Introduction
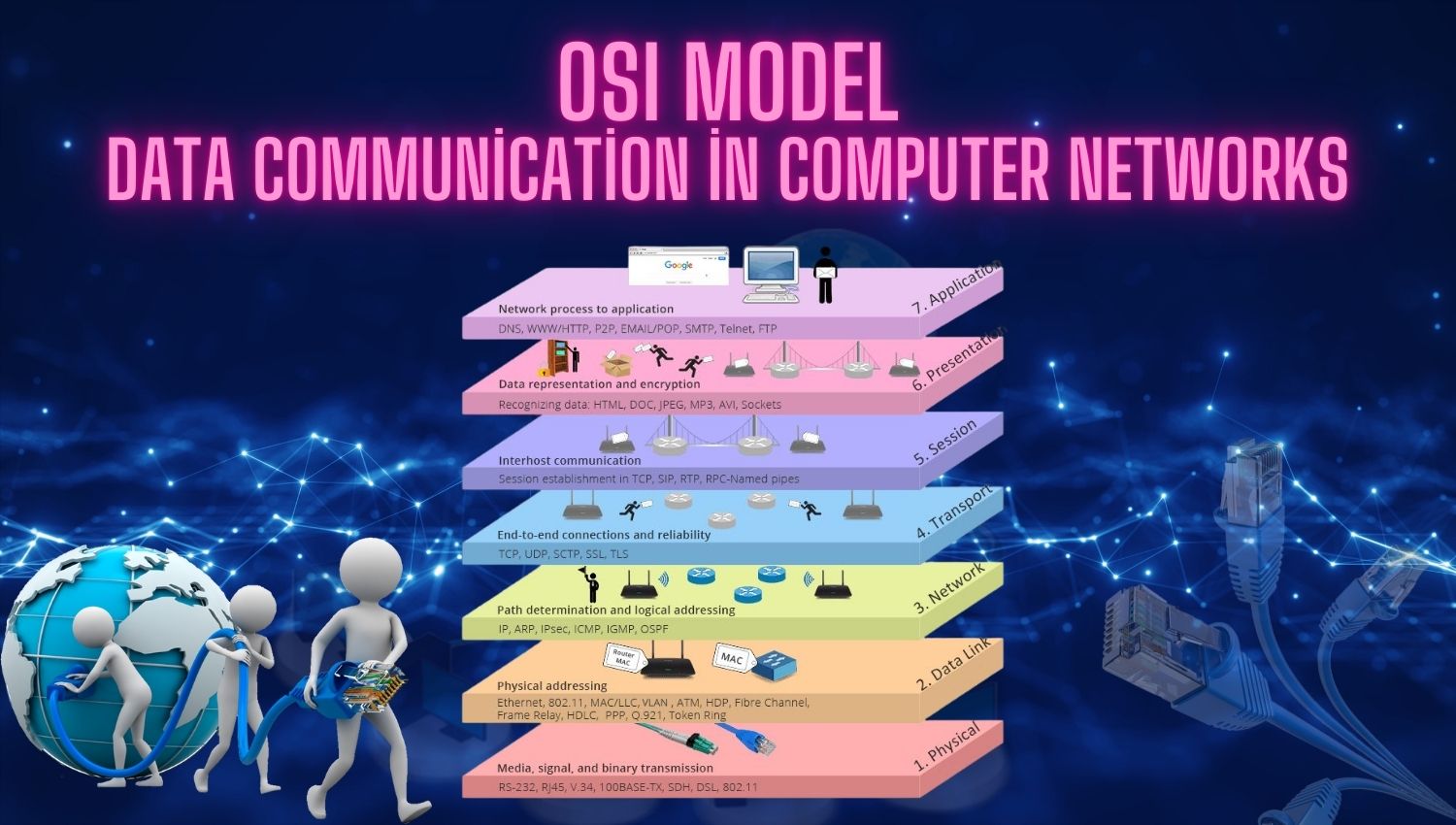
In today’s complex computer networks, the accurate, secure, and rapid transmission of data is of vital importance. To manage these processes in a more understandable and systematic way, the OSI (Open Systems Interconnection) model was developed as a fundamental reference point for network communication. The OSI model divides network functions into seven layers, allowing each layer to perform different tasks. In this article, we will examine what the OSI model is, the functions of each layer, and their roles in network communication. We will clarify the workings of the OSI model with real-life scenarios.
