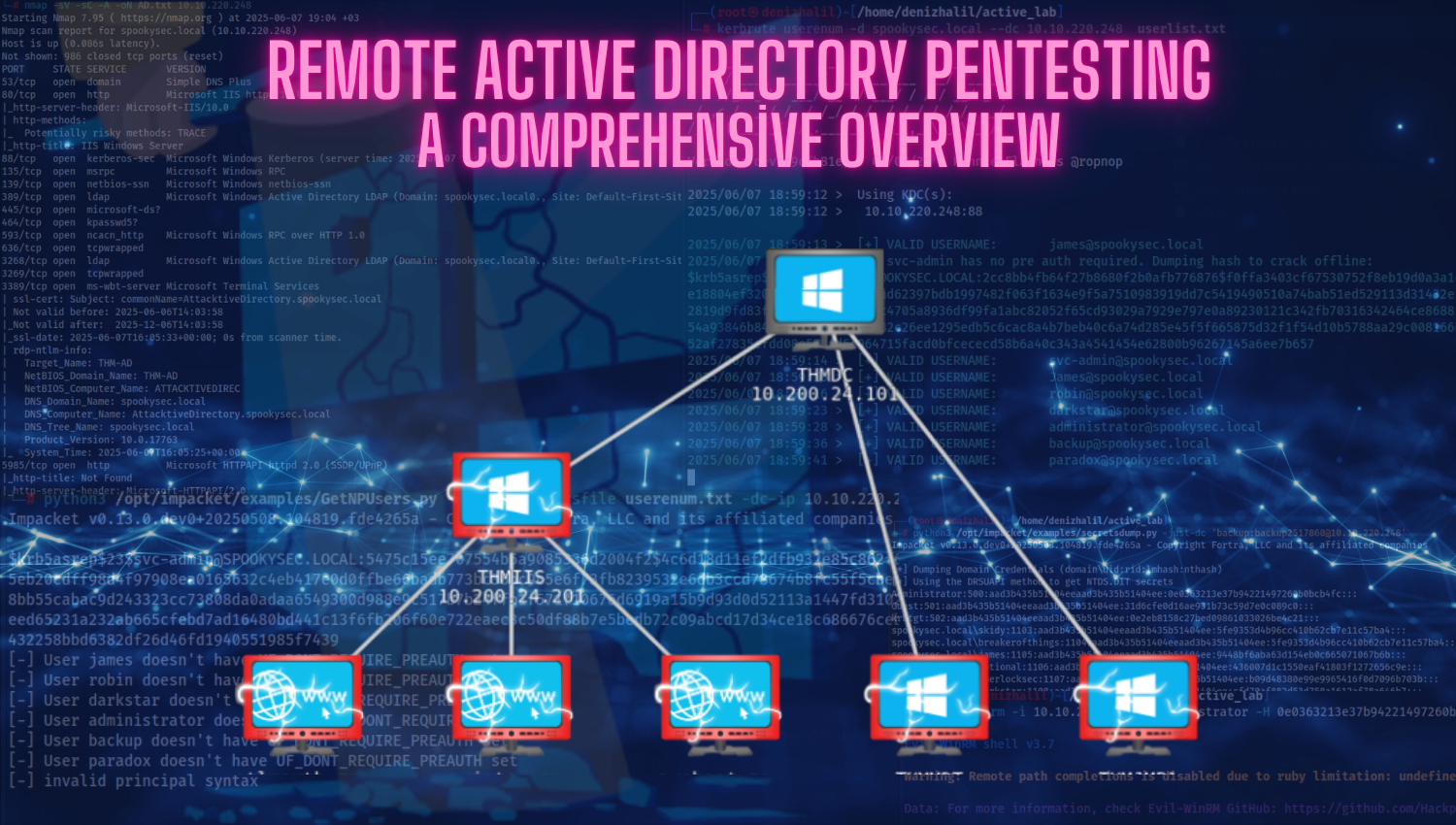
Remote Active Directory Pentesting: A Comprehensive Overview
Introduction Active Directory (AD) serves as the central nervous system for identity and access management in enterprise environments, governing user authentication, resource permissions, and group policies across networks. Despite its critical role, AD environments are frequent targets for attackers due to inherent complexities and common misconfigurations—such as overly permissive access controls, legacy protocol support (e.g., NTLMv1), and unpatched vulnerabilities. Remote Active Directory pentesting simulates adversarial tactics to