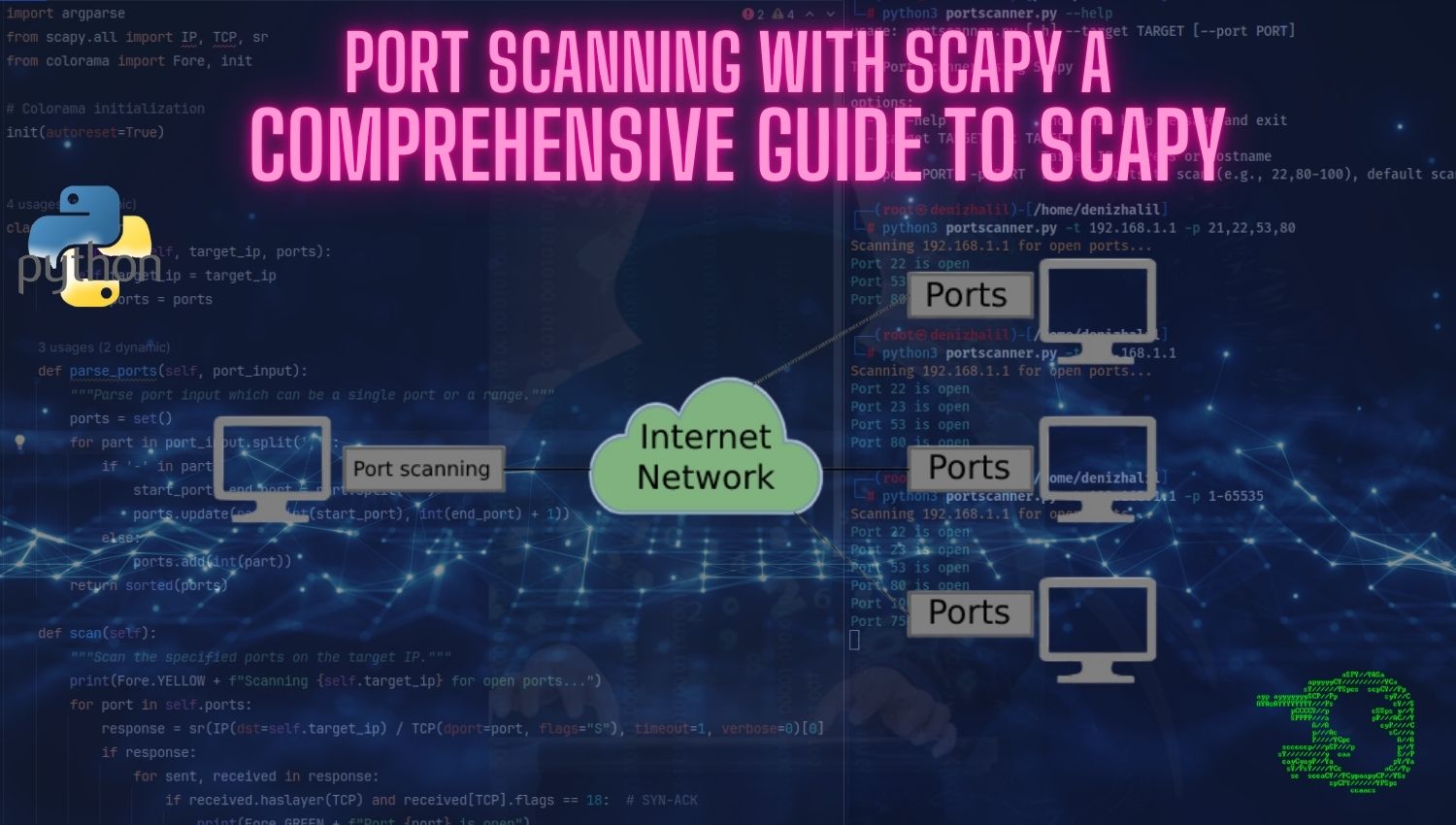
Spoofing Packets with Scapy: A Comprehensive Guide
Introduction In the world of network security, understanding how data packets traverse through networks is crucial. One of the most powerful tools available for packet manipulation is Scapy, a Python-based interactive packet manipulation program. Scapy allows users to create, send, and analyze network packets, making it an essential tool for network engineers, security professionals, and researchers. This guide will delve into the process of sending