Learning Objectives
By reading this article, you will aim to learn:
- The structure and purpose of the OSI model
- The function of each layer and its place in network communication
- To make the OSI model more tangible through a scenario
- How the functions of OSI layers are applied in computer networks
What is the OSI Model?
The OSI (Open Systems Interconnection) model is an international reference model developed to regulate data communication between different devices and networks. This model divides the communication process into seven different layers to better understand and manage data. Each layer performs specific functions and works in collaboration with other layers. This structure simplifies complex data transmission processes and makes transparent the stages through which data passes from the source to the destination. The OSI model also provides standards to ensure interoperability between hardware and software from different manufacturers. Thus, it becomes possible for different platforms and systems to exchange data over the same network, Guide to Learning Computer Networks.
Explaining the OSI Model with a Scenario
Consider wanting to watch a video from a web browser. This seemingly simple process actually involves a complex series of steps through all seven layers of the OSI model. When you select the video you want to watch and hit play in your browser, that request begins at the top layer of the OSI model, the Application Layer, and transmits the data down to the Physical Layer. The data from the server follows the same route back to your computer. In this scenario, each OSI layer performs a different function, allowing complex data communication processes to operate systematically and understandably.
What Are the 7 Layers of the OSI Model?
- Physical Layer: The lowest layer of the OSI model, the Physical Layer, is responsible for transmitting data in the form of bits over physical mediums (cables, radio frequencies, etc.). Data is carried in this layer by electrical signals, light waves, or radio waves. These operations, occurring at the hardware level, enable data to move through cables or wireless connections.
- Data Link Layer: This layer ensures the secure and error-free transmission of data sent over the Physical Layer. If collisions or errors occur during transmission, they are corrected at this layer. It also directs data transmission based on devices’ MAC addresses.
- Network Layer: Responsible for routing data packets from source to destination. It determines the best route using IP addresses and ensures that packets reach their correct destination.
- Transport Layer: This layer makes data transmission between two endpoints reliable. It ensures that data packets arrive in order and intact. If a packet is lost or corrupted, this layer detects and corrects the issue.
- Session Layer: This layer establishes, manages, and terminates sessions between two devices. These sessions ensure that data flows regularly and continuously.
- Presentation Layer: This layer ensures that data is transmitted in a suitable format between different devices. Data encryption, compression, and conversion into different formats occur in this layer.
- Application Layer: The highest layer of the OSI model, the Application Layer, includes applications that allow users to access the network and facilitate data exchange. Web browsers, email programs, and file-sharing tools operate at this layer, Data Transmission and Machine Learning with Client-Server Model.
Conclusion
Mastering Python for Ethical Hacking: A Comprehensive Guide to Building Hacking Tools
Let’s embark on this journey together, where you will learn to use Python not just as a programming language, but as a powerful weapon in the fight against cyber threats
-5% $15 on buymeacoffeeThe OSI model is a framework that clarifies data transmission in computer networks and is used to diagnose network issues. In this article, we thoroughly examined the seven layers of the OSI model and explained the functions of each layer with concrete examples. Understanding the OSI model helps to unravel the complex structure of networks and facilitates the detection of potential issues in network communication. This model enables network engineers and system administrators to manage network infrastructures more effectively.

It’s very interesting!
The scenario explaining how a video request travels through all the OSI layers is such a practical and helpful way to illustrate how the model works. Great job!
OSI ModelHow does the OSI model compare to the TCP/IP model in terms of practical usage today?
The OSI model is more of a conceptual framework, whereas the TCP/IP model is used in real-world networking. That said, the OSI model is still crucial for understanding and diagnosing complex networking issues because it breaks down the functions into more specific layers.