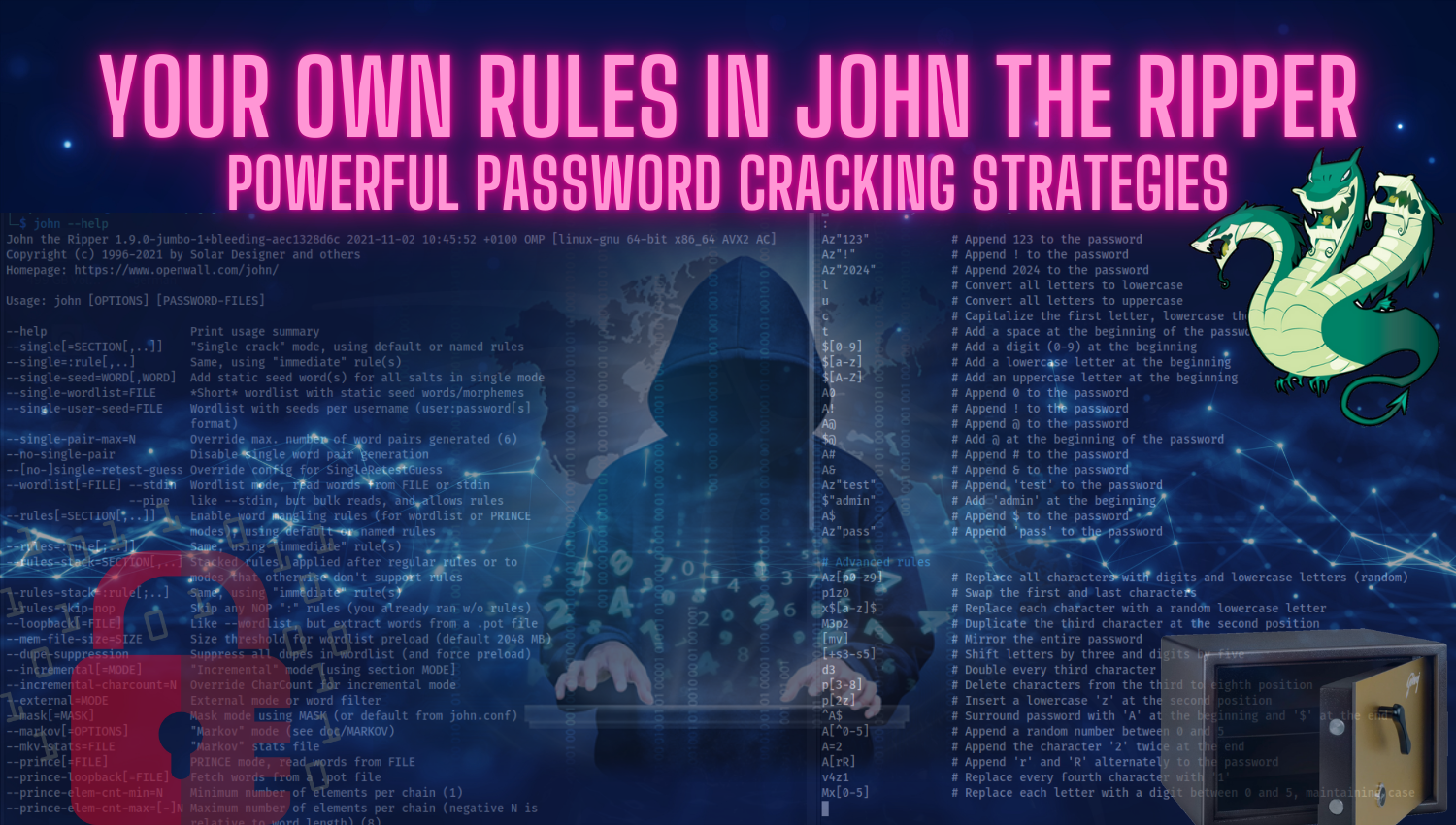
Writing Your Own Rules in John the Ripper
Introduction John the Ripper (JtR) is one of the most popular and powerful tools for password cracking. It can be used for both simple and complex password-cracking tasks. It’s especially useful for testing large password lists or cracking password hashes. However, using just the default wordlists may not always be enough. To deal with stronger, more complex passwords that have been protected with