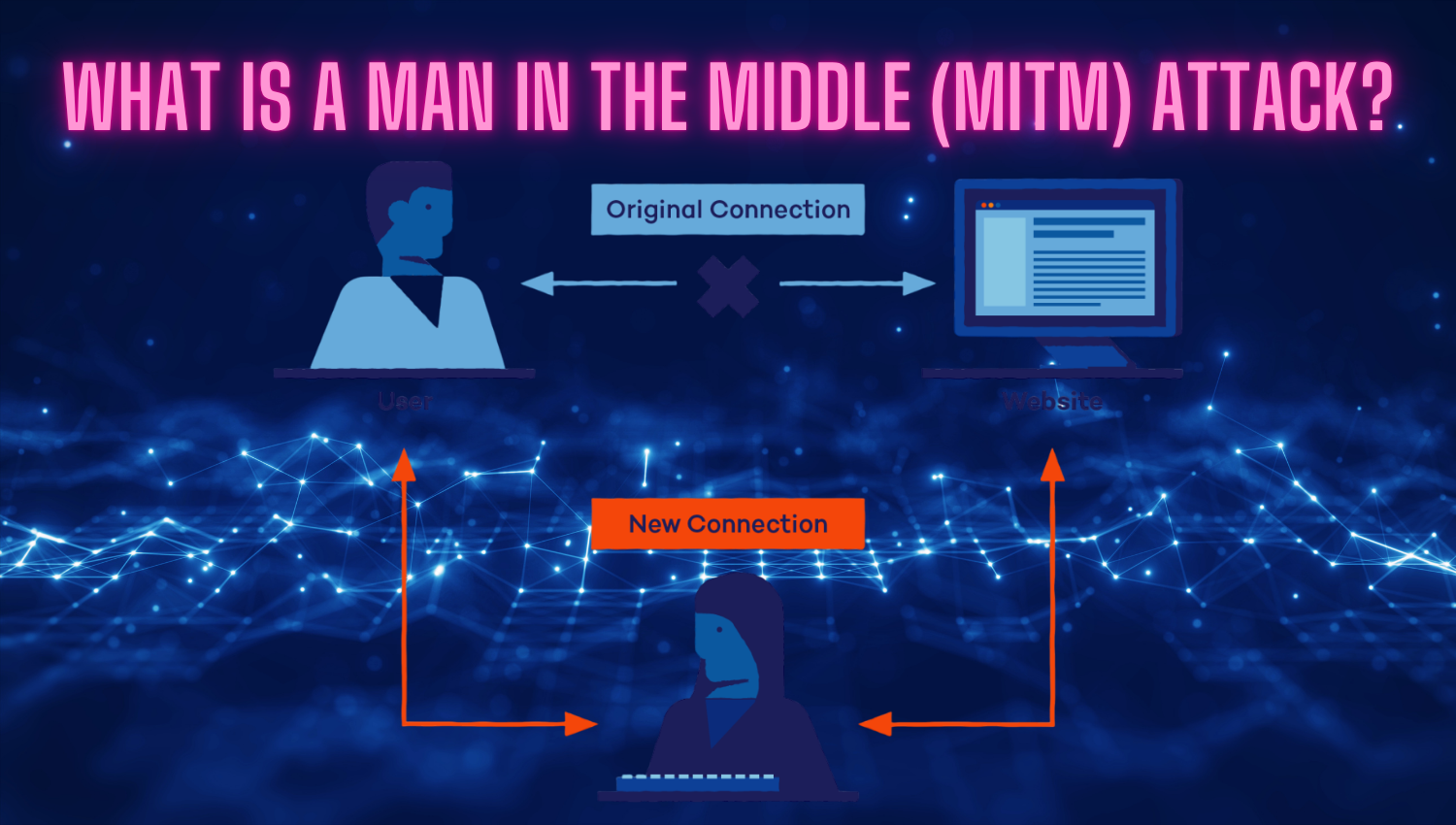
What is a Man-in-the-Middle (MITM) Attack?
Introduction In today’s interconnected digital environment, the security of our online communications is more crucial than ever. Every day, individuals and organizations exchange sensitive information—such as passwords, financial data, and private messages—across various digital platforms. As dependence on these technologies grows, so does the risk of cyber threats targeting the privacy and integrity of our data. One of the most significant and stealthy