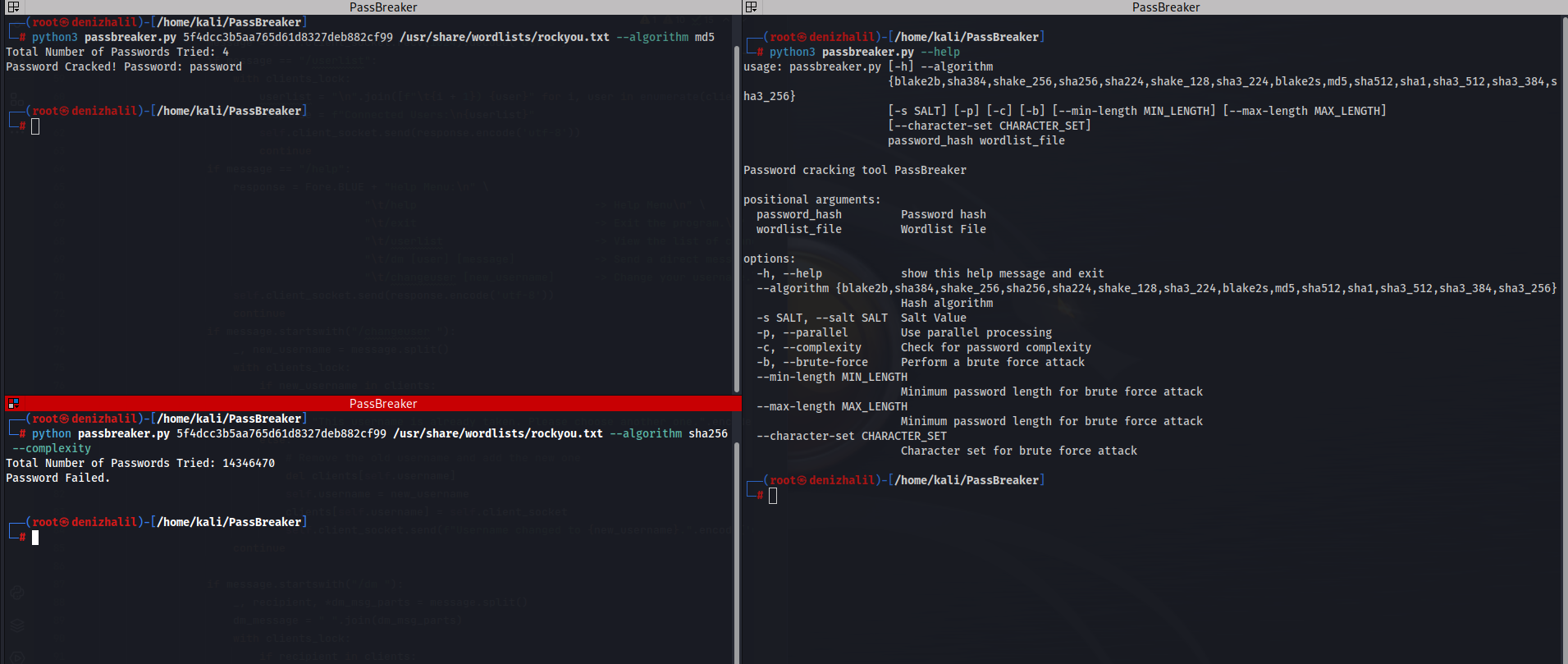
Brute Force Hash Cracker Using SHA-256 With Python
Introduction In today’s digital landscape, securing sensitive information is paramount. One of the most common methods for protecting passwords is through hashing, a technique that transforms plain text into a fixed-size string of characters. However, even the most secure hashes can be vulnerable to brute-force attacks, where an attacker systematically attempts every possible combination to find the original input. This article will