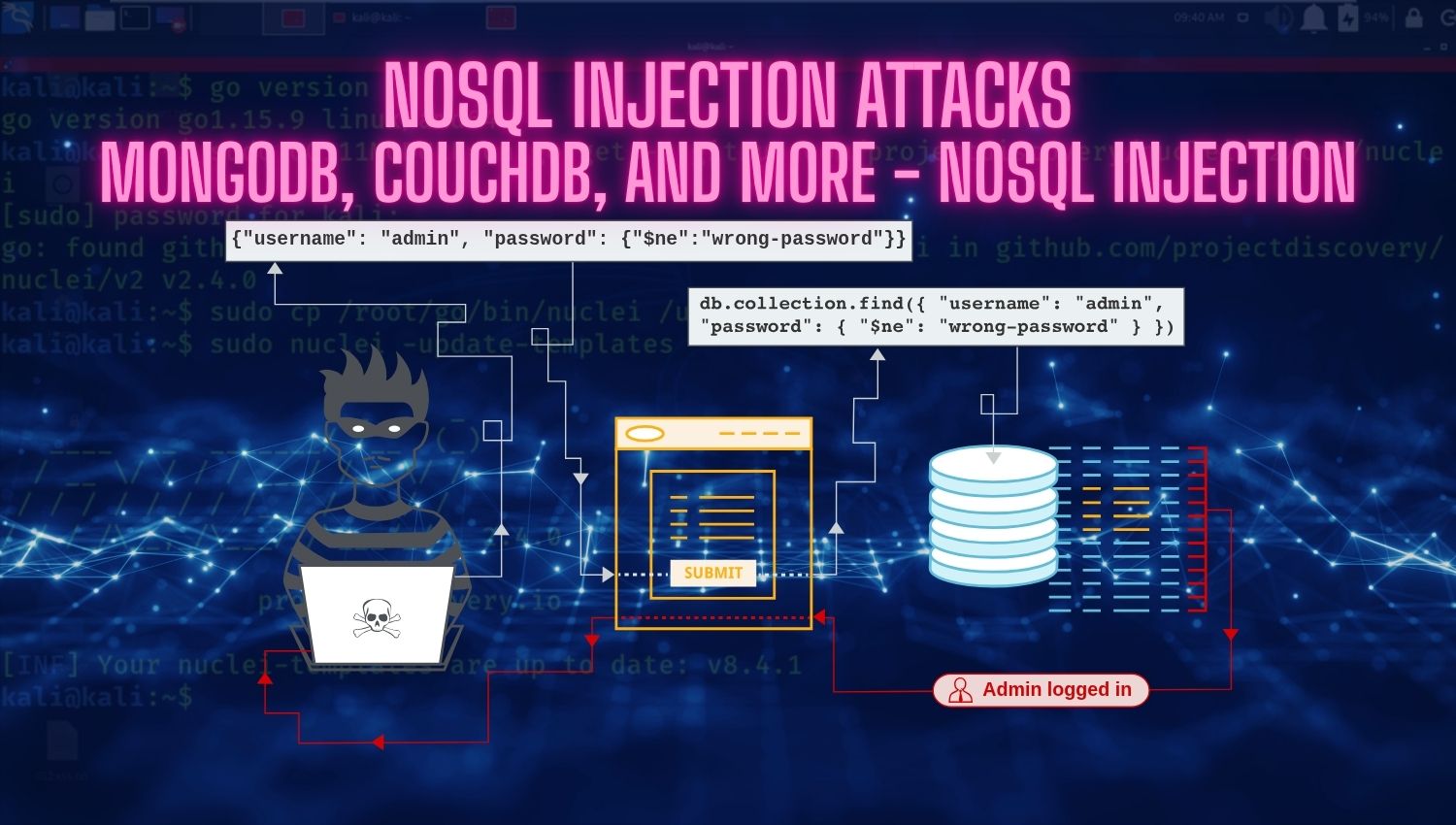
NoSQL Injection Attacks: MongoDB, CouchDB, and More – NoSQL injection
Introduction NoSQL databases have transformed how modern applications store and manage data, offering unparalleled scalability, flexibility, and performance compared to traditional relational databases. MongoDB, CouchDB, Redis, Elasticsearch, and Cassandra have become foundational technologies in cloud-native and microservices architectures. However, this architectural flexibility introduces unique security challenges that many developers overlook. NoSQL injection has emerged as one of the most dangerous and frequently exploited vulnerabilities in contemporary